trmxvibs/NetSentry-Framework
GitHub: trmxvibs/NetSentry-Framework
集成了多线程扫描引擎的自动化侦察与漏洞评估框架,提供 Web 控制台和 CLI 两种操作方式。
Stars: 2 | Forks: 0
# 🛡️ NET-SENTRY 框架


















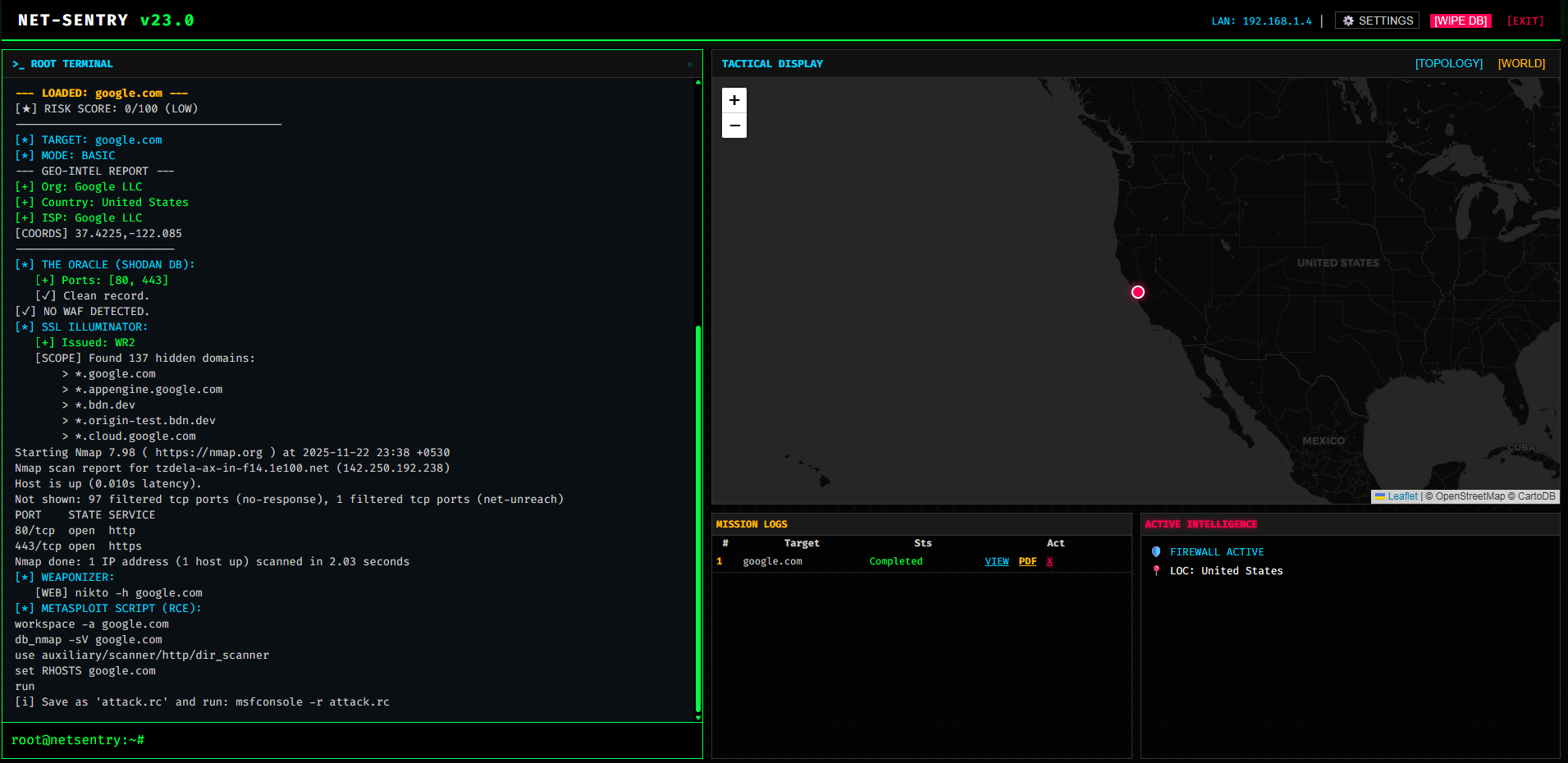
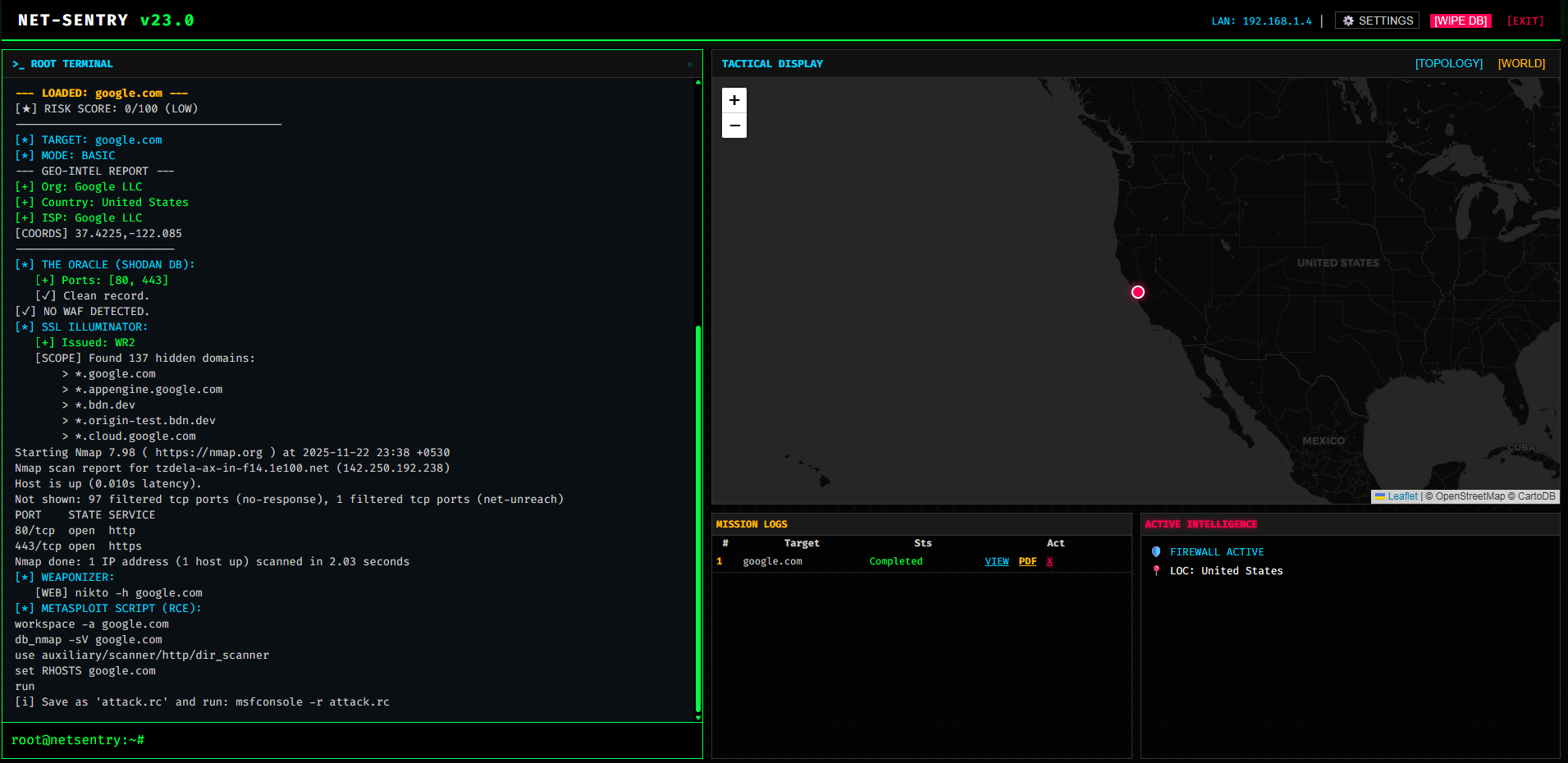
**Net-Sentry** 是一个军事级的攻击性安全框架,旨在自动化侦察和漏洞评估阶段。它通过一个 **统一命令控制台** 取代了繁琐的手动工作,让安全研究人员能够专注于策略制定,而由 AI 负责执行。
如今,Net-Sentry 由 **并发扫描引擎** 驱动,能够以 15 倍的速度提供深度情报、云分析和可操作的报告。
## 主要特性
Net-Sentry 采用模块化架构,在杀伤链的每个阶段部署专门的引擎。
### 1. 主动情报与 AI
* **The Oracle:** 查询 **Shodan/InternetDB** 以获取缓存的开放端口和 CVE 信息,而无需向目标发送主动数据包。
* **Tech Stack Detective:** 识别服务器技术(CMS、Frameworks、WAFs)以定制攻击策略。
### 2. 深度侦察
* **多线程扫描:** 同时运行 Nmap、SSL 和 Spider 模块,以获得超高速结果。
* **地理战术追踪:** 在世界地图上可视化目标服务器的实时 **卫星地理位置**。
* **拓扑映射器:** 在交互式图表中可视化网络节点、端口和攻击向量。
* **子域名间谍:** 通过 Certificate Transparency 日志进行被动子域名枚举。
### 3. 攻击能力
* **The Key Reaper:** 抓取 HTML 和 JavaScript 文件,以收集泄露的 **API Keys**(Google、AWS、Stripe)和隐藏的端点。
* **WAF Detector & Bypass:** 识别防火墙(Cloudflare/AWS)并尝试使用头部投毒技术绕过 403 限制。
* **Directory Buster:** 暴力破解隐藏路径(`/admin`、`/.env`、`/backup`)以查找暴露的面板。
### 4. 分析与界面
* **实时终端:** 浏览器内功能齐全的命令行界面。
* **执行报告:** 生成按模块分类的专业 PDF 报告,便于交付给客户。
* **系统桥接:** 直接从仪表板执行主机 OS 命令。
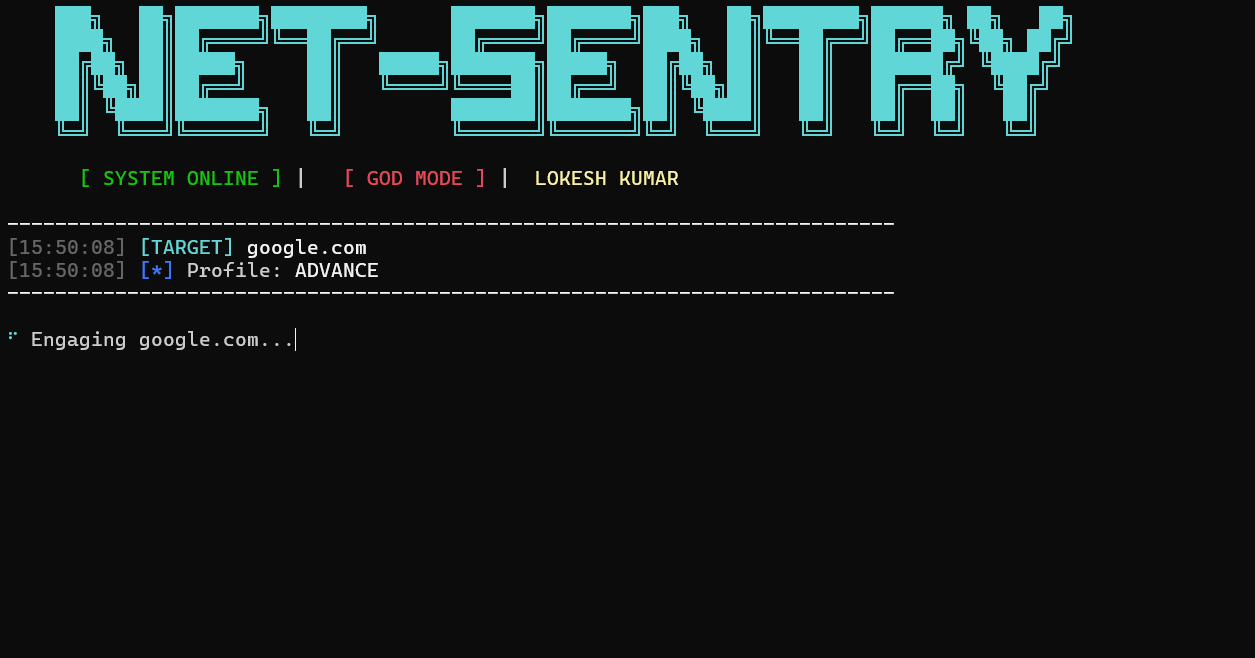
## 视觉画廊
[](https://github.com/trmxvibs/Net-Sentry/actions/workflows/daily_update.yml)
 ## 前置条件
在部署 Net-Sentry 之前,请确保您的系统满足以下要求。
### 1. 核心引擎
* **Python 3.8+**: 框架的基石。
* **Nmap**: 端口扫描和服务检测的基础。
* *Windows:* [下载安装程序](https://nmap.org/download.html)
* *Linux:* `sudo apt install nmap`
* *MacOS:* `brew install nmap`
### 2. 攻击工具(可选但推荐)
* **Metasploit Framework**: 执行自动生成的 `.rc` 攻击脚本所需。
* *Kali Linux:* 预装。
* *Windows:* [下载 Metasploit](https://windows.metasploit.com/)
### 3. 浏览器支持
* **现代网络浏览器**: Chrome、Firefox 或 Edge(可视化拓扑地图和实时终端所需)。
## 安装说明
### 构建技术





## 前置条件
在部署 Net-Sentry 之前,请确保您的系统满足以下要求。
### 1. 核心引擎
* **Python 3.8+**: 框架的基石。
* **Nmap**: 端口扫描和服务检测的基础。
* *Windows:* [下载安装程序](https://nmap.org/download.html)
* *Linux:* `sudo apt install nmap`
* *MacOS:* `brew install nmap`
### 2. 攻击工具(可选但推荐)
* **Metasploit Framework**: 执行自动生成的 `.rc` 攻击脚本所需。
* *Kali Linux:* 预装。
* *Windows:* [下载 Metasploit](https://windows.metasploit.com/)
### 3. 浏览器支持
* **现代网络浏览器**: Chrome、Firefox 或 Edge(可视化拓扑地图和实时终端所需)。
## 安装说明
### 构建技术






   
按照以下步骤在本地机器或 VPS 上部署该框架。
### 1. 克隆仓库
从 GitHub 获取最新源代码。
```
git clone https://github.com/trmxvibs/NetSentry-Framework
cd NetSentry-Framework
```
### 2. 安装依赖
安装所需的 Python 库(Flask、Requests、Vis.js 支持等)。
```
pip install -r requirements.txt
```
### 3. 初始化神经核心(数据库)
运行设置脚本以创建 SQLite 数据库和默认管理员用户。
```
python database_setup.py
```
### **成功检查:** 您应该看到以下消息:
[+] Default User Created: lokesh/lokesh
- 默认用户/密码 ==> lokesh/lokesh
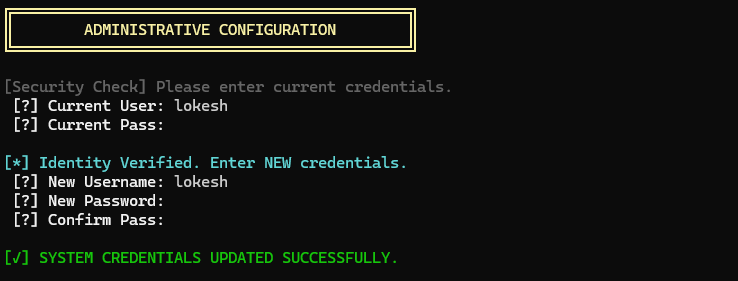
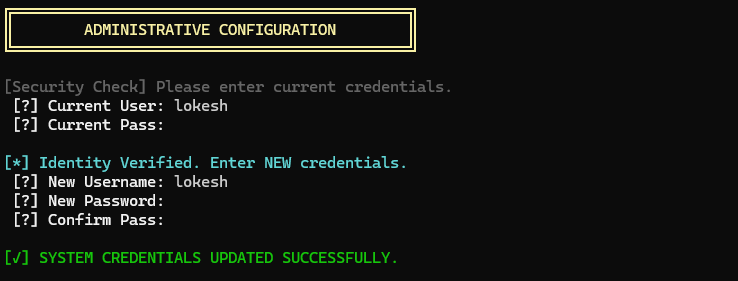
## 修改您的登录数据
```
python cli_tool.py --config
```
 ## 显示帮助菜单
```
python cli_tool.py -h
```
```
usage: cli_tool.py [-h] [-t TARGET] [-m {basic,medium,advance,custom}] [--flags FLAGS] [-o] [--config]
Net-Sentry Professional CLI
options:
-h, --help show this help message and exit
-t, --target TARGET Target IP or Domain
-m, --mode {basic,medium,advance,custom}
Scan Profile
--flags FLAGS Custom Nmap Flags
-o, --output Save report to file
--config Reset Admin Username/Password
```
## 用法:Web 命令控制台 (GUI)
### 1. 启动系统
启动 Web 服务器:
```
python app.py
```
### 控制台输出:[+] Net-Sentry Online. Access: http://127.0.0.1:(port)
### 2. 访问与登录
打开浏览器并导航至 http://127.0.0.1:(port)
默认用户名:`lokesh`
默认密码:`lokesh`
**安全提示:请立即使用仪表板标题中的 ⚙️ SETTINGS 按钮更改您的密码。**
### 3. 仪表板操作
实时终端:直接在浏览器控制台中输入命令。
scan google.com advance (启动全频谱扫描)
man nmap (查看速查表)
ping 8.8.8.8 (执行系统命令)
`战术地图:使用右上角面板中的按钮在 [TOPO] (网络图) 和 [WORLD] (地理地图) 之间切换。`
情报:在 "Active Intel" 框中查看实时 WAF 状态、CVE 警报和收集到的密钥。
`报告:点击 Mission Logs 表格中的 PDF 按钮下载专业的客户报告。`
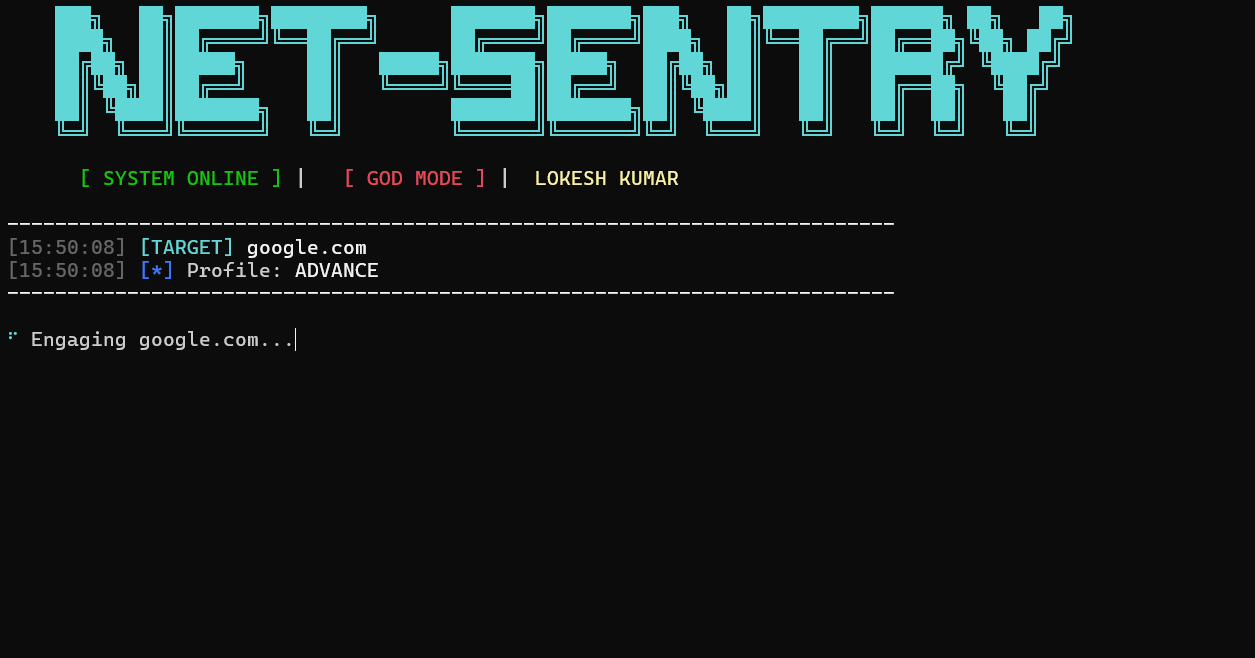
## 用法:CLI 工具 (终端)
对于喜欢无头环境或需要将 Net-Sentry 集成到自动化管道中的安全研究人员,CLI 工具提供了完整的功能。
### 1. 基础扫描(快速)
执行快速端口扫描和基础情报收集。
```
python cli_tool.py -t example.com
```
### 2. 高级模式(全功率)
激活所有引擎,包括 Fuzzing、Spidering、Zone Transfer 和漏洞检查。
```
python cli_tool.py -t example.com -m advance
```
### 3. 自定义操作
定义您自己的 Nmap 标志以进行特定目标扫描。
```
python cli_tool.py -t example.com -m custom --flags "-p 80,443,8080 -sV --script=vuln"
```
### 4. 保存输出
将扫描结果保存到文本文件中以供归档。
```
python cli_tool.py -t example.com -m medium -o
```
## 显示帮助菜单
```
python cli_tool.py -h
```
```
usage: cli_tool.py [-h] [-t TARGET] [-m {basic,medium,advance,custom}] [--flags FLAGS] [-o] [--config]
Net-Sentry Professional CLI
options:
-h, --help show this help message and exit
-t, --target TARGET Target IP or Domain
-m, --mode {basic,medium,advance,custom}
Scan Profile
--flags FLAGS Custom Nmap Flags
-o, --output Save report to file
--config Reset Admin Username/Password
```
## 用法:Web 命令控制台 (GUI)
### 1. 启动系统
启动 Web 服务器:
```
python app.py
```
### 控制台输出:[+] Net-Sentry Online. Access: http://127.0.0.1:(port)
### 2. 访问与登录
打开浏览器并导航至 http://127.0.0.1:(port)
默认用户名:`lokesh`
默认密码:`lokesh`
**安全提示:请立即使用仪表板标题中的 ⚙️ SETTINGS 按钮更改您的密码。**
### 3. 仪表板操作
实时终端:直接在浏览器控制台中输入命令。
scan google.com advance (启动全频谱扫描)
man nmap (查看速查表)
ping 8.8.8.8 (执行系统命令)
`战术地图:使用右上角面板中的按钮在 [TOPO] (网络图) 和 [WORLD] (地理地图) 之间切换。`
情报:在 "Active Intel" 框中查看实时 WAF 状态、CVE 警报和收集到的密钥。
`报告:点击 Mission Logs 表格中的 PDF 按钮下载专业的客户报告。`
## 用法:CLI 工具 (终端)
对于喜欢无头环境或需要将 Net-Sentry 集成到自动化管道中的安全研究人员,CLI 工具提供了完整的功能。
### 1. 基础扫描(快速)
执行快速端口扫描和基础情报收集。
```
python cli_tool.py -t example.com
```
### 2. 高级模式(全功率)
激活所有引擎,包括 Fuzzing、Spidering、Zone Transfer 和漏洞检查。
```
python cli_tool.py -t example.com -m advance
```
### 3. 自定义操作
定义您自己的 Nmap 标志以进行特定目标扫描。
```
python cli_tool.py -t example.com -m custom --flags "-p 80,443,8080 -sV --script=vuln"
```
### 4. 保存输出
将扫描结果保存到文本文件中以供归档。
```
python cli_tool.py -t example.com -m medium -o
```
 **提示:CLI 工具使用与 Web 仪表板完全相同的引擎,确保各接口间结果的一致性。**
# 结果
```
███╗ ██╗███████╗████████╗ ███████╗███████╗███╗ ██╗████████╗██████╗ ██╗ ██╗
████╗ ██║██╔════╝╚══██╔══╝ ██╔════╝██╔════╝████╗ ██║╚══██╔══╝██╔══██╗╚██╗ ██╔╝
██╔██╗ ██║█████╗ ██║ █████╗███████╗█████╗ ██╔██╗ ██║ ██║ ██████╔╝ ╚████╔╝
██║╚██╗██║██╔══╝ ██║ ╚════╝╚════██║██╔══╝ ██║╚██╗██║ ██║ ██╔══██╗ ╚██╔╝
██║ ╚████║███████╗ ██║ ███████║███████╗██║ ╚████║ ██║ ██║ ██║ ██║
╚═╝ ╚═══╝╚══════╝ ╚═╝ ╚══════╝╚══════╝╚═╝ ╚═══╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝
[ SYSTEM ONLINE ] | [ GOD MODE ] | LOKESH KUMAR
--------------------------------------------------------------------------
[10:25:41] [TARGET] google.com
[10:25:41] [*] Profile: ADVANCE
--------------------------------------------------------------------------
⠴ Engaging google.com...
⠇ Engaging google.com...
[★] RISK SCORE: 85/100 (CRITICAL)
----------------------------------------
[*] TARGET: google.com
[*] MODE: ADVANCE
--- GEO-INTEL REPORT ---
[+] Org: Google LLC
[+] Country: Singapore (SG)
[+] ISP: Google LLC
[COORDS] 1.35208,103.82
------------------------
[*] THE ORACLE (SHODAN DB):
[+] Ports: [80, 443]
[✓] Clean record.
[✓] NO WAF DETECTED.
[*] SSL ILLUMINATOR:
[+] Issued: WR2
[SCOPE] Found 136 hidden domains:
> *.google.com
> *.appengine.google.com
> *.bdn.dev
> *.origin-test.bdn.dev
> *.cloud.google.com
> *.crowdsource.google.com
> *.datacompute.google.com
> *.google.ca
> *.google.cl
> *.google.co.in
...and 126 more.
[*] PASSIVE SUBDOMAINS:
[-] Passive recon failed: HTTPSConnectionPool(host='crt.sh', port=443): Read timed out. (read timeout=20)
[*] ACTIVE SUBDOMAIN DISCOVERY:
[⚡] Discovered 11 HIDDEN active subdomains:
> www.google.com
> mail.google.com
> blog.google.com
> ns1.google.com
> ns2.google.com
> smtp.google.com
> vpn.google.com
> m.google.com
> shop.google.com
> admin.google.com
> api.google.com
[*] DNS ZONE TRANSFER:
[✓] DNS Secure.
[-] CRITICAL: Nmap is not installed on the server. Please install it.
[*] DEEP VULNERABILITY SCAN (LFI/CONFIG):
[✓] No config backups exposed.
[✓] LFI check passed.
[*] DIRECTORY BUSTER:
[200] FOUND: /robots.txt
[*] CMS HUNTER (WORDPRESS):
[✓] WP API secure or not WordPress.
[*] GIT SOURCE HUNTER:
[✓] .git is secure.
[*] SPRING BOOT ACTUATOR SCAN:
[✓] Spring Boot Actuators secured.
[*] BROKEN LINK HIJACKING:
[-] BLH check failed.
[*] FIREBASE DATABASE HUNTER:
[✓] No open Firebase databases found.
[*] MOBILE APP ASSET SCANNER:
[+] Found Mobile Config: /apple-app-site-association
[⚠️] LEAK: Internal domains found in /apple-app-site-association
[*] HOST HEADER INJECTION:
[-] Host injection check failed.
[*] CRLF INJECTION (HEADER SPLITTING):
[✓] Header Splitting protected.
[*] CORS CONFIG CHECK:
[✓] CORS policy secure.
[*] CLICKJACKING CHECK:
[✓] Protected against Clickjacking.
[*] PROTOTYPE POLLUTION FUZZER:
[-] Pollution check failed.
[*] DESERIALIZATION SCAN:
[✓] No serialized objects found in cookies.
[*] VERB TAMPERING:
[✓] Verbs restricted.
[*] HTTP REQUEST SMUGGLING (CL.TE/TE.CL):
[✓] No smuggling anomalies detected.
[*] WEBSOCKET SECURITY (CSWSH):
[✓] No open WebSocket found.
[*] API RATE LIMIT BYPASS:
[✓] Rate limiting appears robust (or not triggered).
[*] GRAPHQL INSPECTOR:
[*] WEB CACHE POISONING DETECTOR:
[✓] Cache headers appear secure.
[*] JS MINER & DOM HUNTER:
[$$$] KEY LEAK (Google): AIzaSyBm7NubC-Swn1nt2nhYfxb58eCdmL2vCVU
└── Found in: Main HTML
└── STATUS: [SAFE] Restricted/Inactive
[i] Analyzing 2 JavaScript files...
[$$$] KEY LEAK (AWS): AKIABAAABJIBJJJJRJJJ
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [i] No auto-validation available.
[$$$] KEY LEAK (Google): AIzaSyBwQcjgmXUAsw5r4FZXO5t8_EZ_aUm_TGE
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'eval(' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.search' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.hash' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[$$$] KEY LEAK (Google): AIzaSyCbsbvGCe7C9mCtdaTycZB2eUFuzsYKG_E
└── Found in: rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
[+] Found 37 crawlable endpoints.
[*] API ZOMBIE (LOGIC HUNTER):
[☠️] CONFIRMED BOLA/IDOR: http://google.com/history/optout?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 97% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/advanced_search?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 88% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/preferences?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 96% (Valid Data Structure)
[*] DOM EXPLOIT SUGGESTIONS for innerHTML:
[i] Manual Verification Required. Try these in Browser:
> http://google.com#
**提示:CLI 工具使用与 Web 仪表板完全相同的引擎,确保各接口间结果的一致性。**
# 结果
```
███╗ ██╗███████╗████████╗ ███████╗███████╗███╗ ██╗████████╗██████╗ ██╗ ██╗
████╗ ██║██╔════╝╚══██╔══╝ ██╔════╝██╔════╝████╗ ██║╚══██╔══╝██╔══██╗╚██╗ ██╔╝
██╔██╗ ██║█████╗ ██║ █████╗███████╗█████╗ ██╔██╗ ██║ ██║ ██████╔╝ ╚████╔╝
██║╚██╗██║██╔══╝ ██║ ╚════╝╚════██║██╔══╝ ██║╚██╗██║ ██║ ██╔══██╗ ╚██╔╝
██║ ╚████║███████╗ ██║ ███████║███████╗██║ ╚████║ ██║ ██║ ██║ ██║
╚═╝ ╚═══╝╚══════╝ ╚═╝ ╚══════╝╚══════╝╚═╝ ╚═══╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝
[ SYSTEM ONLINE ] | [ GOD MODE ] | LOKESH KUMAR
--------------------------------------------------------------------------
[10:25:41] [TARGET] google.com
[10:25:41] [*] Profile: ADVANCE
--------------------------------------------------------------------------
⠴ Engaging google.com...
⠇ Engaging google.com...
[★] RISK SCORE: 85/100 (CRITICAL)
----------------------------------------
[*] TARGET: google.com
[*] MODE: ADVANCE
--- GEO-INTEL REPORT ---
[+] Org: Google LLC
[+] Country: Singapore (SG)
[+] ISP: Google LLC
[COORDS] 1.35208,103.82
------------------------
[*] THE ORACLE (SHODAN DB):
[+] Ports: [80, 443]
[✓] Clean record.
[✓] NO WAF DETECTED.
[*] SSL ILLUMINATOR:
[+] Issued: WR2
[SCOPE] Found 136 hidden domains:
> *.google.com
> *.appengine.google.com
> *.bdn.dev
> *.origin-test.bdn.dev
> *.cloud.google.com
> *.crowdsource.google.com
> *.datacompute.google.com
> *.google.ca
> *.google.cl
> *.google.co.in
...and 126 more.
[*] PASSIVE SUBDOMAINS:
[-] Passive recon failed: HTTPSConnectionPool(host='crt.sh', port=443): Read timed out. (read timeout=20)
[*] ACTIVE SUBDOMAIN DISCOVERY:
[⚡] Discovered 11 HIDDEN active subdomains:
> www.google.com
> mail.google.com
> blog.google.com
> ns1.google.com
> ns2.google.com
> smtp.google.com
> vpn.google.com
> m.google.com
> shop.google.com
> admin.google.com
> api.google.com
[*] DNS ZONE TRANSFER:
[✓] DNS Secure.
[-] CRITICAL: Nmap is not installed on the server. Please install it.
[*] DEEP VULNERABILITY SCAN (LFI/CONFIG):
[✓] No config backups exposed.
[✓] LFI check passed.
[*] DIRECTORY BUSTER:
[200] FOUND: /robots.txt
[*] CMS HUNTER (WORDPRESS):
[✓] WP API secure or not WordPress.
[*] GIT SOURCE HUNTER:
[✓] .git is secure.
[*] SPRING BOOT ACTUATOR SCAN:
[✓] Spring Boot Actuators secured.
[*] BROKEN LINK HIJACKING:
[-] BLH check failed.
[*] FIREBASE DATABASE HUNTER:
[✓] No open Firebase databases found.
[*] MOBILE APP ASSET SCANNER:
[+] Found Mobile Config: /apple-app-site-association
[⚠️] LEAK: Internal domains found in /apple-app-site-association
[*] HOST HEADER INJECTION:
[-] Host injection check failed.
[*] CRLF INJECTION (HEADER SPLITTING):
[✓] Header Splitting protected.
[*] CORS CONFIG CHECK:
[✓] CORS policy secure.
[*] CLICKJACKING CHECK:
[✓] Protected against Clickjacking.
[*] PROTOTYPE POLLUTION FUZZER:
[-] Pollution check failed.
[*] DESERIALIZATION SCAN:
[✓] No serialized objects found in cookies.
[*] VERB TAMPERING:
[✓] Verbs restricted.
[*] HTTP REQUEST SMUGGLING (CL.TE/TE.CL):
[✓] No smuggling anomalies detected.
[*] WEBSOCKET SECURITY (CSWSH):
[✓] No open WebSocket found.
[*] API RATE LIMIT BYPASS:
[✓] Rate limiting appears robust (or not triggered).
[*] GRAPHQL INSPECTOR:
[*] WEB CACHE POISONING DETECTOR:
[✓] Cache headers appear secure.
[*] JS MINER & DOM HUNTER:
[$$$] KEY LEAK (Google): AIzaSyBm7NubC-Swn1nt2nhYfxb58eCdmL2vCVU
└── Found in: Main HTML
└── STATUS: [SAFE] Restricted/Inactive
[i] Analyzing 2 JavaScript files...
[$$$] KEY LEAK (AWS): AKIABAAABJIBJJJJRJJJ
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [i] No auto-validation available.
[$$$] KEY LEAK (Google): AIzaSyBwQcjgmXUAsw5r4FZXO5t8_EZ_aUm_TGE
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'eval(' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.search' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.hash' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[$$$] KEY LEAK (Google): AIzaSyCbsbvGCe7C9mCtdaTycZB2eUFuzsYKG_E
└── Found in: rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
[+] Found 37 crawlable endpoints.
[*] API ZOMBIE (LOGIC HUNTER):
[☠️] CONFIRMED BOLA/IDOR: http://google.com/history/optout?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 97% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/advanced_search?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 88% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/preferences?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 96% (Valid Data Structure)
[*] DOM EXPLOIT SUGGESTIONS for innerHTML:
[i] Manual Verification Required. Try these in Browser:
> http://google.com# > http://google.com?q=
> http://google.com?q=
 ## 前置条件
在部署 Net-Sentry 之前,请确保您的系统满足以下要求。
### 1. 核心引擎
* **Python 3.8+**: 框架的基石。
* **Nmap**: 端口扫描和服务检测的基础。
* *Windows:* [下载安装程序](https://nmap.org/download.html)
* *Linux:* `sudo apt install nmap`
* *MacOS:* `brew install nmap`
### 2. 攻击工具(可选但推荐)
* **Metasploit Framework**: 执行自动生成的 `.rc` 攻击脚本所需。
* *Kali Linux:* 预装。
* *Windows:* [下载 Metasploit](https://windows.metasploit.com/)
### 3. 浏览器支持
* **现代网络浏览器**: Chrome、Firefox 或 Edge(可视化拓扑地图和实时终端所需)。
## 安装说明
### 构建技术





## 前置条件
在部署 Net-Sentry 之前,请确保您的系统满足以下要求。
### 1. 核心引擎
* **Python 3.8+**: 框架的基石。
* **Nmap**: 端口扫描和服务检测的基础。
* *Windows:* [下载安装程序](https://nmap.org/download.html)
* *Linux:* `sudo apt install nmap`
* *MacOS:* `brew install nmap`
### 2. 攻击工具(可选但推荐)
* **Metasploit Framework**: 执行自动生成的 `.rc` 攻击脚本所需。
* *Kali Linux:* 预装。
* *Windows:* [下载 Metasploit](https://windows.metasploit.com/)
### 3. 浏览器支持
* **现代网络浏览器**: Chrome、Firefox 或 Edge(可视化拓扑地图和实时终端所需)。
## 安装说明
### 构建技术





   
 ## 显示帮助菜单
```
python cli_tool.py -h
```
```
usage: cli_tool.py [-h] [-t TARGET] [-m {basic,medium,advance,custom}] [--flags FLAGS] [-o] [--config]
Net-Sentry Professional CLI
options:
-h, --help show this help message and exit
-t, --target TARGET Target IP or Domain
-m, --mode {basic,medium,advance,custom}
Scan Profile
--flags FLAGS Custom Nmap Flags
-o, --output Save report to file
--config Reset Admin Username/Password
```
## 用法:Web 命令控制台 (GUI)
### 1. 启动系统
启动 Web 服务器:
```
python app.py
```
### 控制台输出:[+] Net-Sentry Online. Access: http://127.0.0.1:(port)
### 2. 访问与登录
打开浏览器并导航至 http://127.0.0.1:(port)
默认用户名:`lokesh`
默认密码:`lokesh`
**安全提示:请立即使用仪表板标题中的 ⚙️ SETTINGS 按钮更改您的密码。**
### 3. 仪表板操作
实时终端:直接在浏览器控制台中输入命令。
scan google.com advance (启动全频谱扫描)
man nmap (查看速查表)
ping 8.8.8.8 (执行系统命令)
`战术地图:使用右上角面板中的按钮在 [TOPO] (网络图) 和 [WORLD] (地理地图) 之间切换。`
情报:在 "Active Intel" 框中查看实时 WAF 状态、CVE 警报和收集到的密钥。
`报告:点击 Mission Logs 表格中的 PDF 按钮下载专业的客户报告。`
## 用法:CLI 工具 (终端)
对于喜欢无头环境或需要将 Net-Sentry 集成到自动化管道中的安全研究人员,CLI 工具提供了完整的功能。
### 1. 基础扫描(快速)
执行快速端口扫描和基础情报收集。
```
python cli_tool.py -t example.com
```
### 2. 高级模式(全功率)
激活所有引擎,包括 Fuzzing、Spidering、Zone Transfer 和漏洞检查。
```
python cli_tool.py -t example.com -m advance
```
### 3. 自定义操作
定义您自己的 Nmap 标志以进行特定目标扫描。
```
python cli_tool.py -t example.com -m custom --flags "-p 80,443,8080 -sV --script=vuln"
```
### 4. 保存输出
将扫描结果保存到文本文件中以供归档。
```
python cli_tool.py -t example.com -m medium -o
```
## 显示帮助菜单
```
python cli_tool.py -h
```
```
usage: cli_tool.py [-h] [-t TARGET] [-m {basic,medium,advance,custom}] [--flags FLAGS] [-o] [--config]
Net-Sentry Professional CLI
options:
-h, --help show this help message and exit
-t, --target TARGET Target IP or Domain
-m, --mode {basic,medium,advance,custom}
Scan Profile
--flags FLAGS Custom Nmap Flags
-o, --output Save report to file
--config Reset Admin Username/Password
```
## 用法:Web 命令控制台 (GUI)
### 1. 启动系统
启动 Web 服务器:
```
python app.py
```
### 控制台输出:[+] Net-Sentry Online. Access: http://127.0.0.1:(port)
### 2. 访问与登录
打开浏览器并导航至 http://127.0.0.1:(port)
默认用户名:`lokesh`
默认密码:`lokesh`
**安全提示:请立即使用仪表板标题中的 ⚙️ SETTINGS 按钮更改您的密码。**
### 3. 仪表板操作
实时终端:直接在浏览器控制台中输入命令。
scan google.com advance (启动全频谱扫描)
man nmap (查看速查表)
ping 8.8.8.8 (执行系统命令)
`战术地图:使用右上角面板中的按钮在 [TOPO] (网络图) 和 [WORLD] (地理地图) 之间切换。`
情报:在 "Active Intel" 框中查看实时 WAF 状态、CVE 警报和收集到的密钥。
`报告:点击 Mission Logs 表格中的 PDF 按钮下载专业的客户报告。`
## 用法:CLI 工具 (终端)
对于喜欢无头环境或需要将 Net-Sentry 集成到自动化管道中的安全研究人员,CLI 工具提供了完整的功能。
### 1. 基础扫描(快速)
执行快速端口扫描和基础情报收集。
```
python cli_tool.py -t example.com
```
### 2. 高级模式(全功率)
激活所有引擎,包括 Fuzzing、Spidering、Zone Transfer 和漏洞检查。
```
python cli_tool.py -t example.com -m advance
```
### 3. 自定义操作
定义您自己的 Nmap 标志以进行特定目标扫描。
```
python cli_tool.py -t example.com -m custom --flags "-p 80,443,8080 -sV --script=vuln"
```
### 4. 保存输出
将扫描结果保存到文本文件中以供归档。
```
python cli_tool.py -t example.com -m medium -o
```
 **提示:CLI 工具使用与 Web 仪表板完全相同的引擎,确保各接口间结果的一致性。**
# 结果
```
███╗ ██╗███████╗████████╗ ███████╗███████╗███╗ ██╗████████╗██████╗ ██╗ ██╗
████╗ ██║██╔════╝╚══██╔══╝ ██╔════╝██╔════╝████╗ ██║╚══██╔══╝██╔══██╗╚██╗ ██╔╝
██╔██╗ ██║█████╗ ██║ █████╗███████╗█████╗ ██╔██╗ ██║ ██║ ██████╔╝ ╚████╔╝
██║╚██╗██║██╔══╝ ██║ ╚════╝╚════██║██╔══╝ ██║╚██╗██║ ██║ ██╔══██╗ ╚██╔╝
██║ ╚████║███████╗ ██║ ███████║███████╗██║ ╚████║ ██║ ██║ ██║ ██║
╚═╝ ╚═══╝╚══════╝ ╚═╝ ╚══════╝╚══════╝╚═╝ ╚═══╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝
[ SYSTEM ONLINE ] | [ GOD MODE ] | LOKESH KUMAR
--------------------------------------------------------------------------
[10:25:41] [TARGET] google.com
[10:25:41] [*] Profile: ADVANCE
--------------------------------------------------------------------------
⠴ Engaging google.com...
⠇ Engaging google.com...
[★] RISK SCORE: 85/100 (CRITICAL)
----------------------------------------
[*] TARGET: google.com
[*] MODE: ADVANCE
--- GEO-INTEL REPORT ---
[+] Org: Google LLC
[+] Country: Singapore (SG)
[+] ISP: Google LLC
[COORDS] 1.35208,103.82
------------------------
[*] THE ORACLE (SHODAN DB):
[+] Ports: [80, 443]
[✓] Clean record.
[✓] NO WAF DETECTED.
[*] SSL ILLUMINATOR:
[+] Issued: WR2
[SCOPE] Found 136 hidden domains:
> *.google.com
> *.appengine.google.com
> *.bdn.dev
> *.origin-test.bdn.dev
> *.cloud.google.com
> *.crowdsource.google.com
> *.datacompute.google.com
> *.google.ca
> *.google.cl
> *.google.co.in
...and 126 more.
[*] PASSIVE SUBDOMAINS:
[-] Passive recon failed: HTTPSConnectionPool(host='crt.sh', port=443): Read timed out. (read timeout=20)
[*] ACTIVE SUBDOMAIN DISCOVERY:
[⚡] Discovered 11 HIDDEN active subdomains:
> www.google.com
> mail.google.com
> blog.google.com
> ns1.google.com
> ns2.google.com
> smtp.google.com
> vpn.google.com
> m.google.com
> shop.google.com
> admin.google.com
> api.google.com
[*] DNS ZONE TRANSFER:
[✓] DNS Secure.
[-] CRITICAL: Nmap is not installed on the server. Please install it.
[*] DEEP VULNERABILITY SCAN (LFI/CONFIG):
[✓] No config backups exposed.
[✓] LFI check passed.
[*] DIRECTORY BUSTER:
[200] FOUND: /robots.txt
[*] CMS HUNTER (WORDPRESS):
[✓] WP API secure or not WordPress.
[*] GIT SOURCE HUNTER:
[✓] .git is secure.
[*] SPRING BOOT ACTUATOR SCAN:
[✓] Spring Boot Actuators secured.
[*] BROKEN LINK HIJACKING:
[-] BLH check failed.
[*] FIREBASE DATABASE HUNTER:
[✓] No open Firebase databases found.
[*] MOBILE APP ASSET SCANNER:
[+] Found Mobile Config: /apple-app-site-association
[⚠️] LEAK: Internal domains found in /apple-app-site-association
[*] HOST HEADER INJECTION:
[-] Host injection check failed.
[*] CRLF INJECTION (HEADER SPLITTING):
[✓] Header Splitting protected.
[*] CORS CONFIG CHECK:
[✓] CORS policy secure.
[*] CLICKJACKING CHECK:
[✓] Protected against Clickjacking.
[*] PROTOTYPE POLLUTION FUZZER:
[-] Pollution check failed.
[*] DESERIALIZATION SCAN:
[✓] No serialized objects found in cookies.
[*] VERB TAMPERING:
[✓] Verbs restricted.
[*] HTTP REQUEST SMUGGLING (CL.TE/TE.CL):
[✓] No smuggling anomalies detected.
[*] WEBSOCKET SECURITY (CSWSH):
[✓] No open WebSocket found.
[*] API RATE LIMIT BYPASS:
[✓] Rate limiting appears robust (or not triggered).
[*] GRAPHQL INSPECTOR:
[*] WEB CACHE POISONING DETECTOR:
[✓] Cache headers appear secure.
[*] JS MINER & DOM HUNTER:
[$$$] KEY LEAK (Google): AIzaSyBm7NubC-Swn1nt2nhYfxb58eCdmL2vCVU
└── Found in: Main HTML
└── STATUS: [SAFE] Restricted/Inactive
[i] Analyzing 2 JavaScript files...
[$$$] KEY LEAK (AWS): AKIABAAABJIBJJJJRJJJ
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [i] No auto-validation available.
[$$$] KEY LEAK (Google): AIzaSyBwQcjgmXUAsw5r4FZXO5t8_EZ_aUm_TGE
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'eval(' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.search' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.hash' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[$$$] KEY LEAK (Google): AIzaSyCbsbvGCe7C9mCtdaTycZB2eUFuzsYKG_E
└── Found in: rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
[+] Found 37 crawlable endpoints.
[*] API ZOMBIE (LOGIC HUNTER):
[☠️] CONFIRMED BOLA/IDOR: http://google.com/history/optout?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 97% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/advanced_search?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 88% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/preferences?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 96% (Valid Data Structure)
[*] DOM EXPLOIT SUGGESTIONS for innerHTML:
[i] Manual Verification Required. Try these in Browser:
> http://google.com#
**提示:CLI 工具使用与 Web 仪表板完全相同的引擎,确保各接口间结果的一致性。**
# 结果
```
███╗ ██╗███████╗████████╗ ███████╗███████╗███╗ ██╗████████╗██████╗ ██╗ ██╗
████╗ ██║██╔════╝╚══██╔══╝ ██╔════╝██╔════╝████╗ ██║╚══██╔══╝██╔══██╗╚██╗ ██╔╝
██╔██╗ ██║█████╗ ██║ █████╗███████╗█████╗ ██╔██╗ ██║ ██║ ██████╔╝ ╚████╔╝
██║╚██╗██║██╔══╝ ██║ ╚════╝╚════██║██╔══╝ ██║╚██╗██║ ██║ ██╔══██╗ ╚██╔╝
██║ ╚████║███████╗ ██║ ███████║███████╗██║ ╚████║ ██║ ██║ ██║ ██║
╚═╝ ╚═══╝╚══════╝ ╚═╝ ╚══════╝╚══════╝╚═╝ ╚═══╝ ╚═╝ ╚═╝ ╚═╝ ╚═╝
[ SYSTEM ONLINE ] | [ GOD MODE ] | LOKESH KUMAR
--------------------------------------------------------------------------
[10:25:41] [TARGET] google.com
[10:25:41] [*] Profile: ADVANCE
--------------------------------------------------------------------------
⠴ Engaging google.com...
⠇ Engaging google.com...
[★] RISK SCORE: 85/100 (CRITICAL)
----------------------------------------
[*] TARGET: google.com
[*] MODE: ADVANCE
--- GEO-INTEL REPORT ---
[+] Org: Google LLC
[+] Country: Singapore (SG)
[+] ISP: Google LLC
[COORDS] 1.35208,103.82
------------------------
[*] THE ORACLE (SHODAN DB):
[+] Ports: [80, 443]
[✓] Clean record.
[✓] NO WAF DETECTED.
[*] SSL ILLUMINATOR:
[+] Issued: WR2
[SCOPE] Found 136 hidden domains:
> *.google.com
> *.appengine.google.com
> *.bdn.dev
> *.origin-test.bdn.dev
> *.cloud.google.com
> *.crowdsource.google.com
> *.datacompute.google.com
> *.google.ca
> *.google.cl
> *.google.co.in
...and 126 more.
[*] PASSIVE SUBDOMAINS:
[-] Passive recon failed: HTTPSConnectionPool(host='crt.sh', port=443): Read timed out. (read timeout=20)
[*] ACTIVE SUBDOMAIN DISCOVERY:
[⚡] Discovered 11 HIDDEN active subdomains:
> www.google.com
> mail.google.com
> blog.google.com
> ns1.google.com
> ns2.google.com
> smtp.google.com
> vpn.google.com
> m.google.com
> shop.google.com
> admin.google.com
> api.google.com
[*] DNS ZONE TRANSFER:
[✓] DNS Secure.
[-] CRITICAL: Nmap is not installed on the server. Please install it.
[*] DEEP VULNERABILITY SCAN (LFI/CONFIG):
[✓] No config backups exposed.
[✓] LFI check passed.
[*] DIRECTORY BUSTER:
[200] FOUND: /robots.txt
[*] CMS HUNTER (WORDPRESS):
[✓] WP API secure or not WordPress.
[*] GIT SOURCE HUNTER:
[✓] .git is secure.
[*] SPRING BOOT ACTUATOR SCAN:
[✓] Spring Boot Actuators secured.
[*] BROKEN LINK HIJACKING:
[-] BLH check failed.
[*] FIREBASE DATABASE HUNTER:
[✓] No open Firebase databases found.
[*] MOBILE APP ASSET SCANNER:
[+] Found Mobile Config: /apple-app-site-association
[⚠️] LEAK: Internal domains found in /apple-app-site-association
[*] HOST HEADER INJECTION:
[-] Host injection check failed.
[*] CRLF INJECTION (HEADER SPLITTING):
[✓] Header Splitting protected.
[*] CORS CONFIG CHECK:
[✓] CORS policy secure.
[*] CLICKJACKING CHECK:
[✓] Protected against Clickjacking.
[*] PROTOTYPE POLLUTION FUZZER:
[-] Pollution check failed.
[*] DESERIALIZATION SCAN:
[✓] No serialized objects found in cookies.
[*] VERB TAMPERING:
[✓] Verbs restricted.
[*] HTTP REQUEST SMUGGLING (CL.TE/TE.CL):
[✓] No smuggling anomalies detected.
[*] WEBSOCKET SECURITY (CSWSH):
[✓] No open WebSocket found.
[*] API RATE LIMIT BYPASS:
[✓] Rate limiting appears robust (or not triggered).
[*] GRAPHQL INSPECTOR:
[*] WEB CACHE POISONING DETECTOR:
[✓] Cache headers appear secure.
[*] JS MINER & DOM HUNTER:
[$$$] KEY LEAK (Google): AIzaSyBm7NubC-Swn1nt2nhYfxb58eCdmL2vCVU
└── Found in: Main HTML
└── STATUS: [SAFE] Restricted/Inactive
[i] Analyzing 2 JavaScript files...
[$$$] KEY LEAK (AWS): AKIABAAABJIBJJJJRJJJ
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [i] No auto-validation available.
[$$$] KEY LEAK (Google): AIzaSyBwQcjgmXUAsw5r4FZXO5t8_EZ_aUm_TGE
└── Found in: m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'eval(' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.search' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[⚠️] DOM RISK: Found 'location.hash' in m=cdos,hsm,jsa,mb4ZUb,cEt90b,SNUn3,qddgKe,sTsDMc,dtl0hd,eHDfl,YV5bee,d,csi
[$$$] KEY LEAK (Google): AIzaSyCbsbvGCe7C9mCtdaTycZB2eUFuzsYKG_E
└── Found in: rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
└── STATUS: [SAFE] Restricted/Inactive
[⚠️] DOM RISK: Found 'innerHTML' in rs=AA2YrTvMeF_1CDYQne2BjPnlmkIuQqq6vg
[+] Found 37 crawlable endpoints.
[*] API ZOMBIE (LOGIC HUNTER):
[☠️] CONFIRMED BOLA/IDOR: http://google.com/history/optout?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 97% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/advanced_search?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 88% (Valid Data Structure)
[☠️] CONFIRMED BOLA/IDOR: http://google.com/preferences?hl=en-IN&fg=2
> Original ID: 1 | Test ID: 2
> Context Match: 96% (Valid Data Structure)
[*] DOM EXPLOIT SUGGESTIONS for innerHTML:
[i] Manual Verification Required. Try these in Browser:
> http://google.com#标签:AES-256, CTI, Flask, Nmap, Python, Scrypt密钥派生, SQLite, 多线程扫描, 安全测试, 实时处理, 密码管理, 开源安全工具, 批量查询, 插件系统, 攻击性安全, 数据统计, 无后门, 服务指纹识别, 检测规则, 漏洞评估, 端口扫描, 网络安全, 网络资产发现, 自动化侦察, 虚拟驱动器, 资产探测, 逆向工具, 逆向工程平台, 隐私保护