SQL注入有多酷?初学者来看看
作者:FancyPig | 发布时间: | 更新时间:
相关阅读
data-postsbox="{"id":21845,"title":"【视频讲解】黑客如何使用SQL注入导出网站的用户信息","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/08/20220813052421504.png","cover_video":"","views":3363,"comment_count":3,"category":"knowledge","is_forum_post":false}">{"id":21845,"title":"【视频讲解】黑客如何使用SQL注入导出网站的用户信息","author":"FancyPig","author_id":1,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/08/20220813052421504.png","cover_video":"","views":3363,"comment_count":3,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":16451,"title":"如何通过SQL注入修改密码登录后台","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3661,"comment_count":7,"category":"knowledge","is_forum_post":false}">{"id":16451,"title":"如何通过SQL注入修改密码登录后台","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3661,"comment_count":7,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":16195,"title":"【零基础学渗透】SQL注入的常见方式汇总","author":"Sec-Labs","author_id":10015,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/05/20220519074409830.png","cover_video":"","views":5639,"comment_count":378,"category":"cybersecurity","is_forum_post":false}">{"id":16195,"title":"【零基础学渗透】SQL注入的常见方式汇总","author":"Sec-Labs","author_id":10015,"cover_image":"https://static.pigsec.cn/wp-content/uploads/2022/05/20220519074409830.png","cover_video":"","views":5639,"comment_count":378,"category":"cybersecurity","is_forum_post":false}
data-postsbox="{"id":1895,"title":"【收藏版】WAF攻防实战笔记","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":6096,"comment_count":18,"category":"cybersecurity","is_forum_post":false}">{"id":1895,"title":"【收藏版】WAF攻防实战笔记","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":6096,"comment_count":18,"category":"cybersecurity","is_forum_post":false}
视频讲解
SQL注入可以干什么?无需输入密码也可以登录?今天我们给大家分享简单的两个技巧,一个是OR,一个是#,通过简单的闭合和注释来绕过登录验证!
图文讲解
我们这里以简单的一个登录框为例,这里如果是最原始的SQL语句写法
我们可以看到是通过验证用户名和密码是否同时为真,最终登陆成功的
SELECT * FROM users WHERE username='admin' AND password='password123'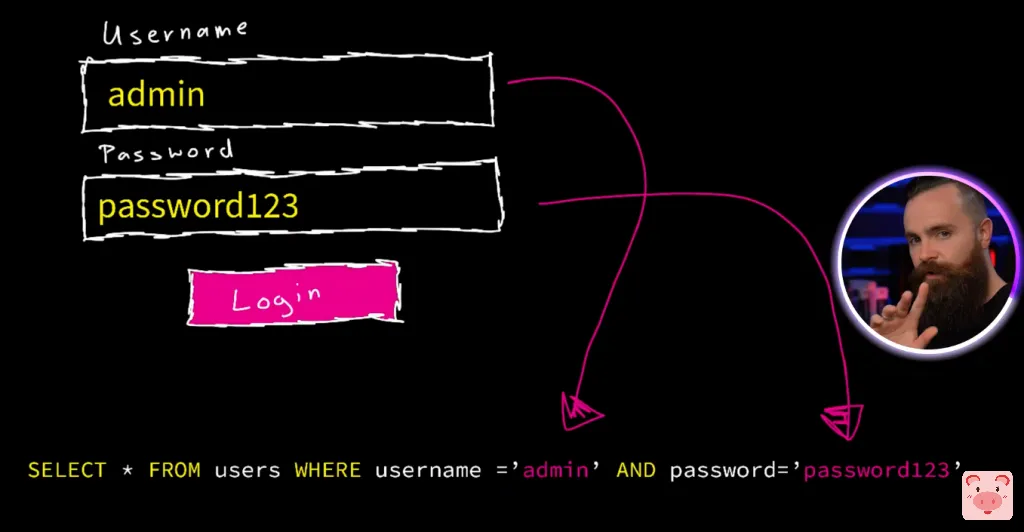
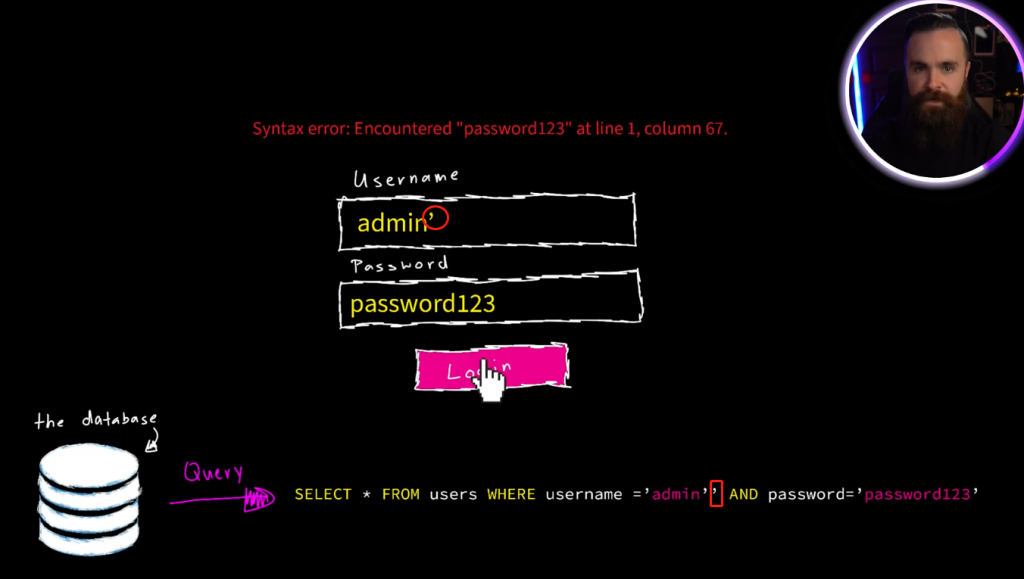
如何检测可能存在以上的注入点?我们可以在用户名后添加一个',查看是否存在SQL语法错误,如果存在,则可以使用下面的方式进行绕过登录!
思路一:'OR 1=1
我们通过'OR 1=1的方式,重新频接语句
我们知道在SQL语句中,语法优先级首先是AND,然后是OR
那可以这么看
username = 'admin' OR '1' = '1' AND password='password123'
实际上的执行顺序是
( username = 'admin' AND password='password123' ) OR '1'='1'
'1'='1'是永真的,OR 永真则这个语句永真,所以不管你用户名、密码咋输入,都能登录成功

思路二:注释绕过
我们在用户名后面添加'--,通过频接语句可以发现,SQL语句变成了
SELECT * FROM users WHERE username ='admin'-- 'AND password='password123'--后面的内容成功被注释掉,因此,只要存在用户名为admin的则可以成功登录!

是不是SQL注入基于报错的方法是否简单,而且非常酷呢?
挑战
您可以访问下面的网站尝试通过上述方法,看看能不能成功完成SQL注入呢?
https://demo.testfire.net/index.jsp