我的电脑文件被打开过?如何溯源定位到黑客?
作者:FancyPig | 发布时间: | 更新时间:
相关阅读
data-postsbox="{"id":25927,"title":"如何判断电脑被入侵?如何通过Volatility分析内存并进行取证?","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/11/20221105071630723.png","cover_video":"","views":2452,"comment_count":8,"category":"knowledge","is_forum_post":false}">{"id":25927,"title":"如何判断电脑被入侵?如何通过Volatility分析内存并进行取证?","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/11/20221105071630723.png","cover_video":"","views":2452,"comment_count":8,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":19131,"title":"一次宝塔面板入侵溯源实战","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/07/20220701012825429.png","cover_video":"","views":4768,"comment_count":10,"category":"cybersecurity","is_forum_post":false}">{"id":19131,"title":"一次宝塔面板入侵溯源实战","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/07/20220701012825429.png","cover_video":"","views":4768,"comment_count":10,"category":"cybersecurity","is_forum_post":false}
data-postsbox="{"id":17378,"title":"如何通过恶意攻击IP溯源","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":10422,"comment_count":1067,"category":"cybersecurity","is_forum_post":false}">{"id":17378,"title":"如何通过恶意攻击IP溯源","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":10422,"comment_count":1067,"category":"cybersecurity","is_forum_post":false}
data-postsbox="{"id":2955,"title":"钓鱼的常见手段,如何防范?如何进行溯源、反制?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":11096,"comment_count":322,"category":"knowledge","is_forum_post":false}">{"id":2955,"title":"钓鱼的常见手段,如何防范?如何进行溯源、反制?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":11096,"comment_count":322,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":2618,"title":"如何隐藏自己的真实IP地址 防止被溯源/恶意钓鱼","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":26290,"comment_count":1167,"category":"cybersecurity","is_forum_post":false}">{"id":2618,"title":"如何隐藏自己的真实IP地址 防止被溯源/恶意钓鱼","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":26290,"comment_count":1167,"category":"cybersecurity","is_forum_post":false}
视频讲解
你是否曾怀疑过自己电脑被黑客控制,再或是自己的电脑文件被黑客浏览过?本期视频我们将带大家通过canary token快速部署一个简单的蜜罐,来捕获这些黑客!
图文讲解
如果你成功找到了远程命令执行(RCE)漏洞,并且可以控制终端,通常情况下你会怎么做呢?
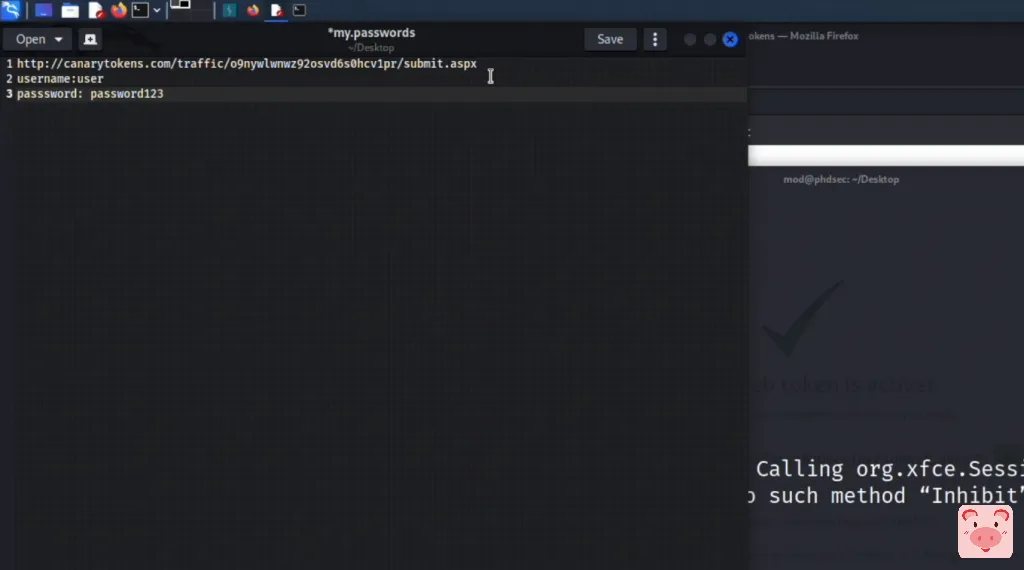
黑客通常情况下,会试图搜索文件里的pass关键词,来尝试找到你记录的账户和密码
grep -r pass
部分黑客找到账户、密码后,会尝试登录站点,看看能不能进一步控制你的资产,那这样的话,我们是不是可以尝试在txt中,设置一个蜜罐,也就是陷阱,让黑客去访问,并进行溯源!
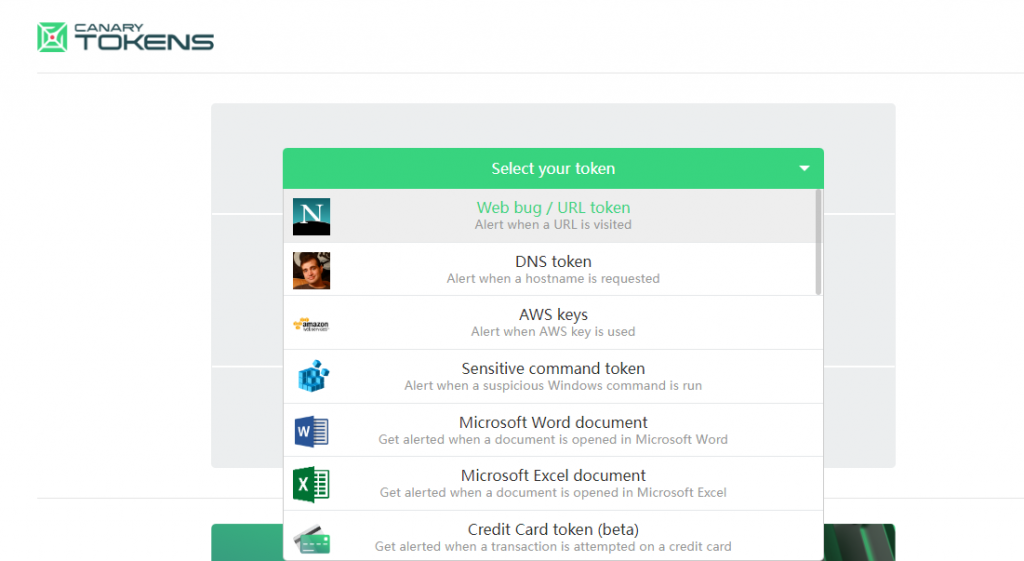
这里我们给大家推荐的是Canary Token的网站

我们可以选择Web bug/URL token,然后填入邮箱,这样一旦有人访问了这个网址,我们就会收到邮件提醒!
按需填写邮箱或者webhook的url以及备注信息

然后,可以生成一个URL

我们可以将其放到我们刚才的txt文件中
但是你可能会觉得这个看起来有些假,网址很长,而且显示了canarytokens,因此,你可以选择后期自定义域名或者使用短网址的方式来优化它。可以在Google上搜索shorten url

缩短我们的URL,得到一个很短的网址
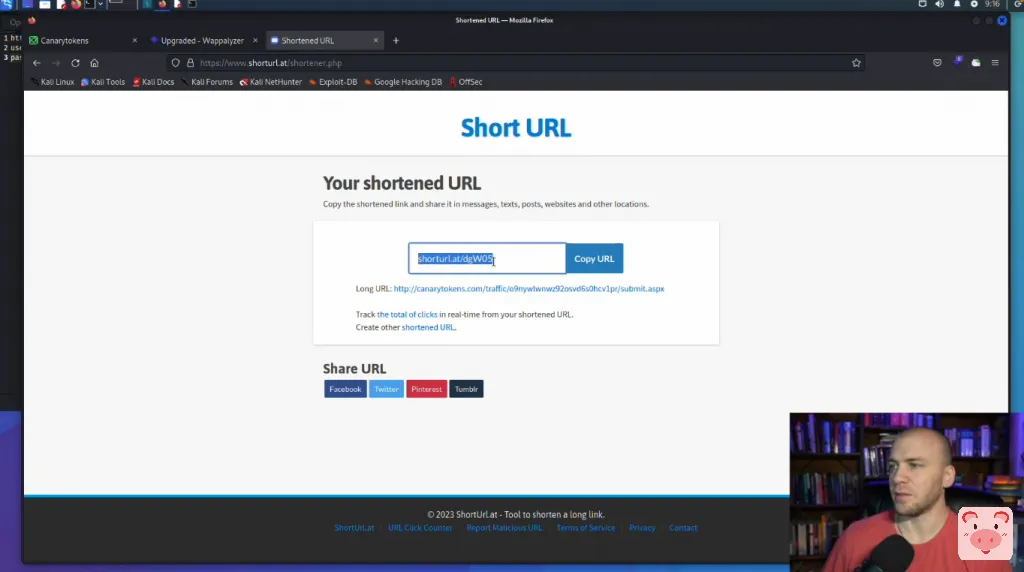
将其填入我们的txt文本中

蜜罐就部署好了,如果有黑客访问了,我们会立刻收到邮件提醒
包括请求方式、时间、源IP地址、使用的客户端等信息,可以一定程度上帮助我们进行溯源。
