Shubh9414/MicrosoftAzure-Sentinel-SOAR-Lab
GitHub: Shubh9414/MicrosoftAzure-Sentinel-SOAR-Lab
Stars: 0 | Forks: 0
# Microsoft Sentinel 混合云 SOC 实验室
## 📝 项目概述
本项目是一个综合性的 **Detection Engineering** 与 **SOAR Automation** 作品集。我设计了一个混合云环境来模拟企业级 SOC,重点在于跨 Windows、Azure 和本地 Linux 等不同平台实现统一的可见性。通过设计自定义的 **KQL** 检测规则和 **SOAR** Playbook,我实现了从威胁检测到事件分诊的自动化流程。
| 特性 | 技术实现 |
| :--- | :--- |
| **SIEM & SOAR** | Microsoft Sentinel & Azure Logic Apps |
| **混合管道** | Azure Monitor Agent (AMA) & Azure Arc |
| **检测范围** | 10 条映射到 **MITRE ATT&CK** 的自定义 KQL 规则 |
| **日志工程** | 自定义 **Sysmon** XML (Event ID 10) & Linux **auditd** 规则 |
| **自动化** | 通过 Adaptive Card JSON payloads 实现事件到 Teams 的告警 |
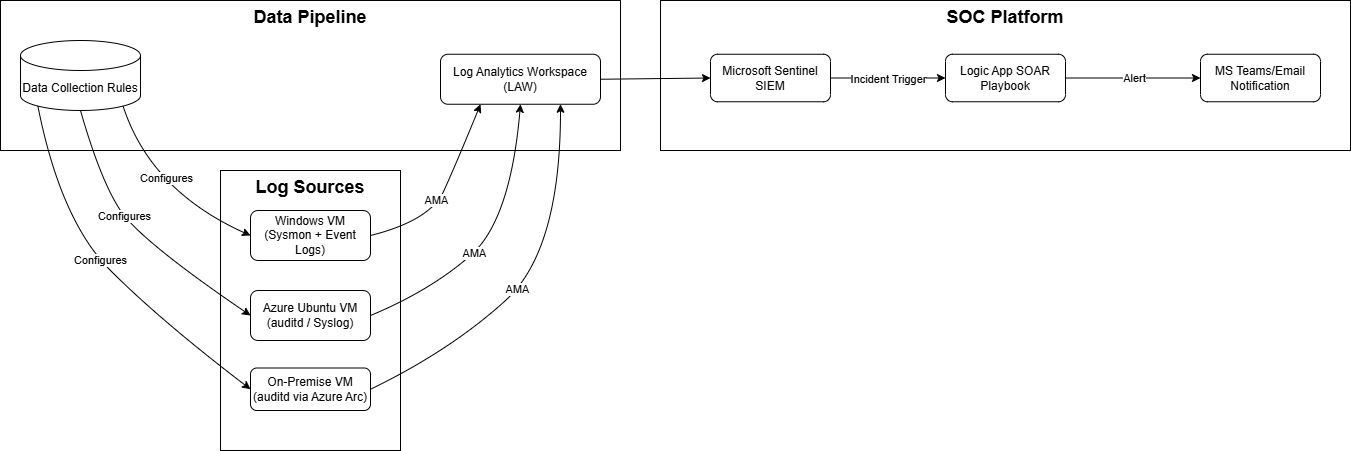
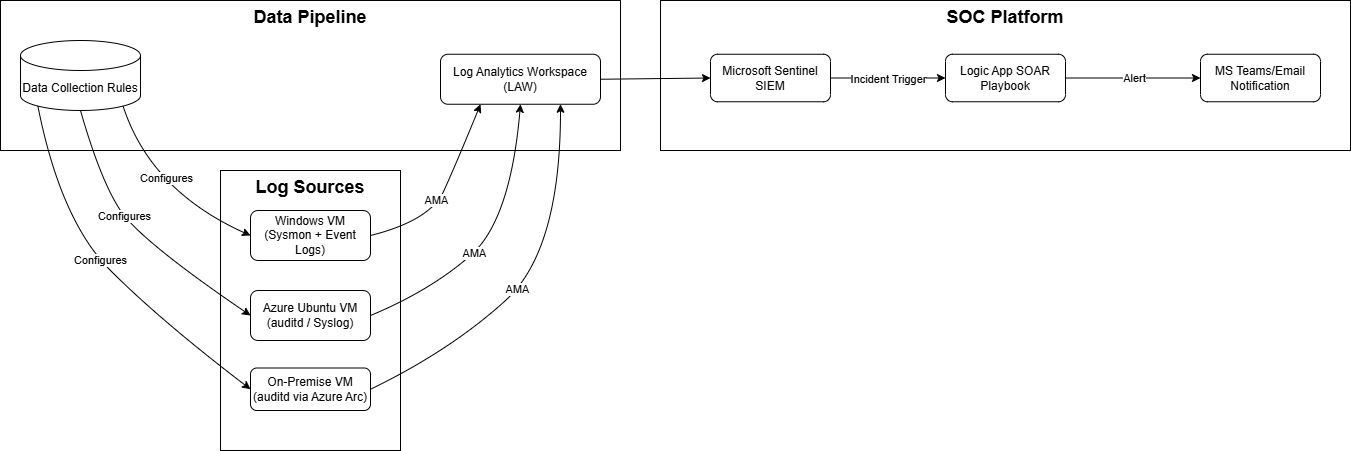
## 1. 实验室架构
该架构遵循混合云模型,旨在将云原生和本地端点的遥测数据集中到单一的 **Log Analytics Workspace (LAW)** 中
* **云基础设施:** Windows Server(通过 **Sysmon** 监控)和 Ubuntu VM(通过 **auditd** 监控)。
* **本地集成:** 通过 **Azure Arc** 集成 Linux VM,以模拟远程办公室监控。
* **统一管道:** 利用 **Data Collection Rules (DCRs)** 和 **Azure Monitor Agent (AMA)** 获取高保真日志,以便在 Sentinel 中进行实时分析。
 ## 2. 检测工程:10 条自定义分析规则
本项目的核心是一组由 10 条自定义 KQL 分析规则组成的集合,这些规则是通过模拟攻击并搜寻由此产生的遥测数据而开发出来的。
### Windows 检测(7 条规则)
### Linux 检测(3 条规则)
## 3. SOAR 自动化:事件到 Teams 告警
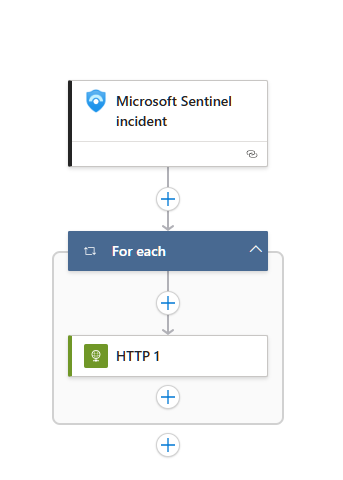
使用 Azure Logic Apps 配置了一个 SOAR Playbook,以自动化事件分诊的第一步。
* **触发器:** Microsoft Sentinel 中创建新的 "Incident" 时。
* **动作:** 解析事件数据(严重性、标题、描述)。
* **响应:** 向 Microsoft Teams 频道发布格式化的 Adaptive Card,供 SOC 分析师立即审查。
#### Logic App 工作流:
## 2. 检测工程:10 条自定义分析规则
本项目的核心是一组由 10 条自定义 KQL 分析规则组成的集合,这些规则是通过模拟攻击并搜寻由此产生的遥测数据而开发出来的。
### Windows 检测(7 条规则)
### Linux 检测(3 条规则)
## 3. SOAR 自动化:事件到 Teams 告警
使用 Azure Logic Apps 配置了一个 SOAR Playbook,以自动化事件分诊的第一步。
* **触发器:** Microsoft Sentinel 中创建新的 "Incident" 时。
* **动作:** 解析事件数据(严重性、标题、描述)。
* **响应:** 向 Microsoft Teams 频道发布格式化的 Adaptive Card,供 SOC 分析师立即审查。
#### Logic App 工作流:
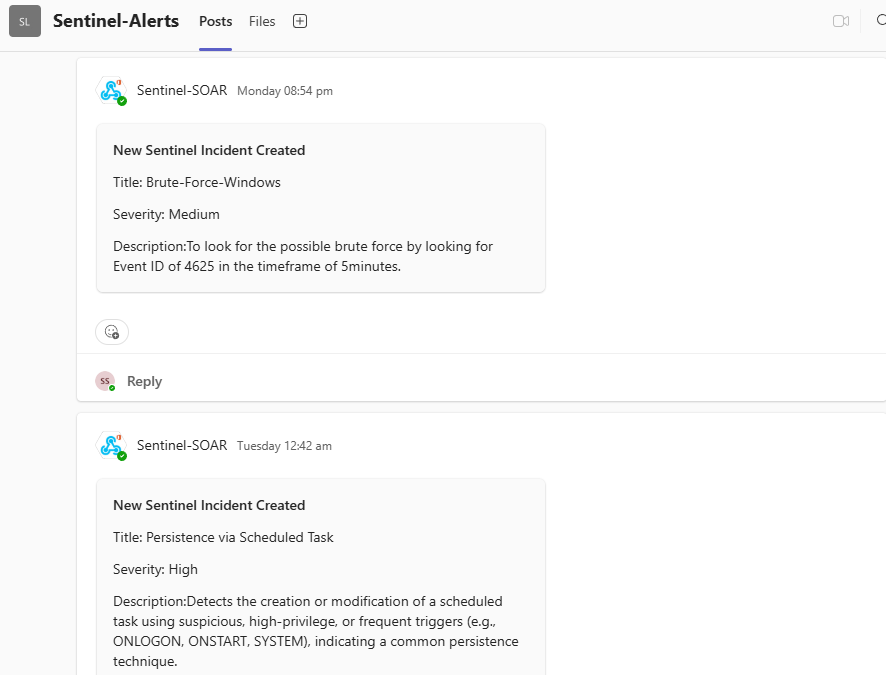
 #### 最终告警:
#### 最终告警:
 ## 4. 关键经验:日志配置与故障排除
本项目最大的挑战不在于编写 KQL,而在于配置数据管道。成功的检测工程需要高质量的日志。
- Windows (Sysmon): 默认的 Sysmon 日志不包含 Event ID 10 (ProcessAccess)。为了检测 LSASS 转储,我编辑了 sysmonconfig.xml 文件以明确包含针对 lsass.exe 的此 TTP。
- Linux (auditd): 这是一个主要的日志缺口。Linux VM 默认不发送任何命令行日志。修复过程需要三个步骤:
1. 安装 auditd 服务。
2. 编写自定义规则 (/etc/audit/rules.d/10-execve.rules) 以强制 auditd 记录所有 execve(进程执行)系统调用。
3. 配置d 插件 (/etc/audit/plugins.d/syslog.conf) 将这些新的安全日志转发到 Syslog,然后由 Sentinel 收集。
- 横向移动 (T1021.002): 针对此 TTP 的模拟(PsExec/impacket)反复失败。故障排除证明 Azure 网络层是正确的(通过 "IP flow verify"),但操作系统级别的连接被拒绝。这是由于受害者 VM 上复杂的 admin$ 共享和防火墙绑定问题无法解决。这是一个现实的实验室结果,也是本项目的一个已知限制。
## 4. 关键经验:日志配置与故障排除
本项目最大的挑战不在于编写 KQL,而在于配置数据管道。成功的检测工程需要高质量的日志。
- Windows (Sysmon): 默认的 Sysmon 日志不包含 Event ID 10 (ProcessAccess)。为了检测 LSASS 转储,我编辑了 sysmonconfig.xml 文件以明确包含针对 lsass.exe 的此 TTP。
- Linux (auditd): 这是一个主要的日志缺口。Linux VM 默认不发送任何命令行日志。修复过程需要三个步骤:
1. 安装 auditd 服务。
2. 编写自定义规则 (/etc/audit/rules.d/10-execve.rules) 以强制 auditd 记录所有 execve(进程执行)系统调用。
3. 配置d 插件 (/etc/audit/plugins.d/syslog.conf) 将这些新的安全日志转发到 Syslog,然后由 Sentinel 收集。
- 横向移动 (T1021.002): 针对此 TTP 的模拟(PsExec/impacket)反复失败。故障排除证明 Azure 网络层是正确的(通过 "IP flow verify"),但操作系统级别的连接被拒绝。这是由于受害者 VM 上复杂的 admin$ 共享和防火墙绑定问题无法解决。这是一个现实的实验室结果,也是本项目的一个已知限制。
 ## 2. 检测工程:10 条自定义分析规则
本项目的核心是一组由 10 条自定义 KQL 分析规则组成的集合,这些规则是通过模拟攻击并搜寻由此产生的遥测数据而开发出来的。
### Windows 检测(7 条规则)
## 2. 检测工程:10 条自定义分析规则
本项目的核心是一组由 10 条自定义 KQL 分析规则组成的集合,这些规则是通过模拟攻击并搜寻由此产生的遥测数据而开发出来的。
### Windows 检测(7 条规则)
1. RDP 暴力破解 (T1110.001)
* **描述:** 检测在短时间窗口内来自单一 IP 地址的大量 RDP 登录失败尝试(Event ID 4625)。 * **KQL:** Event | where EventID == 4625 | parse EventData with * 'IpAddress">' IpAddress "<" * | where isnotempty(IpAddress) and IpAddress != "-" | summarize count() by IpAddress, bin(TimeGenerated, 5m) | where count_ > 82. 编码的 PowerShell (T1059.001)
* **描述:** 检测带有编码命令标志(`-e`, `-en`, `-enc`, `-encodedcommand`)的 PowerShell 执行,这是一种混淆恶意脚本的常用技术。 * **KQL:** Event | where EventID == 4688 | parse EventData with * 'NewProcessName">' Process "<" * 'CommandLine">' CommandLine "<" * 'ParentProcessName">' ParentProcessName "<" * | where Process endswith "\\powershell.exe" and ParentprocessName endswith "\\svchost.exe" and ( CommandLine contains " -e " or CommandLine contains " -en " or CommandLine contains " -enc " or CommandLine contains " -encodedcommand " ) | project TimeGenerated, CommandLine, Process, ParentProcessName3. 可疑的 PowerShell 脚本块 (T1059.001)
* **描述:** 一种分层检测,用于搜寻 PowerShell 脚本块日志(Event ID 4104)中的高可信度恶意关键词(例如 `IEX`, `DownloadString`, `Invoke-Mimikatz`)。这可以捕捉到 4688 可能遗漏的非编码 Payload。 * **KQL:** Event | where EventID == 4104 | parse EventData with * '' ScriptBlockText '' * | where isnotempty(ScriptBlockText) | where (ScriptBlockText contains "IEX" or ScriptBlockText contains "Invoke-Expression" or ScriptBlockText contains "DownloadString" or ScriptBlockText contains "FromBase64String" or ScriptBlockText contains "Get-NetUser" or ScriptBlockText contains "Get-NetComputer" or ScriptBlockText contains "Get-NetGroup" or ScriptBlockText contains "Invoke-Mimikatz" or ScriptBlockText contains "System.Net.Sockets.TCPClient") | project TimeGenerated, Computer, UserName, RenderedDescription, ScriptBlockText4. LSASS 凭据转储 (T1003.001)
* **描述:** 检测非标准进程以高权限访问 LSASS 内存。这是通过 Mimikatz 或 `procdump.exe` 等工具进行凭据转储的强烈指征。(需要 Sysmon Event ID 10)。 * **KQL:** Event | where Source == "Microsoft-Windows-Sysmon" and EventID == 10 | parse EventData with * 'SourceImage">' SourceImage '' * 'TargetImage">' TargetImage '' * 'GrantedAccess">' GrantedAccess '' * | where TargetImage endswith "\\lsass.exe" | where not (SourceImage in ("C:\\Windows\\System32\\svchost.exe", "C:\\Windows\\System32\\taskmgr.exe", "C:\\Windows\\System32\\services.exe", "C:\\Windows\\System32\\wininit.exe" "C:\\Windows\\System32\\lsm.exe")) | where GrantedAccess in ("0x1010", "0x1410", "0x1F1FFF", "0x1038", "0x1438", "0x143a", "0x1f0fff", "0x1f2fff", "0x1f3fff") | project TimeGenerated, Computer, UserName,SourceImage, TargetImage, GrantedAccess5. 通过注册表 Run 键实现持久化 (T1547.001)
* **描述:** 检测通过可疑命令行工具(`powershell.exe`, `reg.exe`, `cmd.exe`)修改常见的持久化注册表键(Run, RunOnce),这对于合法的安装程序来说属于异常行为。 * **KQL:** Event | where Source == "Microsoft-Windows-Sysmon" and EventID == 13 | parse EventData with * 'TargetObject">' TargetObject '' * 'Image">' Image '' * | where TargetObject contains "CurrentVersion\\Run" or TargetObject contains "CurrentVersion\\RunOnce" | where Image endswith "\\reg.exe" or Image endswith "\\powershell.exe" or Image endswith "\\cmd.exe" or Image endswith "\\wscript.exe" or Image endswith "\\cscript.exe" | project TimeGenerated, Computer, UserName, Image, TargetObject6. 伪装系统进程 (T1036.003)
* **描述:** 检测从非标准、非法目录(例如 `Desktop`)运行的常见系统进程(例如 `svchost.exe`, `lsass.exe`),这表明发生了伪装攻击。 * **KQL:** Event | where Source == "Microsoft-Windows-Sysmon" and EventID == 1 | parse EventData with * 'Image">' Image '' * 'CommandLine">' CommandLine '' * | where (Image has "svchost.exe" or Image has "lsass.exe" or Image has "wininit.exe" or Image has "lsm.exe") | where not (Image startswith "C:\\Windows\\System32\\") | project TimeGenerated, Computer, UserName, Image, CommandLine7. 通过计划任务实现持久化 (T1546.011)
* **描述:** 检测使用可疑、高权限或频繁触发器(例如 ONLOGON, ONSTART, SYSTEM)创建计划任务,这是一种常见的持久化技术。 * **KQL:** Event | where Source == "Microsoft-Windows-Sysmon" and EventID == 1 | parse EventData with * 'Image">' Image '' * 'CommandLine">' CommandLine '' * | where Image endswith "\\schtasks.exe" | where CommandLine has "/Create" or CommandLine has "/Change" | where CommandLine has "/SC ONLOGON" or CommandLine has "/SC ONSTART" or CommandLine has "/SC MINUTE" or CommandLine has "/SC HOURLY" | where CommandLine has "/RU SYSTEM" or CommandLine has "SYSTEM" | project TimeGenerated, Computer, UserName, Image, CommandLine8. Linux 入口工具传输 (T1105)
* **描述:** 检测 `wget` 或 `curl` 将潜在 Payload(.sh, .py, .elf)下载到全局可写目录(`/tmp`, `/var/tmp`, `/dev/shm`)中。 * **KQL:** Syslog | where ProcessName in ("wget", "curl") or SyslogMessage has "wget " or SyslogMessage has "curl " | where SyslogMessage has "/tmp/" or SyslogMessage has "/var/tmp/" or SyslogMessage has "/dev/shm/" | where SyslogMessage has ".sh" or SyslogMessage has ".py" or SyslogMessage has ".elf" or SyslogMessage has ".bin" | project TimeGenerated, HostName, ProcessName, SyslogMessage9. Linux SSH 持久化 (T1098.004)
* **描述:** 检测进程(`tee`, `echo`, `cat`)向用户的 `.ssh/authorized_keys` 文件追加数据,这是一种常见的持久化技术。 * **KQL:** Syslog | where SyslogMessage has "type=EXECVE" | where SyslogMessage has "authorized_keys" | parse SyslogMessage with * 'a0="' A0 '"' * 'a1="' A1 '"' * 'a2="' A2 '"' * | where (A0 endswith "tee" or A0 endswith "echo" or A0 endswith "cat") and (A1 has "authorized_keys" or A2 has "authorized_keys" or A1 has ".ssh" or A2 has ".ssh") | project TimeGenerated, HostName, SyslogMessage, A0, A1, A210. 来自可疑位置的 Linux 脚本执行 (T1059.004)
* **描述:** 检测 Shell(bash, python 等)从全局可写目录(`/tmp`, `/var/tmp`, `/dev/shm`)执行脚本,这是一种典型的攻击者模式。 * **KQL:** Syslog | where SyslogMessage has "type=EXECVE" | where SyslogMessage has "/tmp/" or SyslogMessage has "/var/tmp/" or SyslogMessage has "/dev/shm/" | parse SyslogMessage with * 'a0="' A0 '"' * 'a1="' A1 '"' * | where ( A0 endswith "bash" or A0 endswith "sh" or A0 endswith "zsh" or A0 endswith "perl" or A0 endswith "python" ) and ( A1 startswith "/tmp/" or A1 startswith "/var/tmp/" or A1 startswith "/dev/shm/" ) | project TimeGenerated, HostName, SyslogMessage, A0, A1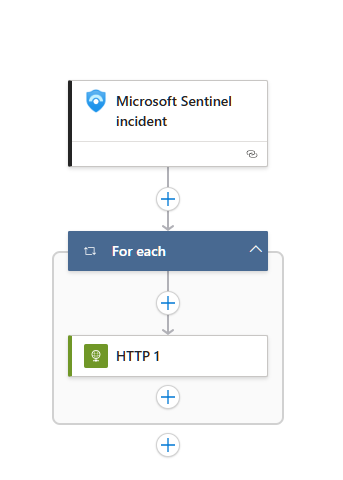 #### 最终告警:
#### 最终告警:
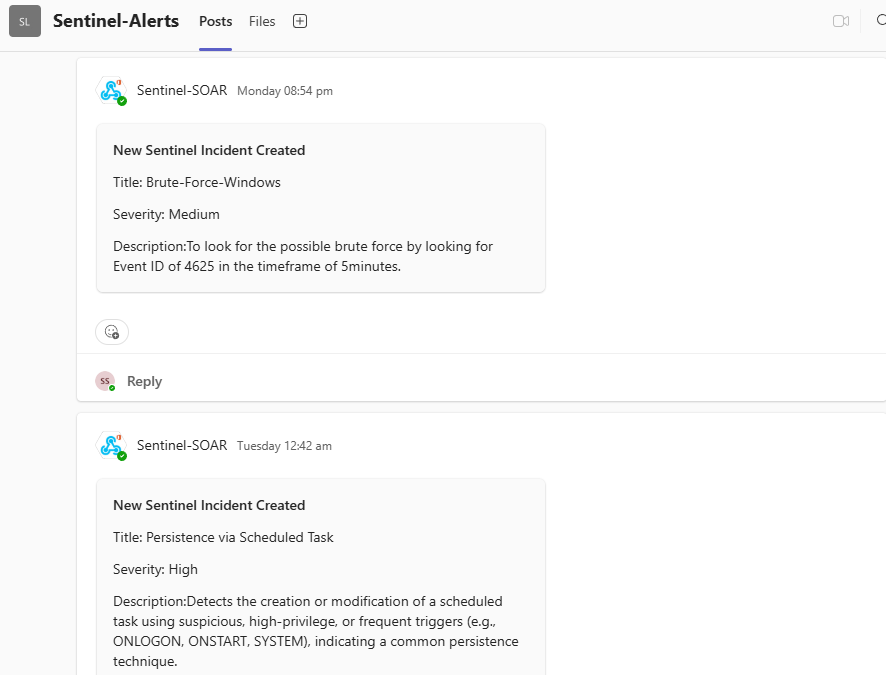
Adaptive Card JSON Payload
``` { "type": "message", "attachments": [ { "contentType": "application/vnd.microsoft.card.adaptive", "content": { "type": "AdaptiveCard", "version": "1.2", "body": [ { "type": "TextBlock", "text": "New Sentinel Incident Created", "weight": "bolder", "size": "medium" }, { "type": "TextBlock", "text": "Title: @{triggerBody()?['object']?['properties']?['title']}", "wrap": true }, { "type": "TextBlock", "text": "Severity: @{triggerBody()?['object']?['properties']?['severity']}", "wrap": true }, { "type": "TextBlock", "text": "Description: @{items('For_each')?['properties']?['description']}", "wrap": true } ], "$schema": "[http://adaptivecards.io/schemas/adaptive-card.json]" } } ] } ```标签:AMA, AMSI绕过, Azure Arc, Azure Logic Apps, Azure Monitor Agent, Azure安全, Cloudflare, DCR, DNS 反向解析, incident response, KQL, Kusto查询语言, Linux Auditd, Log Analytics Workspace, Microsoft Sentinel, MITRE ATT&CK, PE 加载器, RDP暴力破解, SOAR, SOC分析师, Sysmon, 云端安全, 威胁检测, 数据收集规则, 混合云SOC, 端点监控, 网络安全实验室