【漏洞赏金侦察课程】如何发现隐藏的子域名&URL
作者:FancyPig | 发布时间: | 更新时间:
相关阅读
data-postsbox="{"id":11160,"title":"【零基础学渗透】主动信息收集","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":9681,"comment_count":485,"category":"cybersecurity","is_forum_post":false}">{"id":11160,"title":"【零基础学渗透】主动信息收集","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":9681,"comment_count":485,"category":"cybersecurity","is_forum_post":false}
data-postsbox="{"id":11003,"title":"【零基础学渗透】被动信息收集","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":13626,"comment_count":853,"category":"cybersecurity","is_forum_post":false}">{"id":11003,"title":"【零基础学渗透】被动信息收集","author":"Sec-Labs","author_id":10015,"cover_image":"","cover_video":"","views":13626,"comment_count":853,"category":"cybersecurity","is_forum_post":false}
视频讲解
通过本视频你将学习到侦察阶段必备的技能,黑客通常不是针对单个页面进行渗透的,在渗透测试前,通常会发现企业或者目标网站攻击暴露面,可以通过sublist3r、amass进行子域名的信息收集,这样可以发现更多功能存在的漏洞……
图文讲解
data-postsbox="{"id":2210,"title":"Kali linux最新版 安装方法以及常见问题解答","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6768,"comment_count":28,"category":"cybersecurity","is_forum_post":false}">{"id":2210,"title":"Kali linux最新版 安装方法以及常见问题解答","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6768,"comment_count":28,"category":"cybersecurity","is_forum_post":false}
我们主要讲解上述视频中提供的2个工具
- sublist3r
- amass
sublist3r(坑比较多,不推荐)
我们这里使用Kali linux安装sublist3r
apt-get install sublist3r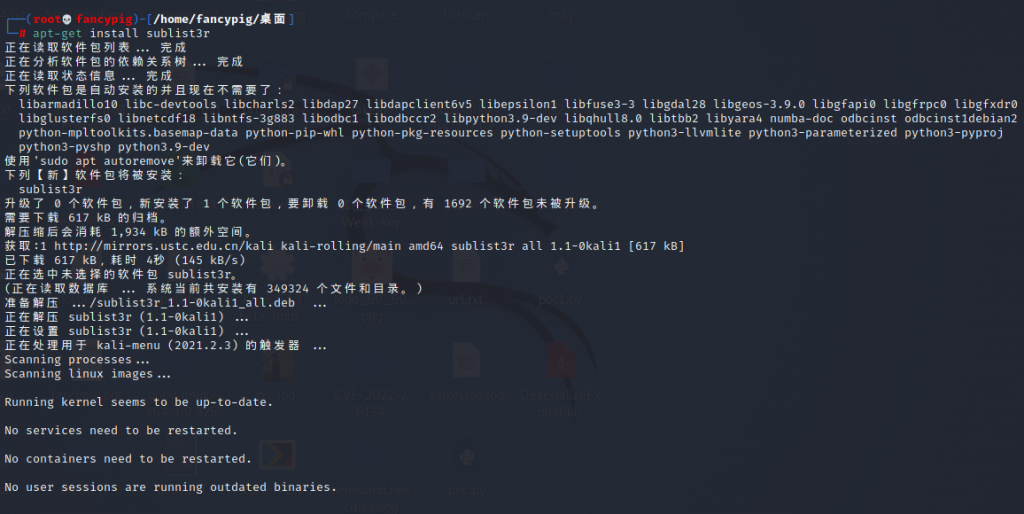
安装完成后就可以进行子域名挖掘了


这里如果使用不了Google服务,可能需要部署clash,可以参考(实际上不影响,这么多搜索引擎足够了)
[postsbox post_id="265"]
当然如果懒得折腾,也可以直接在vultr上临时租用一台海外的服务器做测试,我这里由于使用的是CentOs的,因此我直接从Github上拉取仓库
- 原版(可能有bug)
git clone https://github.com/aboul3la/Sublist3r- 推荐版本(热心网友修改版本)
git clone https://github.com/AetherBreeze/Sublist3r.git然后安装依赖
pip3 install -r requirements.txt然后开始扫描,我们这里以pigsec.cn为例
python3 sublist3r.py -d pigsec.cn

扫描没有结果如何解决?
- CentOS因为是Github上直接下载的,很方便修改
sublist3r.py - Kali linux可以在
/usr/lib/python3/dist-packages/sublist3r.py修改
很多用户反馈扫描有问题,这里大家可以修改sublist3r.py文件
class Virustotal(enumratorBaseThreaded):
def __init__(self, domain, subdomains=None, q=None, silent=False, verbose=True):
subdomains = subdomains or []
base_url = 'https://www.virustotal.com/ui/domains/{domain}/subdomains'
self.engine_name = "Virustotal"
self.q = q
super(Virustotal, self).__init__(base_url, self.engine_name, domain, subdomains, q=q, silent=silent, verbose=verbose)
self.url = self.base_url.format(domain=self.domain)修改为
class Virustotal(enumratorBaseThreaded):
def __init__(self, domain, subdomains=None, q=None, silent=False, verbose=True):
subdomains = subdomains or []
base_url = 'https://www.virustotal.com/ui/domains/{domain}/subdomains?relationships=resolutions'
self.engine_name = "Virustotal"
self.q = q
super(Virustotal, self).__init__(base_url, self.engine_name, domain, subdomains, q=q, silent=silent, verbose=verbose)
self.url = self.base_url.format(domain=self.domain)
# Virustotal requires specific headers to bypass the bot detection:
self.headers["X-Tool"] = "vt-ui-main"
self.headers["X-VT-Anti-Abuse-Header"] = "hm" # as of 1/20/2022, the content of this header doesn't matter, just its presence
self.headers["Accept-Ianguage"] = self.headers["Accept-Language"] # this header being present is required to prevent a captchaamass(强烈推荐)
使用下面的命令即可,-d后面接域名,-passive代表使用被动方式,效率更高。
amass enum -d pigsec.cn -passive