PowerHuntShares 域控审计小工具
作者:Sec-Labs | 发布时间:
工具介绍
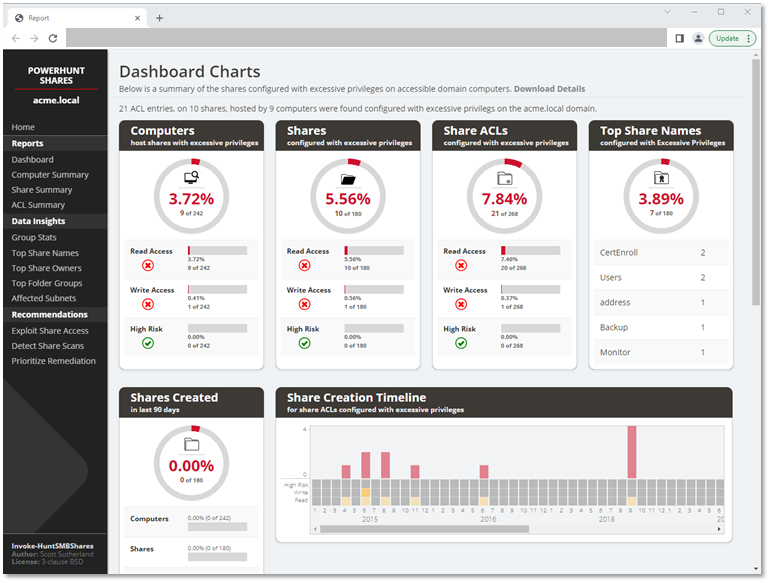
PowerHuntShares被设计用来自动清点、分析和报告分配给活动目录域连接的计算机上的SMB共享的过度权限。
它的目的是帮助IAM和其他蓝色团队更好地了解他们的SMB共享攻击面,并提供数据洞察力,以帮助自然分组相关的共享,帮助简化大规模的补救工作。
它支持以下功能:
- 使用当前的用户环境、凭证或明文用户/密码进行认证。
- 自动发现与活动目录域相关的可访问系统。它还将根据可用的开放端口过滤活动目录计算机。
- 针对单一计算机、计算机列表或发现的活动目录计算机(默认)。
- 使用PowerShell从目标计算机收集SMB共享ACL信息。
- 分析收集的共享ACL数据。
- 以HTML和CSV文件格式报告摘要报告和过度权限细节。
过多的SMB共享ACL是一个系统性的问题,也是所有组织都在努力解决的攻击面。这个项目的目标是提供一个证明概念,致力于建立一个更好的共享收集和数据洞察引擎,可以帮助通知和优先考虑补救工作。
额外功能:
- 为可配置的深度生成目录列表转储
- 在发现的共享中搜索文件类型
我还把一个简短的介绍放在一起,概述了一些常见的错误配置和优先补救的策略。参考《评估活动目录SMB共享的规模 (Secure360) 》
工具下载
https://github.com/NetSPI/PowerHuntShares
词汇表
PowerHuntShares将清点配置有 "过度权限 "的SMB共享ACL,并突出显示 "高风险 "ACL。以下是在这种情况下的定义。
过高的权限
过高的读写权限被定义为任何网络共享ACL,其中包含 "Everyone"、"Authenticated Users"、"BUILTIN\Users"、"Domain Users "或 "Domain Computers "组的明确ACE(访问控制条目)。由于权限继承问题,所有这些都为域用户提供了对受影响共享的访问权。请注意,有一个参数允许操作员添加他们自己的目标组。
下面是一些额外的背景:
- 每个人都是一个直接引用,适用于未认证和认证的用户。通常情况下,只需要一个空会话就可以访问这些资源。
- BUILTIN/Users包含认证的用户
- 认证的用户包含域连接系统中的域用户。这就是为什么当共享权限被分配给 "BUILTIN\Users "时,域用户可以访问一个共享。
- 网域用户是一个直接的参考
- 默认情况下,"网域用户 "还可以创建多达10个计算机账户,这些账户被放在 "网域计算机 "组中。对加入域的计算机有本地管理权限的域用户也可以冒充计算机账户。
请注意:共享权限可以被NTFS权限所推翻。另外,请注意,测试排除了包含以下关键词的共享名称。
print$, prnproc$, printer, netlogon,and sysvol高风险分享
在本报告中,高风险分享被定义为对系统或应用程序提供未经授权的远程访问的分享。默认情况下,这包括以下分享
wwwroot, inetpub, c$, and admin$然而,除此之外,可能还存在没有被叫出来的其他风险。
命令示例
重要提示:所有命令都应该以非特权域用户的身份运行。
.EXAMPLE 1: Run from a domain computer. Performs Active Directory computer discovery by default.
PS C:\temp\test> Invoke-HuntSMBShares -Threads 100 -OutputDirectory c:\temp\test
.EXAMPLE 2: Run from a domain computer with alternative domain credentials. Performs Active Directory computer discovery by default.
PS C:\temp\test> Invoke-HuntSMBShares -Threads 100 -OutputDirectory c:\temp\test -Credentials domain\user
.EXAMPLE 3: Run from a domain computer as current user. Target hosts in a file. One per line.
PS C:\temp\test> Invoke-HuntSMBShares -Threads 100 -OutputDirectory c:\temp\test -HostList c:\temp\hosts.txt
.EXAMPLE 4: Run from a non-domain computer with credential. Performs Active Directory computer discovery by default.
C:\temp\test> runas /netonly /user:domain\user PowerShell.exe
PS C:\temp\test> Import-Module Invoke-HuntSMBShares.ps1
PS C:\temp\test> Invoke-HuntSMBShares -Threads 100 -RunSpaceTimeOut 10 -OutputDirectory c:\folder\ -DomainController 10.1.1.1 -Credential domain\user
===============================================================
PowerHuntShares
===============================================================
This function automates the following tasks:
o Determine current computer's domain
o Enumerate domain computers
o Filter for computers that respond to ping reqeusts
o Filter for computers that have TCP 445 open and accessible
o Enumerate SMB shares
o Enumerate SMB share permissions
o Identify shares with potentially excessive privielges
o Identify shares that provide reads & write access
o Identify shares thare are high risk
o Identify common share owners, names, & directory listings
o Generate creation, last written, & last accessed timelines
o Generate html summary report and detailed csv files
Note: This can take hours to run in large environments.
---------------------------------------------------------------
|||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||||
---------------------------------------------------------------
SHARE DISCOVERY
---------------------------------------------------------------
[*][03/01/2021 09:35] Scan Start
[*][03/01/2021 09:35] Output Directory: c:\temp\smbshares\SmbShareHunt-03012021093504
[*][03/01/2021 09:35] Successful connection to domain controller: dc1.demo.local
[*][03/01/2021 09:35] Performing LDAP query for computers associated with the demo.local domain
[*][03/01/2021 09:35] - 245 computers found
[*][03/01/2021 09:35] Pinging 245 computers
[*][03/01/2021 09:35] - 55 computers responded to ping requests.
[*][03/01/2021 09:35] Checking if TCP Port 445 is open on 55 computers
[*][03/01/2021 09:36] - 49 computers have TCP port 445 open.
[*][03/01/2021 09:36] Getting a list of SMB shares from 49 computers
[*][03/01/2021 09:36] - 217 SMB shares were found.
[*][03/01/2021 09:36] Getting share permissions from 217 SMB shares
[*][03/01/2021 09:37] - 374 share permissions were enumerated.
[*][03/01/2021 09:37] Getting directory listings from 33 SMB shares
[*][03/01/2021 09:37] - Targeting up to 3 nested directory levels
[*][03/01/2021 09:37] - 563 files and folders were enumerated.
[*][03/01/2021 09:37] Identifying potentially excessive share permissions
[*][03/01/2021 09:37] - 33 potentially excessive privileges were found across 12 systems..
[*][03/01/2021 09:37] Scan Complete
---------------------------------------------------------------
SHARE ANALYSIS
---------------------------------------------------------------
[*][03/01/2021 09:37] Analysis Start
[*][03/01/2021 09:37] - 14 shares can be read across 12 systems.
[*][03/01/2021 09:37] - 1 shares can be written to across 1 systems.
[*][03/01/2021 09:37] - 46 shares are considered non-default across 32 systems.
[*][03/01/2021 09:37] - 0 shares are considered high risk across 0 systems
[*][03/01/2021 09:37] - Identified top 5 owners of excessive shares.
[*][03/01/2021 09:37] - Identified top 5 share groups.
[*][03/01/2021 09:37] - Identified top 5 share names.
[*][03/01/2021 09:37] - Identified shares created in last 90 days.
[*][03/01/2021 09:37] - Identified shares accessed in last 90 days.
[*][03/01/2021 09:37] - Identified shares modified in last 90 days.
[*][03/01/2021 09:37] Analysis Complete
---------------------------------------------------------------
SHARE REPORT SUMMARY
---------------------------------------------------------------
[*][03/01/2021 09:37] Domain: demo.local
[*][03/01/2021 09:37] Start time: 03/01/2021 09:35:04
[*][03/01/2021 09:37] End time: 03/01/2021 09:37:27
[*][03/01/2021 09:37] Run time: 00:02:23.2759086
[*][03/01/2021 09:37]
[*][03/01/2021 09:37] COMPUTER SUMMARY
[*][03/01/2021 09:37] - 245 domain computers found.
[*][03/01/2021 09:37] - 55 (22.45%) domain computers responded to ping.
[*][03/01/2021 09:37] - 49 (20.00%) domain computers had TCP port 445 accessible.
[*][03/01/2021 09:37] - 32 (13.06%) domain computers had shares that were non-default.
[*][03/01/2021 09:37] - 12 (4.90%) domain computers had shares with potentially excessive privileges.
[*][03/01/2021 09:37] - 12 (4.90%) domain computers had shares that allowed READ access.
[*][03/01/2021 09:37] - 1 (0.41%) domain computers had shares that allowed WRITE access.
[*][03/01/2021 09:37] - 0 (0.00%) domain computers had shares that are HIGH RISK.
[*][03/01/2021 09:37]
[*][03/01/2021 09:37] SHARE SUMMARY
[*][03/01/2021 09:37] - 217 shares were found. We expect a minimum of 98 shares
[*][03/01/2021 09:37] because 49 systems had open ports and there are typically two default shares.
[*][03/01/2021 09:37] - 46 (21.20%) shares across 32 systems were non-default.
[*][03/01/2021 09:37] - 14 (6.45%) shares across 12 systems are configured with 33 potentially excessive ACLs.
[*][03/01/2021 09:37] - 14 (6.45%) shares across 12 systems allowed READ access.
[*][03/01/2021 09:37] - 1 (0.46%) shares across 1 systems allowed WRITE access.
[*][03/01/2021 09:37] - 0 (0.00%) shares across 0 systems are considered HIGH RISK.
[*][03/01/2021 09:37]
[*][03/01/2021 09:37] SHARE ACL SUMMARY
[*][03/01/2021 09:37] - 374 ACLs were found.
[*][03/01/2021 09:37] - 374 (100.00%) ACLs were associated with non-default shares.
[*][03/01/2021 09:37] - 33 (8.82%) ACLs were found to be potentially excessive.
[*][03/01/2021 09:37] - 32 (8.56%) ACLs were found that allowed READ access.
[*][03/01/2021 09:37] - 1 (0.27%) ACLs were found that allowed WRITE access.
[*][03/01/2021 09:37] - 0 (0.00%) ACLs were found that are associated with HIGH RISK share names.
[*][03/01/2021 09:37]
[*][03/01/2021 09:37] - The 5 most common share names are:
[*][03/01/2021 09:37] - 9 of 14 (64.29%) discovered shares are associated with the top 5 share names.
[*][03/01/2021 09:37] - 4 backup
[*][03/01/2021 09:37] - 2 ssms
[*][03/01/2021 09:37] - 1 test2
[*][03/01/2021 09:37] - 1 test1
[*][03/01/2021 09:37] - 1 users
[*] -----------------------------------------------生成报告
可以生成HTML格式的报告