OSINT自动化工具,面向黑客。
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/blacklanternsecurity/bbot
BEE·bot
黑客的OSINT自动化。
pip install bbot
BBOT是受Spiderfoot启发的递归性的模块化OSINT框架。
BBOT可以在单个命令中执行整个OSINT过程:子域枚举、端口扫描、网页截图(使用gowitness)、漏洞扫描(使用nuclei)等等。BBOT拥有80多个模块和不断增长的数量。
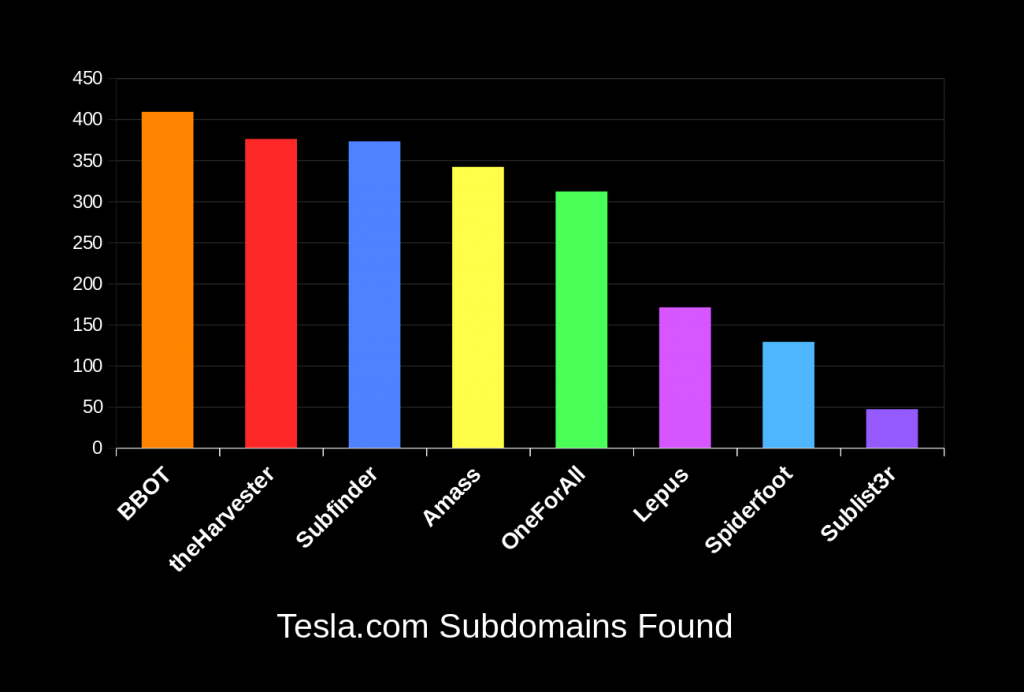
阅读我们的[博客文章] (https://blog.blacklanternsecurity.com/p/subdomain-enumeration-tool-face-off)了解为什么BBOT是最全面的子域枚举工具。
安装(pip)
注意:建议在虚拟环境中安装(例如通过pipx)
#稳定版本
pip install bbot
#最新版(开发分支)
pip install --pre bbot
bbot --help
先决条件:
- Linux(不支持Windows和macOS)
- Python 3.9或更高版本
安装(Docker)
#最新版(开发版)
docker run -it blacklanternsecurity/bbot --help
#稳定版
docker run -it blacklanternsecurity/bbot:stable --help
#注意:或者有一个帮助程序脚本,它将映射docker卷以保留您的BBOT扫描数据:
./bbot-docker.sh --help
如果您需要安装帮助,请参考[维基] (https://github.com/blacklanternsecurity/bbot/wiki#installation)。
另请参见:[发布历史] (https://github.com/blacklanternsecurity/bbot/wiki/Release-History)
使用BBOT进行扫描
示例
# 子域名
bbot -t evilcorp.com -f subdomain-enum
# 子域名(仅被动)
bbot -t evilcorp.com -f subdomain-enum -rf passive
# 子域名 + 端口扫描 + 网页截图
bbot -t evilcorp.com -f subdomain-enum -m naabu gowitness -n my_scan -o .
# 子域名 + 基本Web扫描(wappalyzer、robots.txt、iis短名称等)
bbot -t evilcorp.com -f subdomain-enum web-basic
# 子域名 + 网络蜘蛛(搜索电子邮件等)
bbot -t evilcorp.com -f subdomain-enum -c web_spider_distance=2 web_spider_depth=2
# 所有一次性扫描
# 子域名 + 电子邮件 + 云 + 端口扫描 + 非侵入式Web + 网页截图 + nuclei
bbot -t evilcorp.com -f subdomain-enum email-enum cloud-enum web-basic -m naabu gowitness nuclei --allow-deadly
# 列出模块
bbot -l
目标
目标是用初始数据种子扫描的。您可以直接在命令行或文件中指定无限数量的目标(或两者都有!)。目标可以是以下任何一种:
- DNS_NAME (
evilcorp.com) - IP_ADDRESS (
1.2.3.4) - IP_RANGE (
1.2.3.0/24) - URL (
https://www.evilcorp.com) - EMAIL_ADDRESS (
bob@evilcorp.com)
例如,以下扫描是完全有效的:
# 多个目标
bbot -t evilcorp.com evilcorp.co.uk http://www.evilcorp.cn 1.2.3.0/24 other_targets.txt
白名单/黑名单
BBOT的白名单确定什么被认为是范围内的。默认情况下,白名单只是您的目标。但是,如果您想要更细粒度的范围控制,可以使用--whitelist(或添加--blacklist)覆盖它。
# 用两个域种子扫描,但仅在它们位于1.2.3.0/24内部时才将资产视为范围内
bbot -t evilcorp.com evilcorp.co.uk --whitelist 1.2.3.0/24 --blacklist test.evilcorp.com 1.2.3.4 blacklist.txt
请访问维基了解更多技巧和技巧。
将BBOT作为Python库使用
from bbot.scanner import Scanner
# 可以指定任意数量的目标
scan = Scanner("evilcorp.com", "evilcorp.co.uk", modules=["httpx", "sslcert"])
for event in scan.start():
print(event.json())
输出
默认情况下,BBOT以TXT、JSON和CSV格式保存其输出。要启用更多的输出模块,可以使用--output-module。
# 将输出写入文件
bbot -f subdomain-enum -t evilcorp.com | tee evilcorp.txt
# 输出到JSON
bbot --output-module json -f subdomain-enum -t evilcorp.com | jq
# 在当前目录中输出资产清单
bbot -o . --output-module asset_inventory -f subdomain-enum -t evilcorp.com
对于每个扫描,BBOT都会生成一个独特且有趣的名称,例如demonic_jimmy。该扫描的输出,包括词云和gowitness截图等,保存在名为该名称的文件夹中,在~/.bbot/scans。保留最近的20个扫描,旧的扫描将被删除。您可以使用--output更改BBOT的输出位置,并且还可以使用--name选择自定义扫描名称。
如果您重复使用扫描名称,则会将其附加到其原始输出文件并利用先前的词云。
Neo4j
Neo4j是查看和与BBOT数据交互的最有趣(也是最漂亮)的方式。
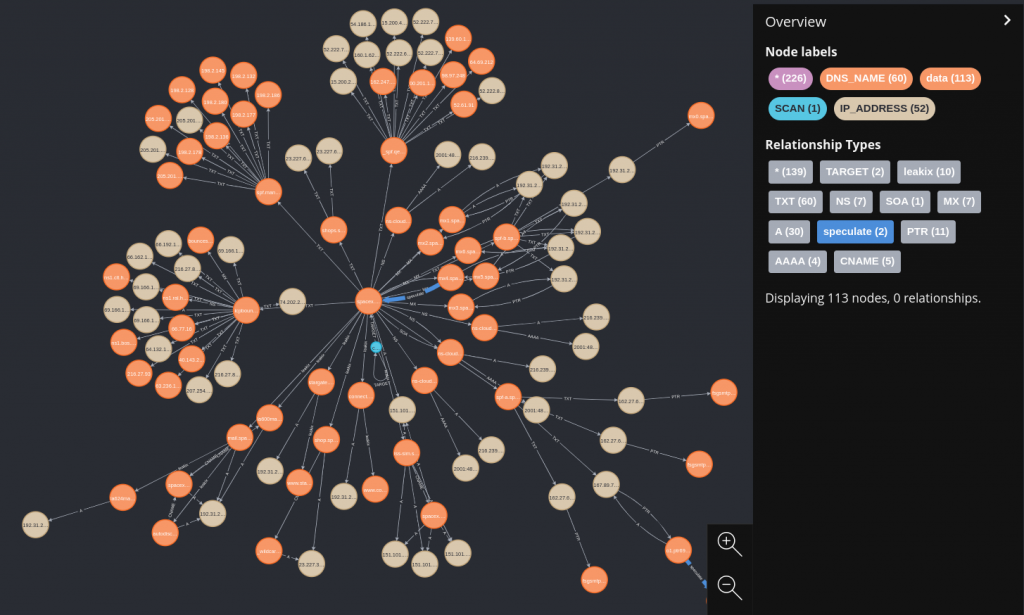
- 您可以使用单个docker命令启动Neo4j:
docker run -p 7687:7687 -p 7474:7474 -v "$(pwd)/data/:/data/" -e NEO4J_AUTH=neo4j/bbotislife neo4j
- 之后,使用
--output-modules neo4j运行bbot
bbot -f subdomain-enum -t evilcorp.com --output-modules neo4j
- 在http://localhost:7474上浏览数据。
用法
$ bbot --help
usage: bbot [-h] [--help-all] [-t TARGET [TARGET ...]] [-w WHITELIST [WHITELIST ...]] [-b BLACKLIST [BLACKLIST ...]] [--strict-scope] [-n SCAN_NAME] [-m MODULE [MODULE ...]] [-l] [-em MODULE [MODULE ...]]
[-f FLAG [FLAG ...]] [-rf FLAG [FLAG ...]] [-ef FLAG [FLAG ...]] [-om MODULE [MODULE ...]] [-o DIR] [-c [CONFIG ...]] [--allow-deadly] [-v] [-d] [-s] [--force] [-y] [--dry-run] [--current-config]
[--save-wordcloud FILE] [--load-wordcloud FILE] [--no-deps | --force-deps | --retry-deps | --ignore-failed-deps | --install-all-deps] [-a] [--version]
Bighuge BLS OSINT工具
选项:
-h,--help 显示此帮助消息并退出
--help-all 显示完整的帮助,包括模块配置选项
-n SCAN_NAME,--name SCAN_NAME
扫描名称(默认情况下为随机)
-m MODULE [MODULE ...],--modules MODULE [MODULE ...]
要启用的模块。选择:affiliates、anubisdb、asn、azure_tenant、badsecrets、bevigil、binaryedge、bucket_aws、bucket_azure、bucket_digitalocean、bucket_firebase、bucket_gcp、builtwith、bypass403、c99、censys、certspotter、crobat、crt、dnscommonsrv、dnsdumpster、dnszonetransfer、emailformat、ffuf、ffuf_shortnames、fingerprintx、fullhunt、generic_ssrf、github、gowitness、hackertarget、host_header、httpx、hunt、hunterio、iis_shortnames、ipneighbor、ipstack、leakix、masscan、massdns、naabu、ntlm、nuclei、otx、paramminer_cookies、paramminer_getparams、paramminer_headers、passivetotal、pgp、rapiddns、riddler、robots、secretsdb、securitytrails、shodan_dns、skymem、smuggler、social、sslcert、subdomain_hijack、sublist3r、telerik、threatminer、url_manipulation、urlscan、vhost、viewdns、virustotal、wafw00f、wappalyzer、wayback、zoomeye
-l,--list-modules 列出可用模块。
-em MODULE [MODULE ...],--exclude-modules MODULE [MODULE ...]
排除这些模块。
-f FLAG [FLAG ...],--flags FLAG [FLAG ...]
标志启用模块。选择:active、affiliates、aggressive、cloud-enum、deadly、email-enum、iis-shortnames、passive、portscan、report、safe、service-enum、slow、social-enum、subdomain-enum、subdomain-hijack、web-basic、web-paramminer、web-screenshots、web-thorough
-rf FLAG [FLAG ...],--require-flags FLAG [FLAG ...]
禁用没有这些标志的模块(例如 -rf passive)
-ef FLAG [FLAG ...],--exclude-flags FLAG [FLAG ...]
禁用具有这些标志的模块。 (例如 -ef aggressive)
-om MODULE [MODULE ...],--output-modules MODULE [MODULE ...]
输出模块。选择:asset_inventory、csv、http、human、json、neo4j、python、web_report、websocket
-o DIR,--output-dir DIR
-c [CONFIG ...],--config [CONFIG ...]
自定义配置文件或以key=value格式的配置选项:'modules.shodan.api_key=1234'
--allow-deadly 启用使用高度侵略性的模块
-v,--verbose 更详细
-d,--debug 启用调试
-s,--silent 保持安静
--force 即使模块设置失败也运行扫描
-y,--yes 跳过扫描确认提示
--dry-run 在执行扫描之前中止
--current-config 以YAML格式显示当前配置
目标:
-t TARGET [TARGET ...],--targets TARGET [TARGET ...]
用于启动扫描的目标
-w WHITELIST [WHITELIST ...],--whitelist WHITELIST [WHITELIST ...]
被视为范围内的内容(默认情况下与 --targets 相同)
-b BLACKLIST [BLACKLIST ...],--blacklist BLACKLIST [BLACKLIST ...]
不要触摸这些东西
--strict-scope 不将目标/白名单的子域视为范围内
词云:
保存/加载扫描期间收集到的常见单词的单词列表
--save-wordcloud FILE
扫描完成后将单词云输出到自定义文件
--load-wordcloud FILE
从自定义文件加载单词云
模块依赖项:
控制模块安装其依赖项的方式
--no-deps 不安装模块依赖项
--force-deps 强制安装所有模块依赖项
--retry-deps 再次尝试安装失败的模块依赖项
--ignore-failed-deps 运行模块,即使它们具有失败的依赖关系
--install-all-deps 为所有模块安装依赖项
代理:
向中央服务器报告
-a,--agent-mode 以代理模式启动
其他:
--version 显示BBOT版本并退出
BBOT配置
BBOT按以下顺序从以下位置加载其配置:
~/.config/bbot/bbot.yml<-- 将其用作主要配置~/.config/bbot/secrets.yml<-- 将其用于诸如API密钥之类的敏感内容- 命令行(
--config)
当您第一次运行BBOT时,将自动为您创建这些配置文件。
命令行参数优先于所有其他参数。您可以使用--config myconf.yml或像这样的单个参数为BBOT提供自定义配置文件:--config http_proxy=http://127.0.0.1:8080 modules.shodan_dns.api_key=1234。要显示完整且当前的BBOT配置,包括任何命令行参数,请使用bbot --current-config。
请注意,在bbot.yml中放置以下内容:
modules:
shodan:
api_key: deadbeef
与以下内容相同:
bbot --config modules.shodan.api_key=deadbeef
有关配置选项的说明,请参见defaults.yml或wiki。
模块
注意:您可以在模块游乐场找到更多有趣的模块。有关如何安装这些其他模块的说明,请参阅wiki。
要查看模块选项(如何更改单词列表,线程计数等),请使用“--help-all”。
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| Module | Type | Needs | Description | Flags | Produced Events |
| | | API | | | |
| | | Key | | | |
+======================+==========+=========+==========================================+==========================================+==========================================+
| badsecrets | scan | | Library for detecting known or weak | active,safe,web-basic,web-thorough | FINDING,VULNERABILITY |
| | | | secrets across many web frameworks | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bucket_aws | scan | | Check for S3 buckets related to target | active,cloud-enum,safe,web-basic,web- | FINDING,STORAGE_BUCKET |
| | | | | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bucket_azure | scan | | Check for Azure storage blobs related to | active,cloud-enum,safe,web-basic,web- | FINDING,STORAGE_BUCKET |
| | | | target | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bucket_digitalocean | scan | | Check for DigitalOcean spaces related to | active,cloud-enum,safe,slow,web-thorough | FINDING,STORAGE_BUCKET |
| | | | target | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bucket_firebase | scan | | Check for open Firebase databases | active,cloud-enum,safe,web-basic,web- | FINDING,STORAGE_BUCKET |
| | | | related to target | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bucket_gcp | scan | | Check for Google object storage related | active,cloud-enum,safe,web-basic,web- | FINDING,STORAGE_BUCKET |
| | | | to target | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bypass403 | scan | | Check 403 pages for common bypasses | active,aggressive,web-thorough | FINDING |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| dnszonetransfer | scan | | Attempt DNS zone transfers | active,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| ffuf | scan | | A fast web fuzzer written in Go | active,aggressive,deadly | URL_UNVERIFIED |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| ffuf_shortnames | scan | | Use ffuf in combination IIS shortnames | active,aggressive,iis-shortnames,web- | URL_UNVERIFIED |
| | | | | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| fingerprintx | scan | | Fingerprint exposed services like RDP, | active,safe,service-enum,slow | PROTOCOL |
| | | | SSH, MySQL, etc. | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| generic_ssrf | scan | | Check for generic SSRFs | active,aggressive,web-thorough | VULNERABILITY |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| gowitness | scan | | Take screenshots of webpages | active,safe,web-screenshots | TECHNOLOGY,URL,URL_UNVERIFIED,WEBSCREENS |
| | | | | | HOT |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| host_header | scan | | Try common HTTP Host header spoofing | active,aggressive,web-thorough | FINDING |
| | | | techniques | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| httpx | scan | | Visit webpages. Many other modules rely | active,cloud-enum,safe,social- | HTTP_RESPONSE,URL |
| | | | on httpx | enum,subdomain-enum,web-basic,web- | |
| | | | | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| hunt | scan | | Watch for commonly-exploitable HTTP | active,safe,web-basic,web-thorough | FINDING |
| | | | parameters | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| iis_shortnames | scan | | Check for IIS shortname vulnerability | active,iis-shortnames,safe,web- | URL_HINT |
| | | | | basic,web-thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| masscan | scan | | Port scan IP subnets with masscan | active,aggressive,portscan | OPEN_TCP_PORT |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| naabu | scan | | Execute port scans with naabu | active,aggressive,portscan,web-thorough | OPEN_TCP_PORT |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| ntlm | scan | | Watch for HTTP endpoints that support | active,safe,web-basic,web-thorough | DNS_NAME,FINDING |
| | | | NTLM authentication | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| nuclei | scan | | Fast and customisable vulnerability | active,aggressive,deadly | FINDING,VULNERABILITY |
| | | | scanner | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| paramminer_cookies | scan | | Smart brute-force to check for common | active,aggressive,slow,web-paramminer | FINDING |
| | | | HTTP cookie parameters | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| paramminer_getparams | scan | | Use smart brute-force to check for | active,aggressive,slow,web-paramminer | FINDING |
| | | | common HTTP GET parameters | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| paramminer_headers | scan | | Use smart brute-force to check for | active,aggressive,slow,web-paramminer | FINDING |
| | | | common HTTP header parameters | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| robots | scan | | Look for and parse robots.txt | active,safe,web-basic,web-thorough | URL_UNVERIFIED |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| secretsdb | scan | | Detect common secrets with secrets- | active,safe,web-basic,web-thorough | FINDING |
| | | | patterns-db | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| smuggler | scan | | Check for HTTP smuggling | active,aggressive,slow,web-thorough | FINDING |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| social | scan | | Look for social media links in webpages | active,safe,social-enum | SOCIAL |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| sslcert | scan | | Visit open ports and retrieve SSL | active,affiliates,email- | DNS_NAME,EMAIL_ADDRESS |
| | | | certificates | enum,safe,subdomain-enum,web-basic,web- | |
| | | | | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| subdomain_hijack | scan | | Detect hijackable subdomains | active,cloud-enum,safe,subdomain- | FINDING |
| | | | | enum,subdomain-hijack,web-basic,web- | |
| | | | | thorough | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| telerik | scan | | Scan for critical Telerik | active,aggressive,slow,web-thorough | FINDING,VULNERABILITY |
| | | | vulnerabilities | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| url_manipulation | scan | | Attempt to identify URL parsing/routing | active,aggressive,web-thorough | FINDING |
| | | | based vulnerabilities | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| vhost | scan | | Fuzz for virtual hosts | active,aggressive,deadly,slow | DNS_NAME,VHOST |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| wafw00f | scan | | Web Application Firewall Fingerprinting | active,aggressive | WAF |
| | | | Tool | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| wappalyzer | scan | | Extract technologies from web responses | active,safe,web-basic,web-thorough | TECHNOLOGY |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| affiliates | scan | | Summarize affiliate domains at the end | passive,report,safe | |
| | | | of a scan | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| anubisdb | scan | | Query jldc.me's database for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| asn | scan | | Query ripe and bgpview.io for ASNs | passive,report,safe,subdomain-enum | ASN |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| azure_tenant | scan | | Query Azure for tenant sister domains | affiliates,passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| bevigil | scan | X | Retrieve OSINT data from mobile | passive,safe,subdomain-enum | DNS_NAME,URL_UNVERIFIED |
| | | | applications using BeVigil | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| binaryedge | scan | X | Query the BinaryEdge API | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| builtwith | scan | X | Query Builtwith.com for subdomains | affiliates,passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| c99 | scan | X | Query the C99 API for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| censys | scan | X | Query the Censys API | email-enum,passive,safe,subdomain-enum | DNS_NAME,EMAIL_ADDRESS,IP_ADDRESS,OPEN_P |
| | | | | | ORT,PROTOCOL |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| certspotter | scan | | Query Certspotter's API for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| crobat | scan | | Query Project Crobat for subdomains | passive,safe | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| crt | scan | | Query crt.sh (certificate transparency) | passive,safe,subdomain-enum | DNS_NAME |
| | | | for subdomains | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| dnscommonsrv | scan | | Check for common SRV records | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| dnsdumpster | scan | | Query dnsdumpster for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| emailformat | scan | | Query email-format.com for email | email-enum,passive,safe | EMAIL_ADDRESS |
| | | | addresses | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| fullhunt | scan | X | Query the fullhunt.io API for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| github | scan | X | Query Github's API for related | passive,safe,subdomain-enum | URL_UNVERIFIED |
| | | | repositories | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| hackertarget | scan | | Query the hackertarget.com API for | passive,safe,subdomain-enum | DNS_NAME |
| | | | subdomains | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| hunterio | scan | X | Query hunter.io for emails | email-enum,passive,safe,subdomain-enum | DNS_NAME,EMAIL_ADDRESS,URL_UNVERIFIED |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| ipneighbor | scan | | Look beside IPs in their surrounding | aggressive,passive,subdomain-enum | IP_ADDRESS |
| | | | subnet | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| ipstack | scan | X | Query IPStack's API for GeoIP | passive,safe | GEOLOCATION |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| leakix | scan | | Query leakix.net for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| massdns | scan | | Brute-force subdomains with massdns | aggressive,passive,slow,subdomain-enum | DNS_NAME |
| | | | (highly effective) | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| otx | scan | | Query otx.alienvault.com for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| passivetotal | scan | X | Query the PassiveTotal API for | passive,safe,subdomain-enum | DNS_NAME |
| | | | subdomains | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| pgp | scan | | Query common PGP servers for email | email-enum,passive,safe | EMAIL_ADDRESS |
| | | | addresses | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| rapiddns | scan | | Query rapiddns.io for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| riddler | scan | | Query riddler.io for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| securitytrails | scan | X | Query the SecurityTrails API for | passive,safe,subdomain-enum | DNS_NAME |
| | | | subdomains | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| shodan_dns | scan | X | Query Shodan for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| skymem | scan | | Query skymem.info for email addresses | email-enum,passive,safe | EMAIL_ADDRESS |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| sublist3r | scan | | Query sublist3r's API for subdomains | passive,safe | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| threatminer | scan | | Query threatminer's API for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| urlscan | scan | | Query urlscan.io for subdomains | passive,safe,subdomain-enum | DNS_NAME,URL_UNVERIFIED |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| viewdns | scan | | Query viewdns.info's reverse whois for | affiliates,passive,safe | DNS_NAME |
| | | | related domains | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| virustotal | scan | X | Query VirusTotal's API for subdomains | passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| wayback | scan | | Query archive.org's API for subdomains | passive,safe,subdomain-enum | DNS_NAME,URL_UNVERIFIED |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| zoomeye | scan | X | Query ZoomEye's API for subdomains | affiliates,passive,safe,subdomain-enum | DNS_NAME |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| asset_inventory | output | | Output to an asset inventory style | | |
| | | | flattened CSV file | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| csv | output | | Output to CSV | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| http | output | | Send every event to a custom URL via a | | |
| | | | web request | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| human | output | | Output to text | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| json | output | | Output to JSON | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| neo4j | output | | Output to Neo4j | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| python | output | | Output via Python API | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| web_report | output | | Create a markdown report with web assets | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| websocket | output | | Output to websockets | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| aggregate | internal | | Summarize statistics at the end of a | passive,safe | |
| | | | scan | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| excavate | internal | | Passively extract juicy tidbits from | passive | URL_UNVERIFIED |
| | | | scan data | | |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+
| speculate | internal | | Derive certain event types from others | passive | DNS_NAME,FINDING,IP_ADDRESS,OPEN_TCP_POR |
| | | | by common sense | | T |
+----------------------+----------+---------+------------------------------------------+------------------------------------------+------------------------------------------+鸣谢
BBOT由@TheTechromancer编写。BBOT中的Web黑客攻击是由@liquidsec实现的,他编写了大部分Web模块和辅助工具。
特别感谢以下人员使BBOT成为可能:
- @kerrymilan 因其Neo4j和Ansible专业知识
- Steve Micallef (@smicallef) 因为创建了Spiderfoot
- Aleksei Kornev (@alekseiko) 因允许我们拥有 bbot Pypi 仓库 <3