最新漏洞Goby、Nuclei POC收集——pxplan
作者:Sec-Labs | 发布时间:
项目介绍
PX计划
lv sec收集归纳的POC
项目地址
https://github.com/GREENHAT7/pxplan
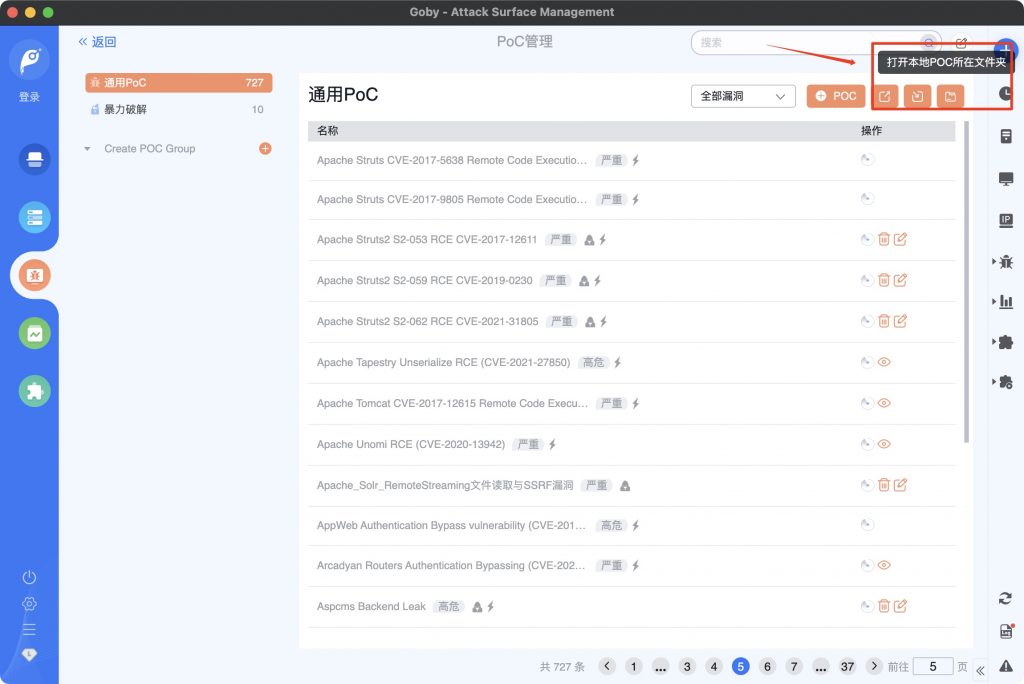
相关漏洞POC展示
-
-
360_Tianqing_database_information_disclosure.json
-
AceNet_AceReporter_Report_component_Arbitrary_file_download.go
-
Active_UC_index.action_RCE.json
-
ACTI_camera_images_File_read.go
-
Adobe_ColdFusion_LFI_CVE-2010-2861.json
-
ADSelfService_Plus_RCE_CVE-2021-40539.json
-
ADSelfService_Plus_RCE_CVE_2021_40539.json
-
Adslr_Enterprise_online_behavior_management_system_Information_leak.json
-
Adslr_Enterprise_online_behavior_management_system_Information_leakage.json
-
Alibaba Nacos 控制台默认弱口令.json
-
Alibaba Nacos 未授权访问漏洞.json
-
alibaba_canal_default_password.json
-
Alibaba_Nacos_Add_user_not_authorized.json
-
Alibaba_Nacos_Default_password.json
-
Ametys_CMS_infoleak_CVE_2022_26159.json
-
Apache ActiveMQ Console控制台弱口令.json
-
Apache Cocoon Xm- 注入 CVE-2020-11991.json
-
Apache Kylin Console 控制台弱口令.json
-
Apache Kylin 未授权配置泄露 CVE-2020-13937.json
-
Apache Solr Log4j JNDI RCE.go
-
Apache Solr任意文件读取漏洞.json
-
Apache_2.4.49_Path_Traversal_CVE_2021_41773.json
-
Apache_2.4.49_RCE_CVE_2021_41773_and_2.4.50_CVE_2021_42013.json
-
Apache_ActiveMQ_Console_Weak_Password.json
-
Apache_ActiveMQ_default_admin_account.json
-
Apache_Airflow_Unauthorized.json
-
Apache_APISIX_Admin_API_Default_Token_CVE_2020_13945.json
-
Apache_APISIX_Dashboard_API_Unauthorized_Access_CVE-2021-45232.json
-
Apache_APISIX_Dashboard_CVE_2021_45232.json
-
Apache_APISIX_Dashboard_RCE_CVE_2021_45232.json
-
Apache_Cocoon_XML_Injection_CVE_2020_11991.json
-
Apache_CouchDB_Remote_Privilege_Escalation_CVE-2017-12635.json
-
Apache_CouchDB_Unauth.json
-
Apache_Druid_Abritrary_File_Read_CVE-2021-36749.json
-
Apache_Druid_Abritrary_File_Read_CVE_2021_36749.json
-
Apache_Druid_Arbitrary_File_Read_CVE_2021_36749.json
-
Apache_Druid_Log4shell_CVE-2021-44228.json
-
Apache_Druid_Log4shell_CVE_2021_44228.json
-
Apache_Dubbo_Admin_Default_Password.json
-
Apache_Flink_CVE_2020_17519.json
-
Apache_HTTP_Server_2.4.48_mod_proxy_SSRF_CVE_2021_40438.json
-
Apache_HTTP_Server_2.4.49_2.4.50_Path_Traversal_CVE_2021_42013.json
-
Apache_HTTP_Server_2.4.49_Path_Traversal_CVE_2021_41773.json
-
Apache_HTTP_Server_2.4.49_RCE_CVE_2021_41773.json
-
Apache_HTTP_Server_Arbitrary_File_Read_CVE_2021_41773.json
-
Apache_HTTP_Server_SSRF_CVE-2021-40438.json
-
Apache_HTTP_Server_SSRF_CVE_2021_40438.json
-
Apache_JSPWiki_Log4shell_CVE-2021-44228_(1).json
-
Apache_JSPWiki_Log4shell_CVE-2021-44228_(2).json
-
Apache_JSPWiki_Log4shell_CVE_2021_44228_1.json
-
Apache_JSPWiki_Log4shell_CVE_2021_44228_2.json
-
Apache_Kylin_Console_Default_password.json
-
Apache_Kylin_Unauthorized_configuration_disclosure.json
-
Apache_OFBiz_Log4shell_CVE-2021-44228.json
-
Apache_OFBiz_Log4shell_CVE_2021_44228.json
-
Apache_ShenYu_Admin_Unauth_Access_CVE_2022_23944.json
-
Apache_SkyWalking_Log4shell_CVE-2021-44228.json
-
Apache_SkyWalking_Log4shell_CVE_2021_44228.json
-
Apache_Solr_Arbitrary_File_Read.json
-
Apache_Solr_Log4j2CVE_2021_44228.json
-
Apache_Solr_RemoteStreaming_File_Read.json
-
Apache_Struts2_S2_053_RCE_CVE_2017_12611.json
-
Apache_Struts2_S2_059_RCE_CVE_2019_0230.json
-
Apache_Struts2_S2_062_RCE_CVE_2021_31805.json
-
Aspcms_Backend_Leak.json
-
AspCMS_commentList.asp_SQLinjection_vulnerability.json
-
Atlassian Jira 信息泄露漏洞 CVE-2020-14181.json
-
Atlassian_Confluence_OGNL_injection_CVE_2021_26084.json
-
Atlassian_Confluence_OGNL_Injection_RCE_CVE_2022_26134.json
-
Atlassian_Confluence_Webwork_OGNL_Inject_CVE_2022_26134.go
-
Atlassian_Jira_Path_Traversal_CVE_2021_26086.json
-
Atlassian_Jira_Seraph_Authentication_bypass_CVE_2022_0540.json
-
Atlassian_Jira_user_information_disclosure.json
-
Atlassian_Jira_user_information_disclosure_CVE_2020_14181.json
-
AVCON6_org_execl_download.action_file_down.json
-
BigAnt_Server_v5.6.06_Path_Traversal_CVE_2022_23347.json
-
BSPHP_index.php_unauthorized_access_information.json
-
Cacti_Weathermap_File_Write.json
-
Casdoor_1.13.0_SQL_InjectionCVE_2022_24124.json
-
chanjet_CRM_get_usedspace.php_sql_injection.json
-
Chanjet_CRM_get_usedspace.php_sql_injection_CNVD_2021_12845.json
-
China_Mobile_Yu_routed_the_login_bypass.json
-
China_Mobile_Yu_Routing_ExportSettings.sh_Info_Leak_CNVD_2020_67110.json
-
China_Mobile_Yu_Routing_Login_Bypass.json
-
China_Mobile_Yu_Routing_Sensitive_Information_Leaks_Vulnerability.json
-
Citrix_unauthenticated_LFI_CVE-2020-8193.json
-
Citrix_Unauthorized_CVE_2020_8193.json
-
ClickHouse_SQLI.json
-
ClusterEngineV4.0_RCE_.json
-
ClusterEngine_V4.0_Shell_cluster_RCE.json
-
CmsEasy_crossall_act.php_SQL_injection_vulnerability.json
-
Coldfusion_LFI_CVE_2010_2861.json
-
Confluence_RCE_CVE_2021_26084.json
-
Consul_Rexec_RCE.json
-
Coremail_configuration_information_disclosure.json
-
Coremail_Config_Disclosure.json
-
CouchCMS_Infoleak_CVE-2018-7662.json
-
Couchdb_Add_User_Not_Authorized_CVE_2017_12635.json
-
Couchdb_Unauth.json
-
Couch_CMS_Infoleak_CVE_2018_7662.json
-
CraftCMS_Seomatic_RCE_CVE_2020_9597.json
-
CraftCMS_SEOmatic_Server-Side_Template_Injection_CVE-2020-9597.json
-
CVE_2018_19367_.json
-
cve_2022_1388_goby.json
-
CVE_2022_22947.json
-
D-Link AC集中管理系统默认弱口令.json
-
D-Link DCS系列监控 CNVD-2020-25078.json
-
D-Link DCS系列监控 账号密码信息泄露漏洞 CNVD-2020-25078.json
-
D-Link_AC_management_system_Default_Password.json
-
D-Link_DCS_2530L_Administrator_password_disclosure_CVE_2020_25078.json
-
D-Link_DIR-850L_Info_Leak.json
-
D-Link_DIR_868L_x_DIR_817LW_Info_Leak_CVE_2019_17506.json
-
D-Link_Info_Leak_CVE-2019-17506.json
-
D-Link_ShareCenter_DNS_320_RCE.json
-
dahua_DSS_Arbitrary_file_download.json
-
dahua_DSS_Arbitrary_file_download_cnvd_2020_61986.go
-
Datang_AC_Default_Password.json
-
DedeCMS_Carbuyaction_FileInclude.json
-
DedeCMS_InfoLeak_CVE-2018-6910.json
-
DedeCMS_InfoLeak_CVE_2018_6910.json
-
Discuz!ML_3.x_RCE_CNVD-2019-22239.json
-
Discuz_ML_3.x_RCE__CNVD_2019_22239.json
-
Discuz_RCE_WOOYUN_2010_080723.json
-
Discuz_v72_SQLI.json
-
Discuz_Wechat_Plugins_Unauth.json
-
Dlink_850L_Info_Leak.json
-
Dlink_Info_Leak_CVE_2019_17506.json
-
Dlink_RCE_CVE_2019_16920.json
-
DocCMS_keyword_SQL_injection_Vulnerability.json
-
Docker_Registry_API_Unauth.json
-
DotCMS_Arbitrary_File_Upload_CVE_2022_26352.json
-
Dubbo_Admin_Default_Password.json
-
D_Link_AC_Centralized_management_system__Default_weak_password.json
-
D_Link_DC_Disclosure_of_account_password_information.json
-
D_Link_Dir_645_getcfg.php_Account_password_disclosure_CVE_2019_17506.go
-
D_Link_DIR_868L_getcfg.php_Account_password_leakage.json
-
D_Link_ShareCenter_DNS_320_RCE.json
-
D_Link_ShareCenter_DNS_320_system_mgr.cgi_RCE.go
-
Elasticsearch_Remote_Code_Execution_CVE_2014_3120.go
-
Elasticsearch_Remote_Code_Execution_CVE_2015_1427.go
-
ESAFENET_DLP_dataimport_RCE.go
-
Eyou_Mail_system_RCE.json
-
Eyou_Mail_System_RCE_CNVD_2021_26422.json
-
F5_BIG_IP_iControl_REST_API_auth_bypass_CVE_2022_1388.json
-
F5_BIG_IP_iControl_REST_Unauthenticated_RCE_CVE_2021_22986.json
-
F5_BIG_IP_login_bypass_CVE_2022_1388.go
-
F5_BIG_IP_RCE_CVE_2021_22986_exp.json
-
fahuo100_sql_injection_CNVD_2021_30193.json
-
Fastmeeting_Arbitrary_File_Read.json
-
FineReport_Directory_traversal.json
-
FineReport_v8.0_Arbitrary_file_read_.json
-
FineReport_v8.0_Fileread_CNVD_2018_04757.json
-
FineReport_v8.0_v9.0_Directory_Traversal.json
-
FineReport_v9_Arbitrary_File_Overwrite.json
-
Finetree_5MP_default_password_or_Unauthorized_user_added.json
-
Finetree_5MP_Network_Camera_Default_Login_unauthorized_user_add.json
-
firewall_Leaked_user_name_and_password.json
-
FLIR_AX8_Arbitrary_File_Download_Vulnerability_CNVD-2021-39018.go
-
ForgeRock_AM_RCE_CVE_2021_35464.go
-
fumengyun AjaxMethod.ashx SQ- injection.json
-
GitLab Graphql邮箱信息泄露漏洞 CVE-2020-26413.json
-
GitLab_Graphql_Email_information_disclosure.json
-
GitLab_Graphql_Email_information_disclosure_CVE_2020_26413.json
-
GitLab_RCE_CVE-2021-22205.json
-
Gitlab_RCE_CVE_2021_22205.json
-
GitLab_SSRF_CVE_2021_22214.json
-
GoCD_Unauthorized_Path_Traversal_CVE_2021_43287.json
-
Grafana_Angularjs_Rendering_XSS_CVE_2021_41174.json
-
Grafana_Arbitrary_file_read.json
-
Grafana_Plugins_Arbitrary_File_Read.json
-
Grafana_v8.x_Arbitrary_File_Read_CVE_2021_43798.json
-
H3C_HG659_lib_File_read.go
-
H3C_IMC_dynamiccontent.properties.xhtm_RCE.go
-
H3C_IMC_RCE.json
-
H3C_Next_generation_firewall_File_read.go
-
H3C_SecPath_Operation_Login_bypass.go
-
H5S_CONSOLE_Video_Platform_GetSrc_Information_Leak_CNVD_2021_25919.json
-
H5S_video_platform_GetSrc_information_leakage.json
-
H5S_video_platform_GetUserInfo_Account_password_leakage.json
-
H5S_Video_Platform_GetUserInfo_Info_Leak_CNVD_2021_35567.json
-
HanWang_Time_Attendance_SQL_injection.go
-
HEJIA_PEMS_SystemLog.cgi_Arbitrary_file_download.go
-
HIKVISION 视频编码设备接入网关 任意文件下载.json
-
HIKVISION.json
-
Hikvision_RCE_CVE_2021_36260.json
-
Hikvision_Unauthenticated_RCE_CVE-2021-36260.json
-
HIKVISION_Video_coding_equipment_Download_any_file.json
-
Hikvision_Video_Encoding_Device_Access_Gateway_Any_File_Download.json
-
Holographic_AI_network_operation_and_maintenance_platform_RCE.go
-
HotelDruid_Hotel_Management_Software_v3.0.3_XSS_CVE_2022_26564.json
-
Hsmedia_Hgateway_Default_account.json
-
Huijietong_cloud_video_fileDownload_File_read.go
-
Huijietong_cloud_video_list_Information_leakage.go
-
IceWarp_WebClient_basic_RCE.json
-
IFW8_Enterprise_router_Password_leakage_.json
-
IFW8_Router_ROM_v4.31_Credential_Discovery_CVE_2019_16313.json
-
IRDM4000_Smart_station_Unauthorized_access.json
-
JEEWMS_Arbitrary_File_Read_Vulnerability.go
-
Jellyfin_10.7.0_Unauthenticated_Abritrary_File_Read_CVE_2021_21402.json
-
Jellyfin_10.7.2_SSRF_CVE-2021-29490.json
-
Jellyfin_Audio_File_read_CVE_2021_21402.go
-
Jellyfin_prior_to_10.7.0_Unauthenticated_Arbitrary_File_Read_CVE_2021_21402.json
-
Jellyfin_SSRF_CVE_2021_29490.json
-
Jetty_WEB_INF_FileRead_CVE_2021_28169.json
-
Jetty_WEB_INF_FileRead_CVE_2021_34429.json
-
JingHe_OA_C6_Default_password.json
-
JingHe_OA_download.asp_File_read.go
-
Jinher_OA_C6_download.jsp_Arbitrary_file_read.json
-
JinHe_OA_C6_Default_password.json
-
JinHe_OA_C6_download.jsp_Arbitrary_fileread.json
-
Jinshan_V8.json
-
Jitong_EWEBS_arbitrary_file_read.json
-
Jitong_EWEBS_Fileread.json
-
Jitong_EWEBS_phpinfo_leak.json
-
JQuery_1.7.2Version_site_foreground_arbitrary_file_download.json
-
JQuery_1.7.2_Filedownload.json
-
KEDACOM_MTS_transcoding_server_Arbitrary_file_download_CNVD_2020_48650.json
-
KEDACOM_MTS_transcoding_server_Fileread_CNVD_2020_48650.json
-
Kingdee_EAS_server_file_Directory_traversal.go
-
Kingsoft_V8_Arbitrary_file_read.json
-
Kingsoft_V8_Default_weak_password.json
-
Kingsoft_V8_Terminal_Security_System_Default_Login_CNVD_2021_32425.json
-
Kingsoft_V8_Terminal_Security_System_Fileread.json
-
Konga_Default_JWT_KEY.json
-
Kyan.json
-
Kyan_Account_password_leak.json
-
Kyan_design_account_password_disclosure.json
-
Kyan_network_monitoring_device_account_password_leak.json
-
Kyan_network_monitoring_device_run.php_RCE.json
-
Kyan_run.php_RCE.json
-
landray_OA_Arbitrary_file_read.json
-
Landray_OA_custom.jsp_Fileread.json
-
LanhaiZuoyue_system_debug.php_RCE.go
-
LanhaiZuoyue_system_download.php_File_read.go
-
Lanproxy 目录遍历漏洞 CVE-2021-3019.json
-
Lanproxy_Arbitrary_File_Read_CVE_2021_3019.json
-
Lanproxy_Directory_traversal_CVE_2021_3019.json
-
Larave- .env 配置文件泄露 CVE-2017-16894.json
-
Laravel.env_configuration_file_leaks(CVE-2017-16894).json
-
Laravel_.env_configuration_file_leaks_CVE_2017_16894.json
-
Leadsec_ACM_infoleak_CNVD-2016-08574.json
-
Leadsec_ACM_information_leakage_CNVD_2016_08574.json
-
Longjing_Technology_BEMS_API_1.21_Remote_Arbitrary_File_Download.go
-
mallgard.json
-
Mallgard_Firewall_Default_Login_CNVD_2020_73282.json
-
Many_network_devices_have_arbitrary_file_downloads.go
-
Many_network_devices_have_password_leaks.go
-
MessageSolution 邮件归档系统EEA 信息泄露漏洞 CNVD-2021-10543.json
-
MessageSolution_EEA_information_disclosure.json
-
MessageSolution_EEA_information_disclosure_CNVD_2021_10543.json
-
Metabase_geojson_Arbitrary_file_reading_CVE_2021_41277.json
-
Metabase_Geojson_Arbitrary_File_Read_CVE-2021-41277.json
-
Metabase_Geojson_Arbitrary_File_Read_CVE_2021_41277.json
-
Microsoft Exchange SSRF漏洞 CVE-2021-26885.json
-
Microsoft_Exchange_Server_SSRF_CVE_2021_26885.json
-
Micro_module_monitoring_system_User_list.php_information_leakage.json
-
MinIO_Browser_API_SSRF_CVE_2021_21287.json
-
MobileIron_Log4shell_CVE-2021-44228.json
-
MobileIron_Log4shell_CVE_2021_44228.json
-
MPSec_ISG1000_Gateway_Filedownload_CNVD_2021_43984.json
-
MPSec_ISG1000_Security_Gateway_Arbitrary_File_Download_Vulnerability.json
-
Node-RED_ui_base_Arbitrary_File_Read_CVE-2021-3223.json
-
Node.js_Path_Traversal_CVE_2017_14849.json
-
Node_RED_ui_base_Arbitrary_File_Read.json
-
Node_red_UI_base_Arbitrary_File_Read_Vulnerability_CVE_2021_3223.go
-
nsoft_EWEBS_casmain.xgi_File_read.go
-
NVS3000_integrated_video_surveillance_platform_is_not_accessible.go
-
OpenSNS_Application_ShareController.class.php__remote_command_execution_vulnerability.json
-
OpenSNS_RCE.json
-
Oracle_Weblogic_LDAP_RCE_CVE_2021_2109.json
-
Oracle_Weblogic_SearchPublicRegistries.jsp_SSRF_CVE_2014_4210.json
-
Oracle_WebLogic_Server_Path_Traversal_CVE_2022_21371.json
-
Oray_Sunlogin_RCE_CNVD_2022_03672_CNVD_2022_10270.json
-
Panabit_Application_Gateway_ajax_top_backstage_RCE.go
-
Panabit_iXCache_ajax_cmd_backstage_RCE.go
-
Panabit_Panalog_cmdhandle.php_backstage_RCE.go
-
php8.1backdoor.json
-
PHP_8.1.0-dev_Zerodium_Backdoor_RCE.json
-
Portainer_Init_Deploy_CVE_2018_19367.json
-
Qilai_OA_CloseMsg.aspx_SQL_injection.go
-
RG_UAC.json
-
Riskscanner_list_SQL_injection.json
-
Ruijie_Networks_EWEB_Network_Management_System_RCE_CNVD_2021_09650.json
-
Ruijie_RG_UAC_Password_leakage_CNVD_2021_14536.json
-
Ruijie_Smartweb_Default_Password_CNVD_2020_56167.json
-
Ruijie_Smartweb_Management_System_Password_Information_Disclosure_CNVD_2021_17369.json
-
Ruijie_smartweb_password_information_disclosure.json
-
Ruijie_smartweb_weak_password.json
-
RuoYi_Druid_Unauthorized_access.json
-
Samsung_WLAN_AP_RCE.json
-
Samsung_WLAN_AP_WEA453e_RCE.json
-
Samsung_WLAN_AP_wea453e_router_RCE.json
-
sangfor_Behavior_perception_system_c.php_RCE.json
-
SDWAN_Smart_Gateway_Default_Password.json
-
SDWAN_smart_gateway_weak_password.json
-
Security_Devices_Hardcoded_Password.json
-
SECWORLD_Next_generation_firewall_pki_file_download_File_read.go
-
Seeyon_OA_A6_DownExcelBeanServlet_User_information_leakage.json
-
Seeyon_OA_A6_initDataAssess.jsp_User_information_leakage.json
-
Seeyon_OA_A6_setextno.jsp_SQL_injection.json
-
Seeyon_OA_A6_test.jsp_SQL_injection.json
-
Seeyon_OA_A6__Disclosure_of_database_sensitive_information.json
-
Seeyon_OA_A8_m_Information_leakage.json
-
Selea_OCR_ANPR_get_file.php_File_read.go
-
Selea_OCR_ANPR_SeleaCamera_File_read.go
-
Shenzhen_West_dieter_Technology_Co_LTD_CPE_WiFi__ping_RCE.go
-
Shenzhen_West_dieter_Technology_Co_LTD_CPE_WiFi__tracert_RCE.go
-
ShiziyuCms_ApiController.class.php_SQL_injection.go
-
ShiziyuCms_ApiController.class.php_SQL_injection.go.json
-
ShiziyuCms_ApigoodsController.class.php_SQL_injection.go
-
ShiziyuCms_ApigoodsController.class.php_SQL_injection.go.json
-
ShiziyuCms_wxapp.php_File_update.go
-
ShopXO_download_Arbitrary_file_read_CNVD_2021_15822.json
-
ShopXO_download_File_read_CNVD_2021_15822.go
-
ShopXO_Fileread_CNVD_2021_15822.json
-
showDocGo.go
-
showDocJson.go
-
shtermQiZhi_Fortress_Arbitrary_User_Login.json
-
Shterm_QiZhi_Fortress_Unauthorized_Access_CNVD_2019_27717.json
-
SonarQube_search_projects_information.json
-
SonarQube_unauth_CVE-2020-27986.json
-
SonarQube_unauth_CVE_2020_27986.json
-
SonicWal- SSL-VPN 远程命令执行漏洞.json
-
Sonicwall_SSLVPN_ShellShock_RCE.json
-
SonicWall_SSL_VPN_RCE.json
-
SPON_IP_network_intercom_broadcast_system_exportrecord.php_any_file_download.go
-
SPON_IP_network_intercom_broadcast_system_getjson.php_Arbitrary_file_read.go
-
SPON_IP_network_intercom_broadcast_system_ping.php_RCE.go
-
SPON_IP_network_intercom_broadcast_system_rj_get_token.php_any_file_read.go
-
Spring_Boot_Actuator_Logview_Path_Traversal_CVE_2021_21234.json
-
Spring_boot_actuator_unauthorized_access.json
-
Spring_Cloud_Function_SpEL_RCE_CVE_2022_22963.json
-
Spring_Cloud_Gateway_Actuator_API_SpEL_Code_Injection_CVE_2022_22947.json
-
Spring_Framework_Data_Binding_Rules_Spring4Shell_RCE_CVE_2022_22965.json
-
Struts2_Log4Shell_CVE-2021-44228_(1).json
-
Struts2_Log4Shell_CVE-2021-44228_(2).json
-
Struts2_Log4Shell_CVE-2021-44228_(3).json
-
Struts2_Log4Shell_CVE_2021_44228_1.json
-
Struts2_Log4Shell_CVE_2021_44228_2.json
-
Struts2_Log4Shell_CVE_2021_44228_3.json
-
TamronOS_IPTV_Arbitrary_file_download.json
-
TamronOS_IPTV_ping_RCE.go
-
TamronOS_IPTV_RCE.json
-
TamronOS_IPTV_system_Filedownload_CNVD_2021_45711.json
-
TamronOS_IPTV_system_RCE.json
-
Tianwen_ERP_system_FileUpload_CNVD_2020_28119.json
-
Tianwen_ERP_system__uploadfile.aspx_Arbitraryvfilevupload.json
-
tongdaoa_unauth.json
-
Tongda_OA_api.ali.php_RCE.go
-
TopSec_Reporter_Arbitrary_file_download_CNVD_2021_41972.go
-
Tuchuang_Library_System_Arbitrary_Reading_File_CNVD_2021_34454.go
-
U8_OA.json
-
Unauthenticated_Multiple_D-Link_Routers_RCE_CVE-2019-16920.json
-
UniFi_Network_Log4shell_CVE-2021-44228.json
-
UniFi_Network_Log4shell_CVE_2021_44228.json
-
VENGD_Arbitrary_File_Upload.json
-
VMWare_Horizon_Log4shell_CVE-2021-44228.json
-
VMWare_Horizon_Log4shell_CVE_2021_44228.json
-
VMware_NSX_Log4shell_CVE-2021-44228.json
-
VMware_NSX_Log4shell_CVE_2021_44228.json
-
VMWare_Operations_vRealize_Operations_Manager_API_SSRF_CVE_2021_21975.json
-
VMware_vCenter_Log4shell_CVE-2021-44228_(1).json
-
VMware_vCenter_Log4shell_CVE_2021_44228_1.json
-
VMware_vCenter_v7.0.2_Arbitrary_File_Read.json
-
VMware_Workspace_ONE_Access_and_Identity_Manager_Server_Side_Template_Injection_CVE_2022_22954.json
-
VMware_Workspace_ONE_Access_RCE_CVE_2022_22954.json
-
WangKang_Next_generation_firewall_router_RCE.go
-
WangKang_NS_ASG_cert_download.php_File_read.go
-
wangyixingyun_waf_Information_leakage.json
-
WAVLINK_WN535G3_POST_XSS_CVE_2022_30489.json
-
Wayos AC集中管理系统默认弱口令 CNVD-2021-00876.json
-
Wayos_AC_Centralized_management_system_Default_Password_CNVD_2021_00876.json
-
Wayos_AC_Centralized_management_system_Default_weak_password.json
-
Weaver_EOffice_Arbitrary_File_Upload_CNVD-2021-49104.json
-
Weaver_EOffice_Arbitrary_File_Upload_CNVD_2021_49104.json
-
Weaver_e_cology_OA_XStream_RCE_CVE_2021_21350.go
-
Weaver_e_office_UploadFile.php_file_upload_CNVD_2021_49104.json
-
Weaver_OA_8_SQL_injection.json
-
weaver_OA_E_Cology_getSqlData_SQL_injection_vulnerability.json
-
Weaver_OA_E_Cology_Workflowservicexml_RCE.go
-
Webgrind_File_read_cve_2018_12909.go
-
Weblogic LDAP Internet RCE CVE-2021-2109.json
-
Weblogic LDAP 远程代码执行漏洞 CVE-2021-2109.json
-
Weblogic SSRF漏洞 CVE-2014-4210.json
-
Weblogic_LDAP_RCE_CVE_2021_2109.json
-
Weblogic_SSRF.json
-
WebSVN_before_2.6.1_Injection_RCE_CVE_2021_32305.json
-
WordPress_Simple_Ajax_Chat_plugin_InfoLeak_CVE_2022_27849.json
-
WordPress_WPQA_plugin_Unauthenticated_Private_Message_Disclosure_CVE_2022_1598.json
-
WSO2_fileupload_CVE_2022_29464.json
-
WSO2_Management_Console_Reflected_XSS_CVE_2022_29548.json
-
WSO2_Management_Console_Unrestricted_Arbitrary_File_Upload_RCE_CVE_2022_29464.json
-
xiaomi_Mi_wiFi_From_File_Read_To_Login_CVE_2019_18370.go
-
Xieda_oa.json
-
Xieda_OA_Filedownload_CNVD_2021_29066.json
-
XXL-JOB 任务调度中心 后台默认弱口令.json
-
XXL_JOB_Default_Login.json
-
XXL_JOB_Default_password.json
-
YAPI_RCE.json
-
YCCMS_XSS.json
-
Yinpeng_Hanming_Video_Conferencing_Filedownload_CNVD_2020_62437.json
-
Yinpeng_Hanming_Video_Conferencing__Arbitrary_file_read.json
-
yiyou__moni_detail.do_Remote_command_execution.json
-
yongyou_NC_bsh.servlet.BshServlet_RCE.json
-
Yonyou_UFIDA_NC_bsh.servlet.BshServlet_rce.json
-
yuanchuangxianfeng_unauthorized_access_vulnerability.json
-
yunshidai_ERP_SQL_injection.json
-
yycms_XSS.json
-
zabbix_saml_cve_2022_23131.json
-
Zhejiang_Dahua_DSS_System_Filedownload_CNVD_2020_61986.json
-
zhihuipingtai_FileDownLoad.aspx_Arbitrary_file_read_vulnerability.json
-
ZhongkeWangwei_Next_generation_firewall_File_read.go
-
ZhongQing_naibo_Education_Cloud_Platform_Information_leakage.go
-
ZhongQing_naibo_Education_Cloud_platform_reset_password.go
-
Zhongxing_F460_web_shell_cmd.gch_RCE.go
-
ZhongXinJingDun_Default_administrator_password.json
-
ZhongXinJingDun_Information_Security_Management_System_Default_Login.json
-
ziguang_editPass.html_SQL_injection_CNVD_2021_41638.json
-
ZZZCMS_parserSearch_RCE.go
-
ZZZCMS_parserSearch_RCE.go.json
-
帆软报表 v8.0 任意文件读取漏洞 CNVD-2018-04757.json
-
来福云SQL注入漏洞.json
-
致远OA A6 数据库敏感信息泄露.json
-
致远OA A6 用户敏感信息泄露.json
-
致远OA webmail.do任意文件下载 CNVD-2020-62422.json
-
蜂网互联 企业级路由器v4.31 密码泄露漏洞 CVE-2019-16313.json
-