1r0nx/aletheia
GitHub: 1r0nx/aletheia
一款用于古典密码解码与暴力破解的命令行工具,帮助快速破解 CTF 和学习场景中的传统加密文本。
Stars: 0 | Forks: 0
# Aletheia
Aletheia 是一个命令行工具,旨在执行 **常见密码的解码或暴力破解攻击**。它帮助你利用几种经典密码技术快速测试和解密加密文本。
## 🧠 为什么选择 Aletheia?
**Aletheia** 这个名字源于希腊语,意为 *真理* 或 *去蔽*。该工具旨在揭示隐藏的信息,解开加密文本背后的真相。
## ✨ 功能特性
- 针对多种经典密码的暴力破解解密
- 简单直观的 CLI 界面
- 适用于 CTF、密码学学习和快速密码分析
支持的密码:
- xor
- atbash
- vigenere
- rail fence
- xor 暴力破解 (基于密钥长度)
- rot13 暴力破解
- rot47 暴力破解
- affine 暴力破解
- vigenere 暴力破解 (基于密钥长度)
- rail fence 暴力破解
## 🛠 系统要求
- Python3
- pyinstaller (如果你需要二进制文件)
## 📦 安装说明
克隆仓库并创建二进制文件:
```
sudo apt-get install python3 pyinstaller
git clone https://github.com/1r0nx/aletheia.git
cd aletheia
chmod +x build.sh
./build.sh
sudo cp dist/aletheia /usr/bin/
```
现在你可以像使用简单的 Linux 命令一样使用它了!
或者
克隆仓库并赋予脚本执行权限:
```
git clone https://github.com/1r0nx/aletheia.git
cd aletheia/src
chmod +x aletheia.py
./aletheia.py
```
### 全局帮助
```
❯ aletheia
##
:##: #### ## ##
## #### ## ## ##
#### ## ## ##
#### ## .####: ####### ##.#### .####: #### :####
:# #: ## .######: ####### ####### .######: #### ######
#::# ## ##: :## ## ### :## ##: :## ## #: :##
## ## ## ######## ## ## ## ######## ## :#####
###### ## ######## ## ## ## ######## ## .#######
.######. ## ## ## ## ## ## ## ## . ##
:## ##: ##: ###. :# ##. ## ## ###. :# ## ##: ###
### ### ##### .####### ##### ## ## .####### ######## ########
##: :## .#### .#####: .#### ## ## .#####: ######## ###.##
usage: aletheia [-h] {xor,atbash,vigenere,rail_fence,xor_brute,rot13_brute,rot47_brute,affine_brute,vigenere_brute,rail_fence_brute} ...
decode or brute force some substitution ciphers
positional arguments:
{xor,atbash,vigenere,rail_fence,xor_brute,rot13_brute,rot47_brute,affine_brute,vigenere_brute,rail_fence_brute}
xor decode xor cipher
atbash decode atbash cipher
vigenere decode vigenere cipher
rail_fence decode rail fence cipher
xor_brute brute force xor cipher
rot13_brute brute force rot13 cipher
rot47_brute brute force rot47 cipher
affine_brute brute force affine cipher
vigenere_brute brute force vigenere cipher
rail_fence_brute brute force rail fence cipher
options:
-h, --help show this help message and exit
```
## 🔓 密码模块
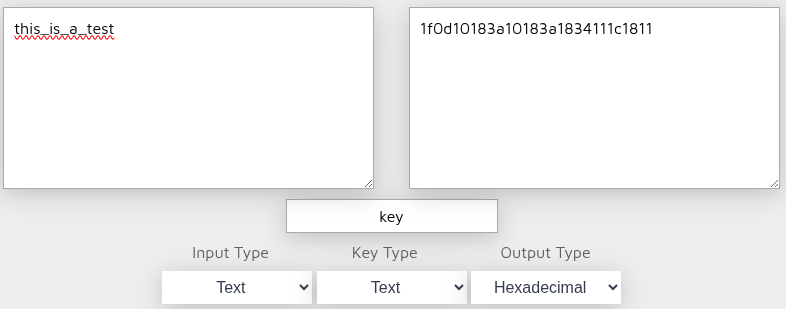
### -XOR
XOR 解码器
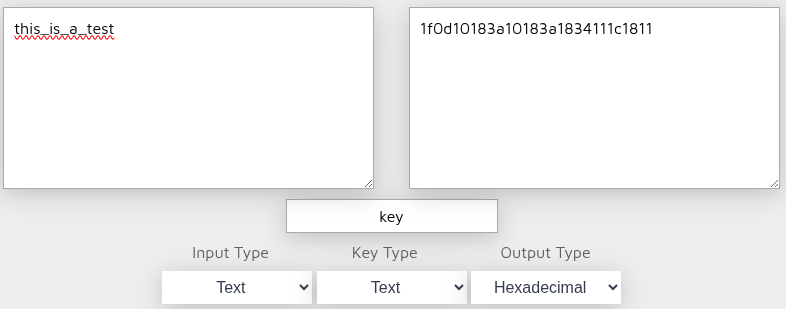
```
❯ aletheia xor -s "1f0d10183a10183a1834111c1811" -k key
XOR Result: this_is_a_test
```
```
❯ aletheia xor -s "1f0d10183a10183a1834111c1811" -k 6B6579
XOR Result: this_is_a_test
```
```
❯ ./aletheia.py xor -s "1f0d10183a10183a1834111c1811" -k '[107, 101, 121]'
XOR Result: this_is_a_test
```
注意:"[107, 101, 121]" 是 ascii 码中的 "key"
```
❯ aletheia xor -s "1f0d10183a10183a1834111c1811" -k "011010110110010101111001"
XOR Result: this_is_a_test
```
### -Atbash
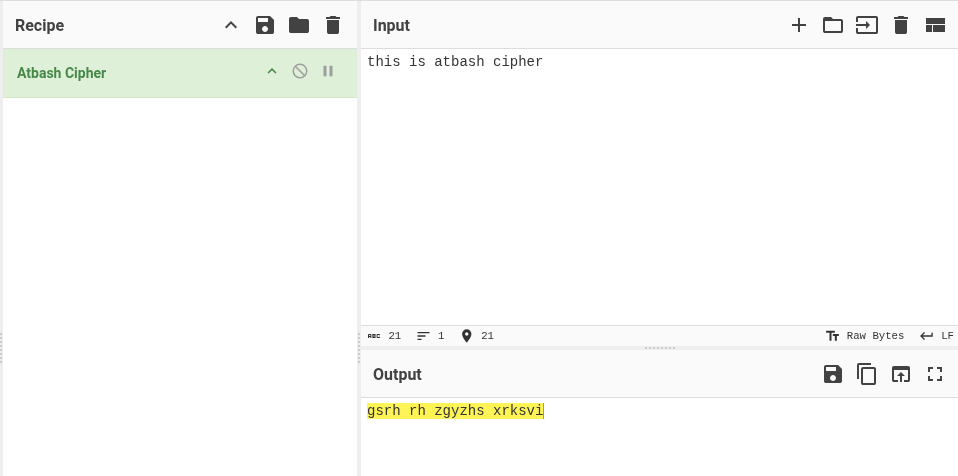
```
❯ aletheia atbash -s "gsrh rh zgyzhs xrksvi"
```
输出:
```
this is atbash cipher
```
### -Vigenère Cipher
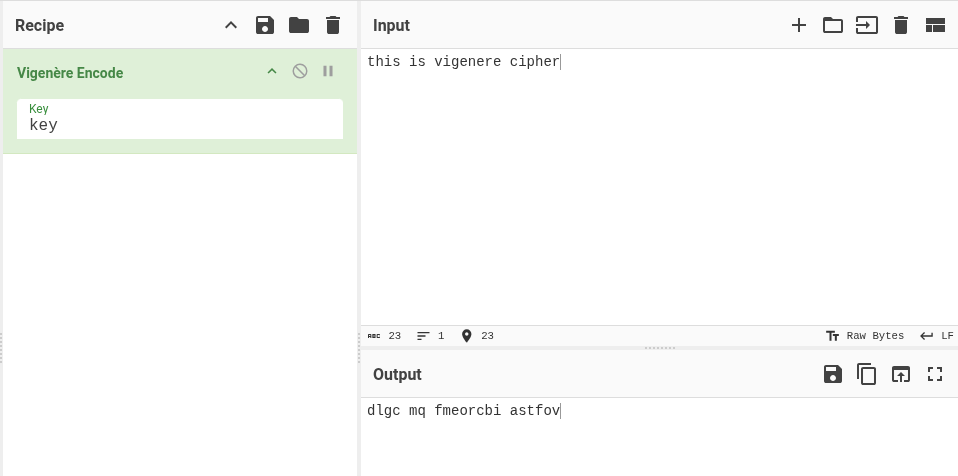
```
❯ aletheia vigenere -s "dlgc mq fmeorcbi astfov" -k key
```
输出:
```
this is vigenere cipher
```
### -Rail fence
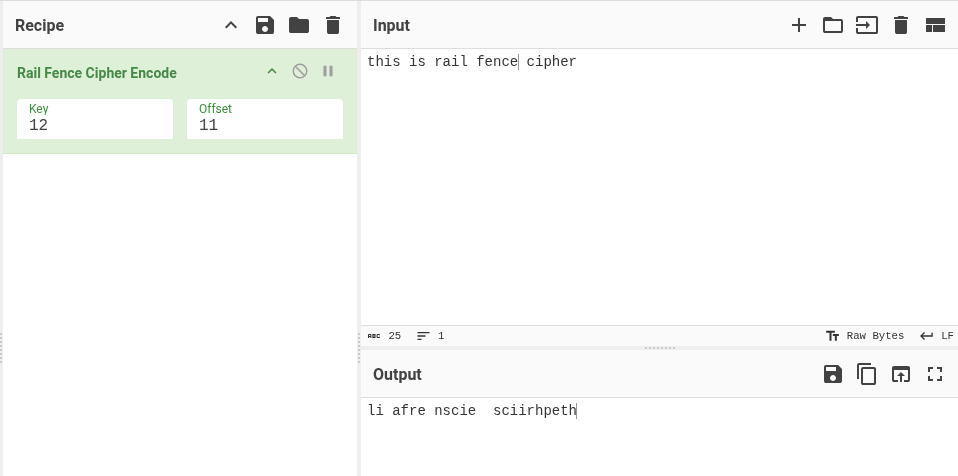
```
❯ aletheia rail_fence -s "li afre nscie sciirhpeth" -k 12 -o 11
```
输出:
```
this is rail fence cipher
```
### -XOR Brute force
基于密钥长度的 xor 暴力破解
```
❯ aletheia xor_brute -s "1f0d10183a10183a1834111c1811" -l 3 | grep key
```
输出:
```
[+] Total keys to test: 1,000,000
[+] Bruteforcing XOR keys of length 3...
101530 KEY = b'afu' -> b'~key\\ey\\mUwiyw'
...
201434 KEY = b'key' -> b'this_is_a_test'
....
923890 KEY = b'}C{' -> b'bNkeykeycIRgeR'
```
### -ROT13
暴力破解 ROT13 替换。
```
./aletheia.py rot13_brute -s "Uryyb Jbeyq"
```
输出:
```
0: Uryyb Jbeyq
...
...
13: Hello World
...
...
25: Tqxxa Iadxp
```
### -ROT47
暴力破解 ROT47 转换。
```
./aletheia.py rot47_brute -s "w6==@ (@C=5P"
```
输出:
```
0: w6==@ (@C=5P
...
...
47: Hello World!
...
...
93: v5< Fwrra Yajrt
a = 1, b = 1 -> Evqqz Xziqs
...
...
a = 9, b = 10 -> Hello World
...
...
a = 25, b = 24 -> Tchhy Ayphf
a = 25, b = 25 -> Udiiz Bzqig
```
### -Vigenère Bruteforce
根据提供的长度暴力破解可能的密钥。1 < len(key) < 5。
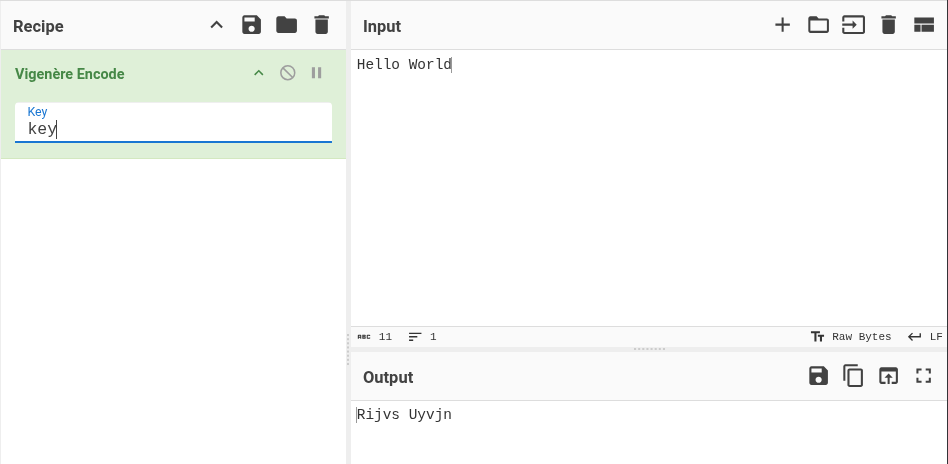
```
./aletheia.py vigenere_brute -s "Rijvs Uyvjn" -l 3
```
输出:
```
[+] Test of 17576 possible keys...
[possible_key=aaa] Rijvs Uyvjn
[possible_key=aab] Riivs Tyvin
...
...
[possible_key=key] Hello World
...
...
[possible_key=zzy] Sjlwt Wzwlo
[possible_key=zzz] Sjkwt Vzwko
```
### -Rail Fence Cipher Brute force
测试各种栏数 (rail counts) 和偏移量 (offset)。
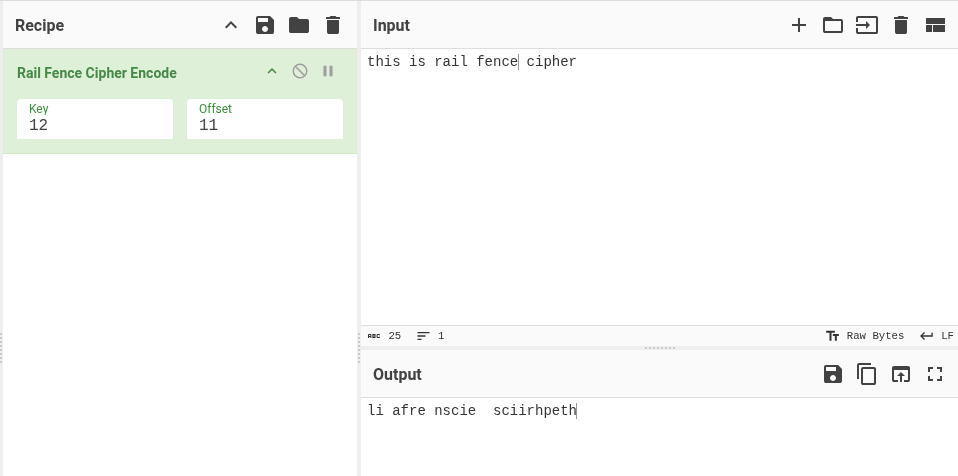
```
aletheia rail_fence_brute -s "li afre nscie sciirhpeth"
```
输出:
```
key = 002 | period = 000 || output = l i sacfirier hnpsectihe
key = 002 | period = 001 || output = el i sacfirier hnpsectih
...
...
key = 012 | period = 011 || output = this is rail fence cipher
...
...
key = 024 | period = 044 || output = ail fre nscie sciirhpeth
key = 024 | period = 045 || output = il afre nscie sciirhpeth
```
## 📜 许可证
MIT 许可证。
## 🤝 贡献
欢迎贡献或提出建议!随时欢迎提交 issue 或 pull request。
标签:CTF工具, PoC, Python, 凯撒密码, 古典密码, 密码学, 异或密码, 手动系统调用, 数据解码, 文档结构分析, 无后门, 暴力破解, 栅栏密码, 漏洞挖掘, 漏洞搜索, 用户模式钩子绕过, 维吉尼亚密码, 编码转换, 解密工具