Terralyp/SunloginLP-Eanalysis-tool
GitHub: Terralyp/SunloginLP-Eanalysis-tool
这是一个针对向日葵远程控制软件本地权限提升漏洞的安全研究与防御分析文档,提供漏洞原理讲解、检测指南和加固建议。
Stars: 1 | Forks: 0
```
# SunloginLPE – Sunlogin 本地权限提升研究
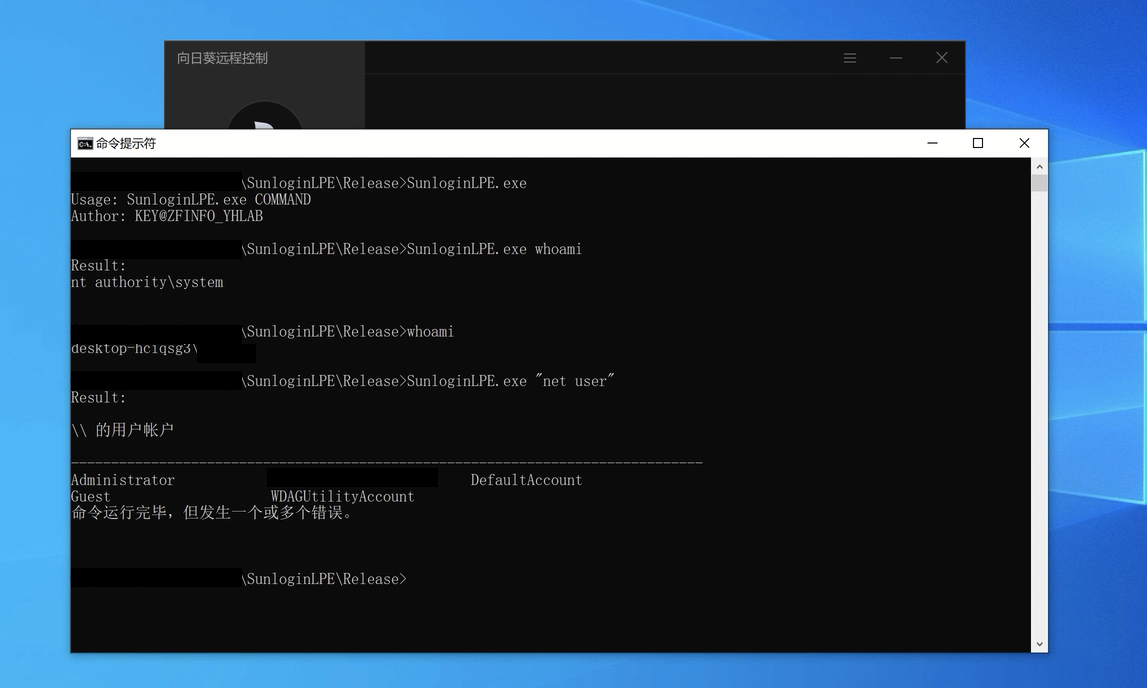
SunloginLPE is a **security research project** focused on analyzing the well-known Local Privilege Escalation vulnerability found in older versions of **Sunlogin Remote Control (Sunflower Remote Control)..**.
The goal of this repository is to provide **educational insight**, **defensive understanding**, and **technical analysis** of the underlying issue—without distributing harmful exploit code.
> ⚠️ This project is strictly for **research, detection, and educational purposes**.
> It does **not** include any working exploit, weaponized payloads, or instructions on abusing the vulnerability.
---
## 🔍 概述
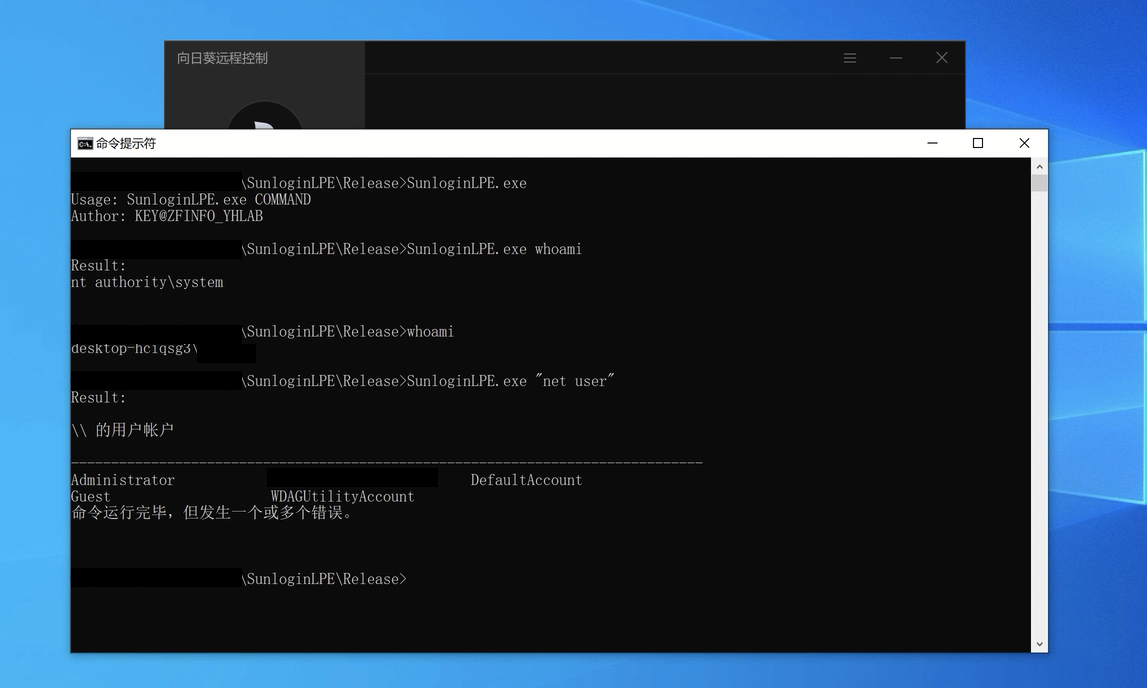 The Sunlogin LPE vulnerability became notable due to the ability for a local attacker to:
- Interact with the Sunlogin service,
- Abuse improper permission validations,
- And escalate privileges to SYSTEM on vulnerable builds.
This repository explains the **root cause**, demonstrates **safe reproduction in isolated lab environments**, and provides **guidance for defenders**.
---
## 🧠 项目包含内容
- ✔ Technical explanation of the Sunlogin LPE vulnerability
- ✔ Breakdown of the insecure logic path
- ✔ Packet/IPC behavior analysis
- ✔ Windows privilege escalation concepts
- ✔ Defensive recommendations
- ✔ Detection guidelines (EDR/SIEM)
- ✔ Patch and mitigation information
---
## ❌ 项目不包含内容
- ✘ No exploit code
- ✘ No weaponized PoC
- ✘ No steps for malicious usage
- ✘ No methods to bypass updated versions
- ✘ No binaries or automation tools
This is a **security analysis project**, not an exploitation toolkit.
---
## 🛡 防御视角
Security teams can use the documentation in this repository to:
- Identify vulnerable Sunlogin versions
- Monitor suspicious Sunlogin service activity
- Detect privilege abuse attempts
- Harden system configurations
- Validate whether mitigations are active
A dedicated *Defense* section describes IOC patterns, unusual log events, and telemetry recommendations.
---
## 📚 背景
The Sunlogin LPE issue originated from:
- Weak authorization validation in local API endpoints
- Privileged operations exposed without proper checks
- IPC interactions that allowed unintended elevation
Several versions were affected prior to vendor fixes.
---
## 🏷 标签
```
安全
信息安全
研究
windows-安全
权限提升
cve-分析
逆向工程
防御性安全
加固
文档
```
---
## 📄 许可证
This project is intended for **educational and research purposes only**.
Use responsibly and ethically.
---
If you find this analysis useful, feel free to contribute with additional detection ideas or documentation!
```
The Sunlogin LPE vulnerability became notable due to the ability for a local attacker to:
- Interact with the Sunlogin service,
- Abuse improper permission validations,
- And escalate privileges to SYSTEM on vulnerable builds.
This repository explains the **root cause**, demonstrates **safe reproduction in isolated lab environments**, and provides **guidance for defenders**.
---
## 🧠 项目包含内容
- ✔ Technical explanation of the Sunlogin LPE vulnerability
- ✔ Breakdown of the insecure logic path
- ✔ Packet/IPC behavior analysis
- ✔ Windows privilege escalation concepts
- ✔ Defensive recommendations
- ✔ Detection guidelines (EDR/SIEM)
- ✔ Patch and mitigation information
---
## ❌ 项目不包含内容
- ✘ No exploit code
- ✘ No weaponized PoC
- ✘ No steps for malicious usage
- ✘ No methods to bypass updated versions
- ✘ No binaries or automation tools
This is a **security analysis project**, not an exploitation toolkit.
---
## 🛡 防御视角
Security teams can use the documentation in this repository to:
- Identify vulnerable Sunlogin versions
- Monitor suspicious Sunlogin service activity
- Detect privilege abuse attempts
- Harden system configurations
- Validate whether mitigations are active
A dedicated *Defense* section describes IOC patterns, unusual log events, and telemetry recommendations.
---
## 📚 背景
The Sunlogin LPE issue originated from:
- Weak authorization validation in local API endpoints
- Privileged operations exposed without proper checks
- IPC interactions that allowed unintended elevation
Several versions were affected prior to vendor fixes.
---
## 🏷 标签
```
安全
信息安全
研究
windows-安全
权限提升
cve-分析
逆向工程
防御性安全
加固
文档
```
---
## 📄 许可证
This project is intended for **educational and research purposes only**.
Use responsibly and ethically.
---
If you find this analysis useful, feel free to contribute with additional detection ideas or documentation!
```
 The Sunlogin LPE vulnerability became notable due to the ability for a local attacker to:
- Interact with the Sunlogin service,
- Abuse improper permission validations,
- And escalate privileges to SYSTEM on vulnerable builds.
This repository explains the **root cause**, demonstrates **safe reproduction in isolated lab environments**, and provides **guidance for defenders**.
---
## 🧠 项目包含内容
- ✔ Technical explanation of the Sunlogin LPE vulnerability
- ✔ Breakdown of the insecure logic path
- ✔ Packet/IPC behavior analysis
- ✔ Windows privilege escalation concepts
- ✔ Defensive recommendations
- ✔ Detection guidelines (EDR/SIEM)
- ✔ Patch and mitigation information
---
## ❌ 项目不包含内容
- ✘ No exploit code
- ✘ No weaponized PoC
- ✘ No steps for malicious usage
- ✘ No methods to bypass updated versions
- ✘ No binaries or automation tools
This is a **security analysis project**, not an exploitation toolkit.
---
## 🛡 防御视角
Security teams can use the documentation in this repository to:
- Identify vulnerable Sunlogin versions
- Monitor suspicious Sunlogin service activity
- Detect privilege abuse attempts
- Harden system configurations
- Validate whether mitigations are active
A dedicated *Defense* section describes IOC patterns, unusual log events, and telemetry recommendations.
---
## 📚 背景
The Sunlogin LPE issue originated from:
- Weak authorization validation in local API endpoints
- Privileged operations exposed without proper checks
- IPC interactions that allowed unintended elevation
Several versions were affected prior to vendor fixes.
---
## 🏷 标签
```
安全
信息安全
研究
windows-安全
权限提升
cve-分析
逆向工程
防御性安全
加固
文档
```
---
## 📄 许可证
This project is intended for **educational and research purposes only**.
Use responsibly and ethically.
---
If you find this analysis useful, feel free to contribute with additional detection ideas or documentation!
```
The Sunlogin LPE vulnerability became notable due to the ability for a local attacker to:
- Interact with the Sunlogin service,
- Abuse improper permission validations,
- And escalate privileges to SYSTEM on vulnerable builds.
This repository explains the **root cause**, demonstrates **safe reproduction in isolated lab environments**, and provides **guidance for defenders**.
---
## 🧠 项目包含内容
- ✔ Technical explanation of the Sunlogin LPE vulnerability
- ✔ Breakdown of the insecure logic path
- ✔ Packet/IPC behavior analysis
- ✔ Windows privilege escalation concepts
- ✔ Defensive recommendations
- ✔ Detection guidelines (EDR/SIEM)
- ✔ Patch and mitigation information
---
## ❌ 项目不包含内容
- ✘ No exploit code
- ✘ No weaponized PoC
- ✘ No steps for malicious usage
- ✘ No methods to bypass updated versions
- ✘ No binaries or automation tools
This is a **security analysis project**, not an exploitation toolkit.
---
## 🛡 防御视角
Security teams can use the documentation in this repository to:
- Identify vulnerable Sunlogin versions
- Monitor suspicious Sunlogin service activity
- Detect privilege abuse attempts
- Harden system configurations
- Validate whether mitigations are active
A dedicated *Defense* section describes IOC patterns, unusual log events, and telemetry recommendations.
---
## 📚 背景
The Sunlogin LPE issue originated from:
- Weak authorization validation in local API endpoints
- Privileged operations exposed without proper checks
- IPC interactions that allowed unintended elevation
Several versions were affected prior to vendor fixes.
---
## 🏷 标签
```
安全
信息安全
研究
windows-安全
权限提升
cve-分析
逆向工程
防御性安全
加固
文档
```
---
## 📄 许可证
This project is intended for **educational and research purposes only**.
Use responsibly and ethically.
---
If you find this analysis useful, feel free to contribute with additional detection ideas or documentation!
```
标签:Conpot, EDR检测, IPC通信分析, LPE, Sunlogin, Web报告查看器, Windows安全, 协议分析, 向日葵远程控制, 教育科普, 本地权限提升, 本地验证工具, 权限提升, 漏洞分析, 漏洞复现, 漏洞缓解, 网络安全, 网页分析工具, 路径探测, 防御策略, 隐私保护