网络安全靶场搭建与练习 附攻略和在线版
作者:FancyPig | 发布时间: | 更新时间:
常见web漏洞靶场
DVWA

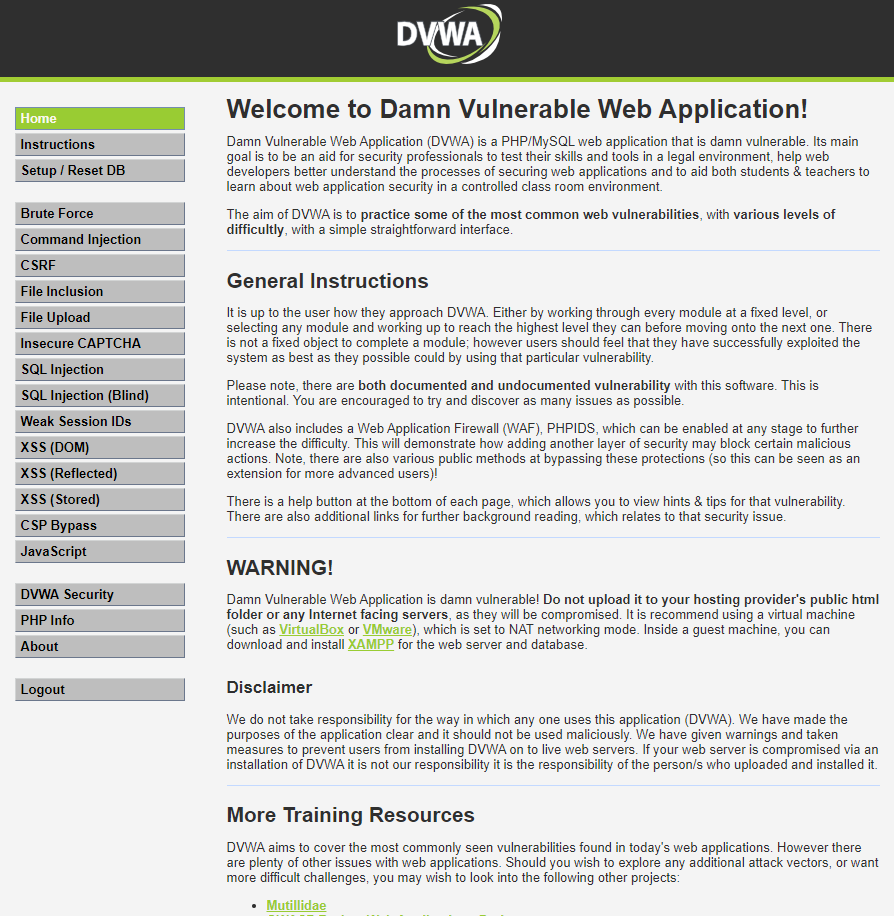
安装过程中需要将config目录下的config.inc.php.dist文件名称修改为config.inc.php,同时配置好里面的数据库
$_DVWA[ 'db_server' ] = '127.0.0.1';
$_DVWA[ 'db_database' ] = 'dvwa';#数据库名称
$_DVWA[ 'db_user' ] = 'dvwa';#数据库用户名
$_DVWA[ 'db_password' ] = 'p@ssw0rd';#数据库密码
$_DVWA[ 'db_port'] = '3306';除此之外,还需要配置好recaptcha密钥接口(里面有一个实验就是针对Google验证码的),这里考虑到很多人都不会注册Google账户,便提供一个自己创建好的。
当然你也可以自己去申请,申请地址https://www.google.com/recaptcha/admin
$_DVWA[ 'recaptcha_public_key' ] = '6LcWNpMaAAAAAJqJcQ7Eea_y_Hh4DpoM-ieBw8ED';
$_DVWA[ 'recaptcha_private_key' ] = '6LcWNpMaAAAAAAwdvSB8szoR-oNW-ZBnpZVFUIlV';数据库都配置好了之后,需要修改你的php.ini配置文件
如果是宝塔面板的话,你可以直接在软件商店>运行环境>php-7.4管理>配置文件里搜索allow_url,然后将Off修改为On
allow_url_include = On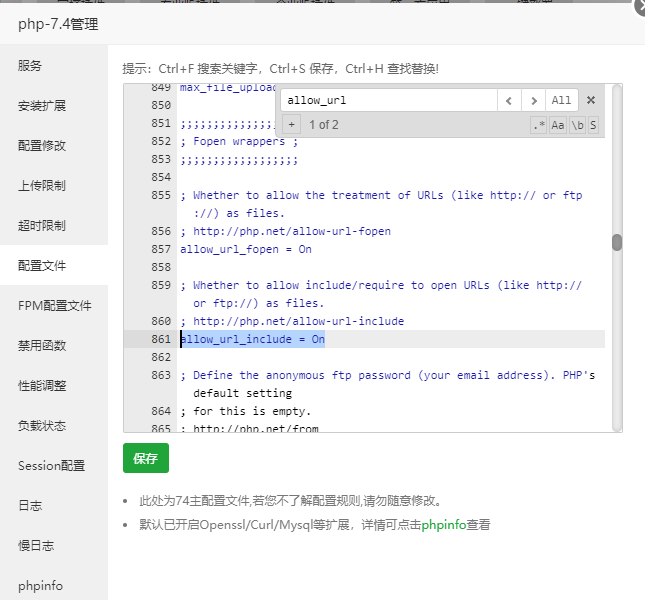
以上操作都完成后,便可进入页面进行安装了

安装完成后默认账户为admin密码为password
视频讲解
学习笔记
靶场攻略之前写过很多了,这里简单做个汇总,欢迎补充!
这里也提供一下来自互联网的内容,如果有需要欢迎参考
在线版来自第三方,随时可能失效
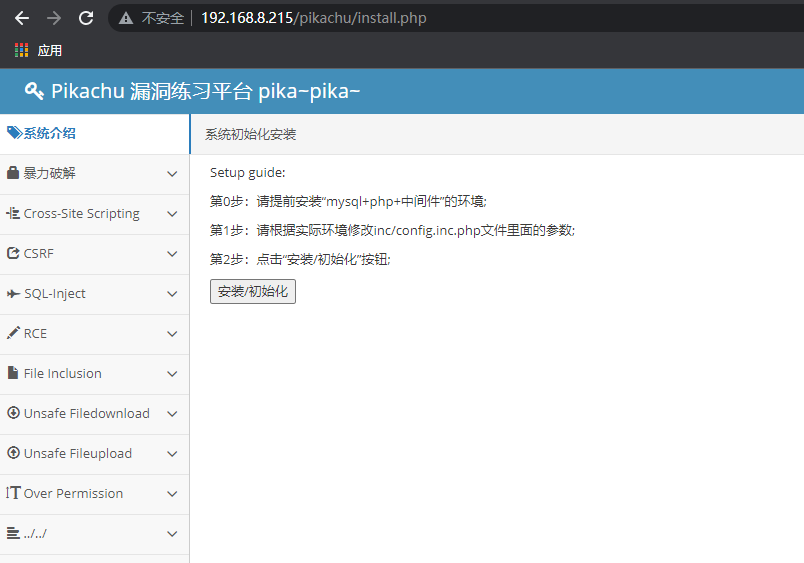
pikachu


在inc目录下修改config.inc.php
//定义数据库连接参数
define('DBHOST', '127.0.0.1');//将localhost或者127.0.0.1修改为数据库服务器的地址
define('DBUSER', 'root');//将root修改为连接mysql的用户名
define('DBPW', '');//将root修改为连接mysql的密码,如果改了还是连接不上,请先手动连接下你的数据库,确保数据库服务没问题在说!
define('DBNAME', 'pikachu');//自定义,建议不修改
define('DBPORT', '3306');//将3306修改为mysql的连接端口,默认tcp3306除此之外还需要修改pkxss/inc目录下的config.inc.php
//定义数据库连接参数
define('DBHOST', 'localhost');//将localhost修改为数据库服务器的地址
define('DBUSER', 'root');//将root修改为连接mysql的用户名
define('DBPW', 'root');//将root修改为连接mysql的密码
define('DBNAME', 'pkxss');//自定义,建议不修改
define('DBPORT', '3306');//将3306修改为mysql的连接端口,默认tcp3306修改完成后,分别进行安装
入口分别为
- install.php
- pkxss/pkxss_install.php

之前只针对其中一部分做过攻略
这里也提供一些来自互联网的内容,如果有需要欢迎参考
Pikachu靶场通关
https://c1everf0x.top/2020/09/18/pikachu%E9%9D%B6%E5%9C%BA%E9%80%9A%E5%85%B3/
在线版
在线版来自第三方,随时可能失效

获取更多同款靶场
使用Fofa获取其他在线靶场方式
https://fofa.so/result?qbase64=ZmlkPSJaa1NvcXRzdmY5ZmNwR25lUlVQSjJ3PT0i
fid="ZkSoqtsvf9fcpGneRUPJ2w=="大概可以搜索到70多条

Sqli_labs


左上角可以选择难度,默认是基础难度,如果你想增加难度可以选择下面的

然后底下的挑战也会随即更换
配置sqli-labs/sql-connections目录下的db-creds.inc
<?php
//give your mysql connection username n password
$dbuser ='数据库账户';
$dbpass ='数据库密码';
$dbname ="数据库名称";
$host = 'localhost';
$dbname1 = "数据库名称1";
?>
然后访问sql-connections/setup-db.php进行安装

这里补充下,由于这个版本非常古老,好像php要用5.4才行哦,当然后面也有人写了适用php7的版本
在线版
在线版可能随时失效
获取更多同款靶场
你可以在fofa中搜索
fid="b8u6q71o2OnTKc/2tT38Fg=="bWAPP


选择要训练的内容

配置bWAPP/admin目录下的settings.php
$db_server = "localhost";
$db_username = "root";#数据库用户名(这里要用root账户创建)
$db_password = "password";#数据库密码
$db_name = "bWAPP";#数据库名称安装页面
入口:bWAPP/install.php

然后点击here进行安装即可,安装完成后你可以自行注册账户
入口:bWAPP/user_new.php
不勾选E-mail activation(因为我们刚才没有配置邮件发送的功能)

uploads-labs


可以说是相当人性化了,而且很方便


上传完即可使用,无需配置数据库
参考互联网内容
Upload-labs 1-21关 靶场通关攻略(全网最全最完整)
https://blog.csdn.net/weixin_47598409/article/details/115050869
upload-labs通关
在线版
在线版来自第三方,随时可能失效
获取更多同款靶场
使用Fofa获取更多靶场
https://fofa.so/result?qbase64=ZmlkPSJMTXJwczdtdlZrL2ZaYnRXeW83ekxBPT0i
fid="LMrps7mvVk/fZbtWyo7zLA=="大概有20多条吧

XSS lab

直接将文件上传网站即可使用,无需安装数据库
参考互联网内容
XSS靶场通关
http://zhuabapa.top/2019/12/10/XSS%E9%9D%B6%E5%9C%BA%E9%80%9A%E5%85%B3/
xss靶场之xss-labs
https://www.cnblogs.com/xiaomeng2333/p/11595786.html
XSS靶场漏洞实践及总结
cve漏洞靶场
vulhub
由于web漏洞靶场相对比较固定,刷完基本上就没什么用了,因此,这里推荐一些cve漏洞靶场供大家学习使用。
这里以centos环境为例,简单讲解一下安装过程。
Vulfocus
Vulfocus 是一个漏洞集成平台,将漏洞环境 docker 镜像,放入即可使用,开箱即用。
特性
- 启动:一键漏洞环境启动,方便简单。
- 自带 Flag 功能:每次启动 flag 都会自动更新,明确漏洞是否利用成功。
- 带有计分功能也可适用于相关安全人员能力的考核。
- 兼容 Vulhub、Vulapps 中所有漏洞镜像。
- 支持可视化编排漏洞环境
快速安装指南
其他靶场
使用Fofa搜索还发现了很多有趣的靶场
- 掌控安全学院实战靶场
http://inject1.lab.aqlab.cn:8005/
http://service.aqlab.cn:8005/
http://kali01.lab.aqlab.cn:8005/
http://service.aqlab.cn:8004/
http://oovw8022.ia.aqlab.cn:8004/
- 掌控封神台